GDF provides the vulnerability assessments and penetration testing solutions necessary to maintain compliance with state laws and industry regulations. Our proprietary process is efficient and thorough, providing complete testing and compliance quickly.
We can help you get in compliance with:
- HIPAA (Health Insurance Portability and Accountability Act)
- DFS 23 NYCRR 500 Cyber Security Regulation
- Sarbanes Oxley Act
- Federal Information Security Management Act of 2002 (FISMA)
- Gramm Leach Bliley Act (GLBA)
- Family Educational Rights and Privacy Act (FERPA)
- Payment Card Industry Data Security Standard (PCI-DSS)
- FedRAMP
Some of the main frameworks GDF can help you align with for compliance:
- NIST SP 800-53
- PCI DSS
- ISO 27001/27002
- CIS Critical Security Controls
Timely, Complete Testing and Compliance
GDF employs the latest vulnerability scanning and penetration testing tools and techniques, maintains a Center of Excellence (COE), and conducts all testing through a secure attack center specifically designed for penetration testing.
Our certified penetration testers, CISSPs (Certified Information Systems Security Professionals) and security architects have decades of experience working with organizations of all sizes and in a range of industries, from Fortune 500 companies, to SMBs to independent freelancers.
We have resources and teams available to implement our testing protocols quickly, getting you in full compliance quickly.
Tailored, Targeted Solutions
GDF tailors each engagement to fit your exact requirements and provide all the deliverables needed to fulfill your organization’s regulatory commitments, including the documentation needed to prove your compliance to the proper enforcement agencies.
Don’t risk fines, sanctions, or criminal prosecution because of easily avoidable compliance failures.
To see how we can help you meet your year-end requirements, call GDF at (800) 868-8189 or fill out the form below.
Perhaps you've been targeted. Perhaps you've gotten that anonymous email describing how your computer has been hacked and how the attacker has complete access to your computer, including the internet browser and webcam. The scammer claims to have recorded visits to porn sites and has video recordings of you "using" porn site. Unless you pay, the scammer will send those incriminating and embarrassing video recordings your friends and family, because of course they have access to your contact list. The scammer accepts Bitcoin, thank you, because it's hard to trace, and the sum is typically around $1500 - low enough that many people will pay it without hesitation.
For some perspective, it's estimated that over 14 billion records have been breached since 2013. This treasure trove of personal information, now easily available to sextortion scammers, allows for levels of personalization which help make sextortion threats seem incredibly authentic. And frankly. sextortion is a scary: Someone has access to your webcam and has been watching everything you've been doing...
In the vast majority of cases, the sextrotion threat is empty, but the level of personalization and detail in the threat has reached an entirely new level. If the scammer brings up information like email like phone numbers, addresses, old passwords, Social Security Numbers, or a portion of a personal contact list, the fear and plausibility generated is enough to prompt many people to pay the ransom and not risk any personal or professional embarrassment.
Sextortion scams are typically executed on mass scales. Thousands, sometimes millions of people are targeted. The success rates tend to vary based on the amount of personal information available from the previously stolen/breached records used. As an example, a sextortion scammer would have a goldmine of information from the Ashley Madison breach in 2015, which saw over 300 GB of very personal data stolen, including users' real names, banking data, credit card transactions and even secret sexual fantasies. Not only was it a massive list of individuals who were actively seeking to secretly engage in infidelity, but the intimacy of the information makes the scam seem that more personal.
3 Tips to Help Spot a Sextortion Scam
Most sextortion scams are toothless threats. Here are three indicators that you've nothing to worry about:
- While the scam email will likely contain some type(s) of personal information, there are no details of the site(s) which were allegedly visited.
- The scammer does not include any actual example of the embarrassing “evidence” they claim to possess (if they had it, they most assuredly would use it to close the deal, and probably charge a much heftier premium).
- Urgent requests for payment are usually an indicator the scam was executed on a large scale, increasing the chances of an investigations being launched, so they want to close up shop and disappear as quickly as possible.
11 Ways to Protect Yourself
For all the fear and anxiety caused by a sextortion scam, they are relatively unsophisticated. We've compiled a list of things you can do to protect yourself.
- Copy a string of text out of the scam email and paste it into Google and do a quick search. The results might show you if others have encountered the same scam.
- Never send compromising pictures/video of yourself to anyone. There is always a chance it could be intercepted, become a casualty of a hack to your device or the recipient’s, and sometimes relationships can just go bad, leaving someone you are no longer friendly with or trusting of, who has the ability to compromise you on the most intimate level.
- Do not respond to the email at all, if fact, promptly delete it.
- Never open unsolicited attachments or click links in emails from people you don’t know. Opening an attachment could download malware exposing you to various cyber attacks, and clicking on a link could send you to a malicious site designed to deliver malware or trick you into supplying your personal access credentials.
- Always have current and updated antivirus/anti-malware software active on your computer system or mobile device.
- Use strong passwords (at least 10 characters, the more the better), a mixture of both uppercase and lowercase letters, a mixture of letters and numbers, and at least one special character (e.g., ! @ & $ % # ?) and change them often. You may want to consider getting a password manager to make it easier to use/remember strong and unique passwords.
- Enable two-factor or multifactor authentication whenever possible on your personal accounts.
- Never send money (or gift cards, or Bitcoins, or wire transfers, or currency in any form) to the scammer.
