Are the Dominoes Starting to Fall After Historic Bounty of User Credentials Stolen?
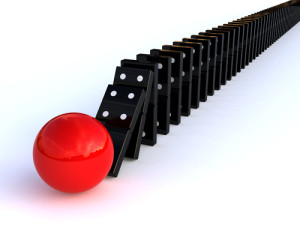
Are the dominoes starting to fall?
When news surfaced last month that over 1.2 billion user credentials were stolen by an organized cybercrime group thought to be operating out of Russia, the dominoes were just starting get to lined up. The founder of Global Digital Forensics, Joe Caruso, talks about the recently reported attack on hosting provider Namecheap and why it should be considered a warning shot across the bow for any business depending on a secure network to function properly.
Harbinger?
It’s been a crazy run on the cyber front in the last couple of weeks, big name banks came forward about being hacked, a slew of celebrities had their private photos exposed for the world to see, and another huge US retailer, Home Depot, is investigating a potentially massive breach which may have exposed the credit card numbers of millions of customers. But on the edge of that cluttered radar, there was a brute force attack on hosting provider Namecheap which didn’t garner as much attention, even though it may have been the first real domino to fall in the aftermath of the biggest compromise of user credentials ever, tallying 1.2 billion plus according to a report in The New York Times last month on August 5th. “IT security departments and professionals should take notice,” says Joe Caruso, founder and CEO/CTO of Global Digital Forensics (GDF), a premier provider of cyber security solutions, ”because this is a show that could be coming soon to a network near you.”
Use a mountain of credentials and see what sticks
According to the security warning published on Namecheap’s website on September 1st, the early stage of their investigation seems to have them convinced the attack they suffered was due to hackers leveraging the massive credentials bounty previously stolen by the Russian group to launch a brute force attack. Software was used to emulate different web browsers like Chrome, Firefox and Safari, allowing attackers to issue repeated login attempts very quickly and burn through any credentials list they may have to see if they can gain access, and with billions of credentials in their arsenal, chances were good at least a few would stick.
Don’t be the next domino to fall victim to avoidable password-based breaches
“The connection to the credentials stolen by the Russian group is certainly not definitive yet,” says Caruso, “and we have not been privy to any details uncovered during their internal investigation to make our own professional determination, but whether or not it was actually the case this time, it is most certainly in the realm of possibility. That’s why businesses should take heed, because attacks like these happen every day, and with that huge collection of credentials already being sold on hacker black market sites, you can bet your bottom dollar others will try the exact same tactic against other targets going forward, tipping domino after domino. The good news is it’s not a complicated fix to avoid being the next domino if approached correctly, and we help clients with these kinds of issues every day.”
In the cyber world like the real world, bad habits can have dire consequences
“Individuals exercising weak password practices, non-existent or subpar password policies and/or enforcement, and simply not being cognizant of the huge threat these mistakes pose are unfortunately all too common occurrences,” says Caruso. “When we do our vulnerability assessments and penetration testing for clients, we uncover all these weak links and help organization’s correct them effectively. I can’t tell you how many times we see ridiculously easy passwords come in when we launch a spear phishing campaign during our penetration testing phase, which is basically us assuming the role of real-world hackers in order to identify weaknesses in the client’s cyber security posture without them suffering the dire consequences a real attack would have, because nine times out of ten, that’s what hackers are after – access. Once they have that, they can do whatever they want, from stealing IP (Intellectual Property), funds or other sensitive ESI (Electronically Stored Information), to malware infections that can grind an entire organization to a screeching halt. And with so many people in the bad habit of using the same credentials for all kinds of different sites, it’s a smoldering cinder just waiting to ignite into a firestorm. We can help clients identify these bad habits internally and correct them. Like Aristotle famously said, “We are what we repeatedly do. Excellence then, is not an act, but a habit.” We always strive to embody that idea in everything we do, and we do everything in our power to help our clients develop and maintain a habit of excellence when it comes to their cyber security. And bad password habits are certainly high on the list of things to tackle when excellence is the objective.”
Customized cyber security solutions that fit any client’s unique needs and budget
*Global Digital Forensics is a recognized industry leader in the fields of computer forensics, cyber security and emergency incident response , with years of experience assisting clients in the government, banking, healthcare, education and corporate arenas. For a free consultation with a Global Digital Forensics specialist, call 1-800-868-8189 about tailoring a cost-effective plan which will meet your unique needs, without wasting resources on solutions you simply don’t need. Emergency responders are also standing by 24/7 to handle intrusion and data breach emergencies whenever and wherever they arise. Time is critical if a cyber incident has occurred, so don’t hesitate to get help. For more information, visit our cyber security page.