- Consider disconnecting your webcam when not in use, or covering the lens with an opaque cover. Band-aids for small cuts neatly cover the lens of the camera on laptop computers without leaving residue or interfering with opening or closing the device. Better safe than sorry.
- Beware surfing “free” pornography sites, especially from links received in unsolicited emails. Some are designed to deliver malware and/or track your sessions, potentially giving an attacker real information to use against you for blackmail.
- Check if your email has been compromised in a prior data breach. You can click here [https://haveibeenpwned.com/] for a popular site where you can check.
If you think you are the victim of a sextortion scam, you can report it on the BBB Scam Tracker at https://www.bbb.org/scamtracker/us/.
If you think the situation is serious and you need professional help, feel free to contact GDF. We've had experience mitigating many kinds of personal cyber attacks, and we have a process which is effective and discrete.
What happens to your company's security when hackers break into the network at the coffee shop your marketing head frequents?
What happens to your company's security when your sales manager leaves his phone in a taxi?
What happens to your company's security when your vice-president gets divorced and the spouse absconds with a laptop?
The number one cause of cyber security breaches is employee negligence. Combine that with an increasingly mobile workforce, and the potential for disaster becomes frightening.
The security staff at Global Digital Forensics has mitigated hundreds of cyber incidents, and we've helped companies in all sectors establish remote work security policies and practices. Based on all that experience, here are ten steps you can take that will secure your mobile workforce from about 90% of the threats out there.
- Create a Clear Mobile Device Security Policy (and enforce it) - For cybersecurity to work, everyone in an organization has to be on the same page. Cookie cutter policies are not ideal, as every organization has a unique environment and needs. A vulnerability assessment will help to determine specific security concerns, and from that a policy can be crafted. A good security policy is a black and white document, and it should make clear what is acceptable and what is not. Once the policy is created, everyone in the organization needs to thoroughly understand it, and review it at regular intervals. The Mobile Device Security Policy should also be presented to new hires and temp workers. The consequences of unacceptable behavior should also be clearly defined, and enforced.
- Ensure Secure Connections – Communications throughout the network should be encrypted. Remote connections should be made through a Virtual Private Network (VPN), or network hardware that encrypts traffic to and from remote devices. Encrypted VPN connections are one of the best ways to prevent Man-in-the-Middle attacks, which occur when an attacker gets between sources and destinations on the network and intercepts data transmissions.
- Provide Antivirus / Anti-malware Solutions – Every computer with access to the company’s network and data must have anti-virus and anti-malware software installed. There are many software solutions available, and probably one best fits your particular security concerns. Whatever software you use, make the installation mandatory and, of course, make this explicit in your security policies.
- Layer Security and Separate Networks – Mobile devices should be limited to certain areas of the network. This will make it more difficult for an attacker to reach the more important areas of the network and limit the potential damage of an attack. Ideally, there should be totally separate networks for employees and visitors, and even separate networks for different security levels of employees.
- Use the Principle of Least Privilege – Users should only have access to the data and programs they need to do their jobs, and no more. This is a cornerstone of security. It also ensures that if a particular user is compromised by an attacker, through a phishing attack or some other type of social engineering, the attacker will only have access to a limited pool of data. Those with the highest privileges should also have commensurate knowledge about good security practices. Privileges for temp workers and interns should also be very strictly controlled. There is no reason for everyone in a company to have equal access to data on the network.
- Beware of Public Wi-Fi – Wi-Fi networks in coffee shops, airports and the like are a huge security concern. Public Wi-Fi is an easy target for hackers and an easy way for an attacker to get into a computer and install malware. Remote workers with access to privileged data should be issues mobile broadband cards for laptops or mobile data plans for smartphones that can then be used to “tether” a laptop to a more secure mobile network.
- Enforce a Strong Password Policy – The main point of failure in 85% of all hacks is a weak password. You simply must enforce a strong password policy. Strong passwords consist of at least 10 characters (the more the better), a mixture of both uppercase and lowercase letters, a mixture of letters and numbers, and at least one special character (e.g., ! @ & $ % # ?). As strong passwords can be more difficult to remember, there are plenty of reputable secure password library utilities available to help keep them straight and easily available. Using the same password across multiple platforms is also a major vulnerability. If a user has the same password for their Facebook account, Gmail, Amazon, etc., then hacking one account can lead to hacking all accounts, including your company email accounts, online software platforms and more. A strong password policy should be employed and enforced, ensuring only unique, complex passwords are used, and users should be forced to change their passwords at regular intervals.
- Enforce Two Factor / Multi-factor Authentication – Attackers are very sophisticated these days, and a simple username/password combination is not enough. Two-factor and multi-factor authentication tools add steps, such as responding to a text message, which make it much harder for an attacker to gain access. Whether it’s a text, or responding to an email, a fingerprint, voice authorization, or a combination of these, every step that’s added increases security. Find the solution that works for you and make it mandatory for remote access. At the very least, remote workers should have to complete two-factor authentication to get on your company network.
- Ensure Device Security – Mobile devices are easy to steal and easy to lose. One way to help avoid disaster is to enforce strict remote lock and data wipe protection. An organization should have the ability to remotely lock or erase a potentially lost phone, tablet or laptop. For organizationally-issued mobile devices this is easy; for BYOD (Bring Your Own Device) users it can be difficult to separate personal data from work related data. There are workarounds, like setting up two different environments on a device, separating business from personal. The organization can lock their portion and wipe their data, and the user can deal with theirs however they see fit. The best and most secure way to handle this situation is to issue specific devices which are to be used strictly for company business.
- Control Apps and Updates – Mobile applications (apps) are notoriously insecure. They are designed for ease of use, and often security is the last thing on the minds of app developers. Add that to the sheer volume of app choices and it’s no wonder they create security problems. Strict control of apps must be maintained for any device which will be used to access organizational resources, with only apps from an IT pre-approved list allowed. Approved apps and app security protocols should also be spelled out in the mobile device security policy. Keeping applications, operating systems, software and security software updated is also extremely important, as outdated software is one of the most common threat vectors attackers use to compromise networks. Mandatory app checks at regular intervals should be policy. It’s also a good idea to throw in some unannounced spot checks to make sure everyone is staying on their toes.
Remote working is only going to become more common, and cyber crime is showing no signs of abating anytime soon. As the “gig economy” grows, and as technology continues to change the landscape of the workplace, remote workers will increasingly be a security concern. Implementing the items listed above is a good start, but for more ideas, or a comprehensive cyber security assessment, contact GDF at 1-(800) 868-8189.
The Department of Defense (DoD) is serious about significantly improving the cybersecurity posture of everyone involved in the Defense Industrial Base chain. On August 30, 2019, the Cybersecurity Maturity Model Certification (CMMC) draft was published and opened for its public comment period. According to the timeline, CMMC Rev 1 will be issued in January 2020, and will be required in RFPs by the fall of 2020. The CMMC will replace the current system for DFARS certification, which is a self-assessment process without 3rd party auditing.
On the heels of DFARS (learn about DFARS compliance here), the DoD is continuing in its efforts to implement universal cybersecurity standards for the DoD supply chain, to include any entity with which it shares sensitive information, including vendors at the earliest steps of the acquisition process.
The CMMC builds on DFARS and is designed to be “a unified cybersecurity standard for DoD acquisitions to reduce exfiltration of Controlled Unclassified Information (CUI) from the Defense Industrial Base (DIB).” It combines various cybersecurity standards and “best practices,” and maps those practices and processes across several maturity levels that range from basic cyber hygiene to advanced. For a given CMMC level, when the associated practices and processes are implemented, the risk against a certain set of cyber risks will be reduced.
The stated goal of the CMMC is to be, “cost-effective and affordable for small businesses to implement at the lower CMMC levels,” with the intent to have third-party organizations conduct audits and inform risk.
At the top level, the framework covers 18 domains:
- Access Control
- Asset Management
- Awareness and Training
- Audit and Accountability
- Configuration Management
- Cybersecurity Governance
- Identification and Authentication
- Incident Response
- Maintenance
- Media Protection
- Personnel Security
- Physical Protection
- Recovery
- Risk Assessment
- Security Assessment
- Situational Awareness
- System and Communications Protection
- System and Information Integrity
Each domain is assessed based on practices (activities performed at each level) and processes (the level of maturation for each practice). By separating the two, it gives vendors the ability to show they have at least “institutionalized” the necessary processes (have plans, policies and procedures to manage the environment where CUI resides), even if their “practice” score falls a little short at the time of assessment.
Both practices and processes are assessed across five levels, with Level 1 being the most basic level, and Level 5 being the most advanced. Hence, a low level vendor could be certified at level 1. This might be a supplier of components or base materials. Machine shops and job shops might be certified at level 2 or 3. The closer a company is to the final product, the more mature certification required.
Practices and Processes by Maturation Level
| Level | Description of Practices | Description of Processes |
|---|---|---|
| 1 |
|
Practices are performed, at least in ad-hoc manner |
| 2 |
|
Practices are documented |
| 3 |
|
Processes are maintained and followed |
| 4 |
|
Processes are periodically reviewed, properly resourced, and improved across the enterprise |
| 5 |
|
Continuous improvement across the enterprise |
*Table from Draft CMMC Model Rev 4 Release & Request for Feedback – Under Secretary of Defense for Acquisition and Sustainment 8/30/19
Using a uniform level-tiered system streamlines certification in a way that will allow small businesses to focus their efforts and resources (costs, manpower, time, etc.) appropriately.
This fourth draft of the CMMC is now open for public comments (as of August 30, 2019). Comments are due by 5 p.m. September 25, 2019.
The department is looking for feedback on four questions:
- What do you recommend removing or de-prioritizing to simplify the model and why?
- Which elements provide high value to your organization?
- Which practices would you move or cross-reference between levels or domains?
- In preparation for the pending easy-to-use assessment guidance, what recommendations might you have to clarify practices and processes?
But aside from a rare and lucky few, most of us know the holidays can also be a bit like an Allstate commercial, with mayhem always seeming to lurk around the happy moments. Holiday shopping, crowds, sales events, traffic, airport delays, expectations, family political discussions, well - you get the picture – mayhem and stress!
In today’s cyber-entwined society, it’s in this darker side of the holidays where cyber criminals thrive. So much so, your team at Global Digital Forensics (GDF) thinks it’s about time this crazy month gets some attention - a name, a movement for added awareness - so we’re going to chime in with “Cyber December – Holiday Hacking Month.” Remember it, and keep it mind.
While it’s true Black Friday and Cyber Monday happen at the end of November, those two days are like appetizers for the cybercrime world. They’re just cracking their knuckles and warming up, the actual feast comes in December, with the main dish being served between Christmas and New Year’s Day.
It makes perfect sense really, cybercriminals bank on deception, and nothing helps with deception like a little mayhem and chaos to distract you.
When Black Friday and Cyber Monday roll around, you’re still fresh. You’ve still been functioning in normalcy and your guard is up. But then come the distractions, things like the office parties start, the holiday shopping intensifies, and you start seeing bills and shipping statements from strange places. People in the office start taking vacation (and of course they post it on social media so the whole world knows) and someone else who’s in over their head is temporarily filling in, or they do work from outside on unsecure equipment through insecure channels.
By the time the super-spike week between Christmas and New Year’s comes around, everyone in the organization is at their most frazzled and distracted, just waiting for that little break before everything goes back to normal again. You know it, hackers know it, everyone knows it … the question is, are you going to become a victim before it’s over?
The best piece of free advice we can give you is to get and stay FATT for Cyber December (Focus, pay Attention, and Take your Time), because social engineering attempts are running rampant this time of year (phishing, spear phishing, vishing, honeypot drops, promotional scams, impersonation, etc.), and it only takes one successful attack to compromise an entire organization.
But don’t fret, you’re not alone. GDF wishes you and yours only the best the holidays have to offer and a prosperous and joyous New Year! But should you need us any time in Cyber December or beyond, we’re only a phone call away.
Our offices will be closed on Tuesday, December 25, 2018, for Christmas Day and Tuesday, January 1, 2018, for New Year’s Day. But, in the event you do experience a cyber incident, GDF will have Emergency Incident Response Teams on call 24/7 throughout the holiday season to assist with any cyber intrusion or data breach emergency should the unthinkable occur. Simply call us at 1-800-868-8189, and we'll be ready to guide you through it.
Many industries are targeted and breached almost daily, which risks the personal and financial information of their clients and customers. Individuals are also quite susceptible. This is not simply someone else’s problem. Everyone needs to be concerned for their online well-being.
The following graphic outlines some of the complex issues that rack up some $400 billion annually for online crimes. The growing problem also has created a growing job market. Cyber security employment is a continually understaffed field. Degrees like the cyber security programs online at Maryville University help prepare new generations for the struggles ahead.
Effective cyber security today not only takes a coordinated approach, for everything from initial risk assessment to emergency incident response, it also takes having an intimate knowledge of the current cyber threat landscape, which by itself is a full time endeavor, time businesses would rather be spending on what they do best.
Joe Caruso, founder and CEO/CTO of Global Digital Forensics (GDF), a premier national provider of cyber security solutions headquartered in New York City, has been helping businesses deal with cyber threats for over two decades. It’s that real-world experience in a wide variety of industries that led to the unified security solutions GDF offers today, because if there’s one thing he has seen prove itself time and time again, it’s that, “Doing things piecemeal internally inevitably leads to resource mismanagement, miscommunication, excess expenditures and ultimately a weaker security posture.”
Proven Solutions
“The best way to reduce cyber security costs, without sacrificing effectiveness, is to tackle more than one front at the same time,” says Caruso. “Every worthwhile plan needs a starting point, and in the world of cyber security, the starting point has to be assessing the threats you face. Every business is unique, so relying on any type of one-size-fits-all solution is simply destined to fail. Our vulnerability assessments are designed to show you exactly where you stand. We look at the entire digital landscape, from the technology in use and the data needs of the client, to regulatory compliance issues and response policies and procedures. So we’ll not only understand the lay of the land and the entire lifecycle of data from creation to destruction, we’ll also be able to show a client where their resources can most effectively be used, without saddling them with unnecessary bells and whistles which will have no real bearing on their cyber security posture. Once we finish the assessment phase, we move on to the penetration testing phase, assuming the role of a real-world attacker to see if we can break through their security. We’ll do everything from launching realistic spear phishing campaigns, the number one gateway for attackers, to making phone calls posing as support to gather network credentials, which is also a common tactic, as well as attempt to exploit other vectors, like operating system and software applications which have not been updated with the latest security patches. And after we’ve gone through the assessment and testing phases, we’ll know the client’s data environment intimately, allowing us to help our client devise an effective response plan from scratch in none exists, or strengthen any existing response policies and procedures based on what we’ve found.”
The Help Needed to Get Back up after Getting Knocked Down
“The harsh reality is, anyone can become a victim of cyber attackers,” warns Caruso, “from corporate giants, to the watchers themselves like the NSA. The paradigm of cyber security has always favored the attackers because the security side has millions of holes to keep plugged every day, but hackers only need to find one, and it can be new one that’s not even on the radar yet. So it’s not a matter of if, it’s a matter of when, and an organization’s survival will depend on how quickly and effectively they respond. Unfortunately though, many organizations, especially small to medium sized businesses, don’t pursue having a reliable emergency incident response plan in place, mostly citing their lack of time and/or budget constraints. But the truth is, it doesn’t have to be such a costly or time consuming nightmare, and we’ve proven it time and time again. We now even offer no-retainer SLAs (Service Level Agreements) to our assessment and testing clients so they can not only have experienced professional emergency responders on call 24/7 who are already familiar with their digital landscape, but thanks to our network of responders strategically positioned across the country, we can have boots on the ground in hours if necessary, not days, to assist with the response. But many times we can even start the process of identifying, stopping and remediating the attack instantly with remote capabilities. And the best part is, if there is no attack, having us in the wings ready to go won’t cost the client one red cent. Regular vulnerability assessments and testing are not luxuries, they are necessities in today’s digital world, and we can not only cover those bases for clients, but we can help them develop a customized professional response plan and escalation matrix while we’re at it, all based on the insight we will have already gained through the assessment and testing process. So forget the time and money excuses, the right assistance to help you survive a cyber attack is only a phone call away.”
Unified Cyber Security Solutions Save Time, Money and Aggravation
*Global Digital Forensics is a recognized industry leader in the fields of computer forensics, cyber security and emergency incident response, with years of experience assisting clients in the government, banking, healthcare, education and corporate arenas. For a free consultation with a Global Digital Forensics specialist, call 1-800-868-8189 about tailoring a cost-effective plan which will meet your unique needs, without wasting resources on solutions you simply don’t need. Emergency responders are also standing by 24/7 to handle intrusion and data breach emergencies whenever and wherever they arise. Time is critical if a cyber incident has occurred, so don’t hesitate to call 1-800-868-8189 for immediate help. For more information, visit GDF's cyber security page.
In this digital world, it doesn’t take a lot of imagination to predict just how much chaos would ensue in just about any business if control of their electronic world is ripped out of their hands by bad actors. As reported by Forbes on February 18th, that’s exactly what happened to Hollywood Presbyterian Medical Center earlier this month. On February 5th, they became victims of a ransomware attack which affected a broad range of daily activities, even forcing staff to resort to pen and paper record keeping for a while. Eventually, the hospital paid roughly $17,000 (the estimated current value of the 40 Bitcoins demanded) just to get their operations on track. The Forbes article also highlighted some scary numbers on the new “Locky” ransomware variant behind the hospital attack, reporting estimations that it is infecting over 90,000 systems a day.
Joe Caruso, founder and CEO-CTO of Global Digital Forensics (GDF), a premier national provider of cyber security solutions and digital forensics services headquartered in New York City, has seen the aftermath of ransomware attacks many times over the last couple of years. According to him, “Ransomware is probably the fastest growing malware class of today’s cyber threat landscape due to its simplicity and effectiveness. When I first heard about the hospital attack, initial reports put the ransom at around $3.5 million dollars, and you know what, it didn’t even seem farfetched. After all, lives could have hung in the balance if a hospital is involved. And you can bet that ears perked in hacker circles around the world too, getting them to think that if they hit the right target, one heavily reliant on their digital assets, the sky is the limit. Make no mistake about it, the threat from ransomware like Locky, and it's certainly not the only one, is very real and the list of victims is growing fast That’s why we offer solutions which stress the importance of regular threat assessments, testing, enterprise-wide cyber awareness training and effective incident response, because with today’s threats, if those four elements are not working in concert, your business is more than likely going to be in for a rude and costly awakening at some point.”
So how is ransomware delivered?
“As with most of today’s most malicious threats, hackers typically seek out the path of least resistance,” says Caruso, “so they rely on the most fallible aspect of any organization’s cyber security posture, the human element, with the most common way of introducing malware being through a phishing or spear phishing email with an infected attachment, or Driveby attacks launched from visited websites containing malware.”
So how can ransomware be avoided?
“In two words, vigilance and awareness. Automated antivirus and antimalware solutions can do an excellent job stopping a great majority of attacks, but they are not intelligent enough to deal with the social engineering strategies hackers use today to compromise targets. And the key to stopping threats like ransomware is to never receive the payload in the first place. Hacks that make national news, and a majority of big ones that go unreported for obvious reasons, almost always use some type of social engineering, from those phishing and spear phishing emails and Driveby attacks I mentioned, to hand delivering a payload that gets injected via an infected USB stick. Stopping the most advanced and costly threats all starts with understanding what to look for, where the weak links are and how to avoid becoming a victim. That’s what we do for clients with comprehensive cyber threat assessment with a special focus on social engineering methods used by today’s real-world hackers. We’ve done assessments, pen-testing, awareness training and served as emergency incident responders for hundreds of organizations, from companies and corporations recognized around the world, to small and medium sized business in every industry imaginable, so from A to Z, we can customize solutions and plans to fit virtually any situation and budget. We offer free initial consultations where we’ll be happy to discuss your unique needs and lay out a cost-effective plan, so there is no risk and no more excuses. The much bigger risk when it comes to cyber security is doing nothing,” warns Caruso, “because in today’s digital world, that’s a plan which could cost you everything.”
*Global Digital Forensics is a recognized industry leader in the fields of computer forensics services, electronic discovery (eDiscovery), cyber security and emergency incident response, with years of experience assisting clients in the government, banking, healthcare, education and corporate arenas. For a free consultation with a Global Digital Forensics specialist, call 1-800-868-8189 about tailoring a plan which will meet your unique needs. Emergency responders are also standing by 24/7 to handle intrusion and data breach emergencies whenever and wherever they arise. Time is critical if a cyber-incident has occurred, so don’t hesitate to get help. For more information, visit our cyber security page.
With the cyber threat landscape constantly evolving, businesses today need to have a coordinated cyber security plan in place that evolves with it. Global Digital Forensics is now offering unified cyber security solutions, newly updated for 2016, that can help eliminate redundancy and excess costs by streamlining and coordinating the process, while still helping achieve the ultimate goal of having an effective and up-to-date security posture.
Effective cyber security today not only takes a coordinated approach, for everything from initial risk assessment to emergency incident response, it also takes having an intimate knowledge of the current cyber threat landscape, which by itself is a full time endeavor, time businesses would rather be spending on what they do best.
Joe Caruso, founder and CEO/CTO of Global Digital Forensics (GDF), a premier national provider of cyber security solutions headquartered in New York City, has been helping businesses deal with cyber threats for over two decades. It’s that real-world experience in a wide variety of industries that led to the unified security solutions GDF offers today, because if there’s one thing he has seen prove itself time and time again, it’s that, “Doing things piecemeal internally inevitably leads to resource mismanagement, miscommunication, excess expenditures and ultimately a weaker security posture.”
Proven Solutions
“The best way to reduce cyber security costs, without sacrificing effectiveness, is to tackle more than one front at the same time,” says Caruso. “Every worthwhile plan needs a starting point, and in the world of cyber security, the starting point has to be assessing the threats you face. Every business is unique, so relying on any type of one-size-fits-all solution is simply destined to fail. Our vulnerability assessments are designed to show you exactly where you stand. We look at the entire digital landscape, from the technology in use and the data needs of the client, to regulatory compliance issues and response policies and procedures. So we’ll not only understand the lay of the land and the entire lifecycle of data from creation to destruction, we’ll also be able to show a client where their resources can most effectively be used, without saddling them with unnecessary bells and whistles which will have no real bearing on their cyber security posture. Once we finish the assessment phase, we move on to the penetration testing phase, assuming the role of a real-world attacker to see if we can break through their security. We’ll do everything from launching realistic spear phishing campaigns, the number one gateway for attackers, to making phone calls posing as support to gather network credentials, which is also a common tactic, as well as attempt to exploit other vectors, like operating system and software applications which have not been updated with the latest security patches. And after we’ve gone through the assessment and testing phases, we’ll know the client’s data environment intimately, allowing us to help our client devise an effective response plan from scratch in none exists, or strengthen any existing response policies and procedures based on what we’ve found.”
The Help Needed to Get Back up after Getting Knocked Down
“The harsh reality is, anyone can become a victim of cyber attackers,” warns Caruso, “from corporate giants, to the watchers themselves like the NSA. The paradigm of cyber security has always favored the attackers because the security side has millions of holes to keep plugged every day, but hackers only need to find one, and it can be new one that’s not even on the radar yet. So it’s not a matter of if, it’s a matter of when, and an organization’s survival will depend on how quickly and effectively they respond. Unfortunately though, many organizations, especially small to medium sized businesses, don’t pursue having a reliable emergency incident response plan in place, mostly citing their lack of time and/or budget constraints. But the truth is, it doesn’t have to be such a costly or time consuming nightmare, and we’ve proven it time and time again. We now even offer no-retainer SLAs (Service Level Agreements) to our assessment and testing clients so they can not only have experienced professional emergency responders on call 24/7 who are already familiar with their digital landscape, but thanks to our network of responders strategically positioned across the country, we can have boots on the ground in hours if necessary, not days, to assist with the response. But many times we can even start the process of identifying, stopping and remediating the attack instantly with remote capabilities. And the best part is, if there is no attack, having us in the wings ready to go won’t cost the client one red cent. Regular vulnerability assessments and testing are not luxuries, they are necessities in today’s digital world, and we can not only cover those bases for clients, but we can help them develop a customized professional response plan and escalation matrix while we’re at it, all based on the insight we will have already gained through the assessment and testing process. So forget the time and money excuses, the right assistance to help you survive a cyber attack is only a phone call away.”
Unified Cyber Security Solutions Save Time, Money and Aggravation
*Global Digital Forensics is a recognized industry leader in the fields of computer forensics, cyber security and emergency incident response, with years of experience assisting clients in the government, banking, healthcare, education and corporate arenas. For a free consultation with a Global Digital Forensics specialist, call 1-800-868-8189 about tailoring a cost-effective plan which will meet your unique needs, without wasting resources on solutions you simply don’t need. Emergency responders are also standing by 24/7 to handle intrusion and data breach emergencies whenever and wherever they arise. Time is critical if a cyber incident has occurred, so don’t hesitate to call 1-800-868-8189 for immediate help. For more information, visit GDF's cyber security page.
Global Digital Forensics will have emergency incident responders on call 24/7 throughout the holiday season to professionally assist organizations that find themselves the victim of data breaches, intrusions and malware infections, without any costly delays.
It’s that time of year again, the holiday season is in full swing. Unfortunately, that also means hackers will be looking to leverage every ounce of holiday chaos to increase their chances of success when it comes to malware delivery, infiltration, virus infections, cyber espionage and theft.
Time is of the essence when an organization is attacked, with every delay potentially compounding both the effectiveness of the attack, and the cost of remediation. Global Digital Forensics (GDF) will have emergency incident responders on call 24/7 throughout the holiday season to provide professional assistance and remediation expertise quickly, even on those days most cyber security solution providers are closed, like Christmas and New Year.
How do hackers take advantage of the holidays?
Hackers have always heavily relied on deception and misdirection to deliver an initial malware payload which they can then use to open the doors to systems and networks at will, and social engineering, or conning people, routinely plays a big part in making that happen. Phishing and spear phishing emails are a great example. They are a problem year round, disguised as notices requiring action that come from well-known and reputable organizations like Amazon, Paypal, banking institutions or any other organization that large swaths of the population are familiar with and use. But users stand a much better chance of spotting and dismissing them when they don’t make any sense, as they often don’t coincide with that user’s typical behavior. During the holidays though, unusual purchasing and online behavior is the norm. Multiple family members may be making undiscussed purchases with certain shared accounts, a user may not exactly remember the name of every website they visited to find that perfect gift, or because they have been making so many more purchases than they typically do throughout the year with credit and debit cards, ploys for identity theft can seem much more realistic, making those phishing emails about unusual account activity much harder to resist.
Helping hackers bait the hook - Social media, gifts and promotions
Thanks to the ever increasing willingness to “share everything” on social media, hackers can also use information users divulge to customize phishing and spear phishing emails for added effectiveness, like a user posting about the luck they had getting that last Star Wars Sphero BB-8 Droid from Best Buy and then getting a phishing email disguised to look like it’s from Best Buy about a purchase they made. Also be dubious about offers that seem too good to be true, the link about that $50 dollar Microsoft Surface Pro 4 offer will most likely lead to a malicious site and an unwanted payload, but no Surface Pro. Hackers will also use things like “friends lists” to send seasonal eGreetings that look like they come from trusted sources, only to deliver a malicious payload once the target opens it to view the contents. Infected USB sticks designed to look like promotions or gifts are also a hacker favorite, delivering their payload as soon as they are attached to a system by a user. So during the holidays it is more important than ever to stay vigilant and approach everything unexpected or unusual with a healthy degree of doubt.
24/7 Cyber Emergency Incident Response
Businesses are especially vulnerable to cyber attacks during the holidays for all the same reasons mentioned above, but with the prevalence of BYOD (Bring Your Own Device) practices being employed by so many organizations, the possibility of crossover infections has also never been higher. Just one employee making a mistake is all it takes to open the doors of a business network to attackers. In the past that mistake would have had to happen at work, but today, a personal system connecting to the company network, cloud computing, a USB stick used to share data, or even a mobile device like a smartphone or a tablet connecting through WiFi at work can be all it takes. Global Digital Forensics has handled emergency incident response for countless organizations in a wide variety of industries.
Time matters when responding to a cyber emergency
With just one toll free call (1-800-868-8189), GDF can get the response and remediation process started any time of the day or night, even weekends and holidays. With a network of emergency responders strategically positioned nationwide and across the globe, GDF’s response times are unrivaled in the industry. In most cases, GDF can even start the process remotely, employing powerful tools to identify, stop, and remediate the threat, because when it comes to data breaches and other cyber attacks, every second counts. GDF has the proven experience in highly regulated industries as well, so regulatory compliance issues, notification headaches and all the documentation needed to satisfy controllers and anxious clients and/or investors will all be handled the right way, significantly reducing the costs and aftermath of any successful intrusion or attack. So if this joyous holiday season hits a cyber snag, don’t hesitate to call right away, expert responders are standing by.
*Global Digital Forensics is a recognized industry leader in the fields of computer forensics services, electronic discovery (eDiscovery), cyber security and emergency incident response, with years of experience assisting clients in the government, banking, healthcare, education and corporate arenas. For a free consultation with a Global Digital Forensics specialist, call 1-800-868-8189 about tailoring a plan which will meet your unique needs. Emergency responders are also standing by 24/7 to handle intrusion and data breach emergencies whenever and wherever they arise. Time is critical if a cyber-incident has occurred, so don’t hesitate to get help. For more information, visit our breach response page.
On Monday October 26th, Forbes published an article titled Cyber Attacks: 5 Ways Small Businesses Can Protect Themselves. The magnitude of the problem is immense, as they point out with the numbers from a US Small Business Committee survey earlier in the year which concluded that, “71 percent of cyber-attacks occur at businesses with fewer than 100 employees."
While the steps suggested are generally informative, what do they actually mean and what does it really take to start and maintain an effective cyber security posture? Joe Caruso, founder and CEO/CTO of Global Digital Forensics (GDF), a premier national provider of cyber security solutions headquartered in New York City, breaks down the most crucial steps like this:
First step, judging the cyber threat landscape
“One-size-fits-all solutions may be great for many things, but cyber security is absolutely not one of them, because different industries typically face different threats,” says Caruso. “A manufacturing company, for instance, is probably a lot more worried about keeping designs, secret manufacturing techniques and other intellectual property (IP) safe and secure. A restaurant should probably be a lot more concerned about securing their POS (Point of Sale) systems to make sure they are keeping their customers’ credit card information from falling into the wrong hands. Financial industry businesses, on the other hand, have the entire gauntlet of threats to face, from brute-force cyber smash-and-grabs and spear phishing campaigns, to distributed denial of service (DoS) attacks which are launched to incapacitate their websites and make accounts unavailable to their clients, and everything in between. Healthcare, schools and retailers have their own ghosts to face as well. But one thing you can be sure of, if you have cyber “gold” of any kind to mine, there are always attackers with their noses pressed up against the glass just licking their chops for an opportunity to capitalize on any exploitable hole they can find. Our cyber threat assessments are designed to look at the big cyber security picture, from understanding and mapping the entire digital infrastructure and how the data flow interacts with business functions, to determining which threat vectors are likely to be the most problematic and prioritize them accordingly. We also thoroughly review cyber security policies and procedures already in place to identify weaknesses and help clients remediate them, or we help create them if none exist.”
Step two, penetration testing
“The importance of comprehensive penetration testing cannot be overstated. Even though we can always show clients mountains of statistics and pull out countless headline stories about successful cyber attacks and the long term financial ramifications victimized organizations have endured, it still won’t sink in. But run a successful penetration test and eyes will open. It’s the cyber equivalent of a live-fire exercise and just like in the military version,” says Caruso, “it stresses every system with attacks that simulate real-world incidents to identify weaknesses. When we launch one of our realistic phishing or spear phishing campaigns, for instance, and get seventy, eighty or ninety percent of the company’s employees to divulge their credentials, everyone from the employees and managers, to executives and owners get the message loud and clear. Because if it was a real attacker, they would have had complete access to the entire network to do anything they want. And we pull out all the stops with tradecraft honed by two decades of experience. We’ll set up dummy websites which look like the real thing to entice our targets, we’ll employ a variety of social engineering techniques to bypass air gaps on segmented systems and deliver payloads using things like USB sticks, we’ll leverage WiFi and Bluetooth connections from smartphones and tablets which have exploded onto the scene, and a whole host of other proven methods and techniques we have in our arsenal to infiltrate the client’s unique digital architecture. And when you can show someone how they were just victimized and how to avoid it in the future, the lessons stay with them for a very long time. That alone is a huge step towards the ultimate goal of effective cyber security.”
Surviving a cyber emergency is all in the response
“The reality is that playing offense on the cyber battleground is a lot easier than playing defense,” says Caruso. Internal IT security personnel have a million holes to plug, but an attacker only needs to find one to exploit. That’s why GDF has a network of experienced cyber emergency incident responders available 24/7 that are strategically positioned across the country, and the globe. Our responders can be onsite in hours, not days, to identify, isolate, secure and investigate security breaches. We have also developed specialized tools to immediately begin the process remotely in many cases as soon as we receive your call. Not only will taking the right approach to handling a cyber emergency help you contain the actual damage from the attack and the inevitable aftermath, but it will also go a long way towards calming nervous clients, vendors and investors, as well as satisfying many regulatory compliance headaches.”
The dangerous sink or swim world of cyber intrusions, data breaches and other cyber attacks is fluid and constantly evolving. Trusted cyber security professionals like Global Digital Forensics can go a long way towards keeping you afloat. So don’t wait to take control, or you may just become another grim statistic.
*Global Digital Forensics is a recognized industry leader in the fields of computer forensics, electronic discovery (eDiscovery), cyber security and emergency incident response, with years of experience. For a free consultation with a GDF security specialist, call 1-800-868-8189 about tailoring a plan which will meet your unique needs. Emergency responders are also standing by 24/7 to handle intrusion and data breach emergencies whenever and wherever they arise. Time is critical if a cyber incident has occurred, so don’t hesitate to get help. For more information, visit our cyber security page.
On Monday, October 12th, Reuters published a report on the rocketing premiums of cyber insurance, concluding that, “The price of cyber coverage - which helps cover costs like forensic investigations, credit monitoring, legal fees and settlements - varies widely, depending on the strength of a company's security, but the overall trend is sharply up.”
To Joe Caruso, founder and CEO/CTO of Global Digital Forensics (GDF), a premier national provider of cyber security solutions headquartered in New York City, the caveat in that very sentence, “depending on the strength of a company's security,” should be front and center for any business even remotely contemplating cyber insurance, because it is the only controllable factor when trying to negotiate a realistic premium.
IT’S ALL ABOUT RISK
“Just like any type of insurance, premiums always boil down to one thing for insurers – the risk involved. And therein lies the rub," says Caruso. "In our experience assessing cyber threats and risk, far too many businesses really have no idea what threats they may be vulnerable to, or just how vulnerable they are, and honestly, it’s also fairly new ground for the insurance industry. So correctly calculating risk is going to be the first big hurdle that needs to be cleared. Because in the end, a cyber insurance policy is going to have to cover a lot of ground, from direct monetary losses which can be fairly straightforward, to the longer-term-impact things like a tarnished reputation and lost customer trust can have, all of which will be unique to each and every client. They will also have to cover things like business interruption, extortion, sabotage, IP (Intellectual Property) theft, data theft, client exposure, reporting costs and much more. So obviously it is not realistic to expect premiums to come cheap, it’s just not going to happen.”
CYBER RISK INSURANCE DOESN’T REPLACE CYBER SECURITY
“One thing that scares me about cyber insurance is the possibility that it could be seen by some as some kind of magic bullet that makes the need for the time and resources to develop and maintain a fundamentally sound cyber security posture unnecessary, because just like technology itself proves, human nature gravitates towards ease and convenience, and if companies start thinking of cyber risk insurance as an easy and convenient replacement to bonafide and proven cyber security practices because now they’ll be ‘covered’ against losses, some long, dark days are coming,” Caruso warns.
INSURANCE PREMIUMS FOR THE HEALTHY OR THE SICK ARE ALWAYS WORLDS APART
“If a business is even contemplating cyber risk insurance, they better first get all their ducks in a row, especially with the costs for coverage soaring," says Caruso. "Think of it just like health insurance. Someone that is healthy, keeps themselves in great shape by exercising, eating right, avoiding unhealthy habits and getting regular checkups is going to be paying far less in premiums than someone who does not, because obviously the risk chart says the latter is a much greater risk and the chances the insurer will have to make a large payout are exponentially higher. That’s where companies like ours can make a huge difference, not just in helping to drastically reduce an organization’s insurance risk profile and putting a huge dent in premiums, but also in the daily battle against cyber criminals to thwart the vast majority of attacks before they ever happen, and helping clients effectively and efficiently manage the emergency response process if the unthinkable does manage to occur, like an APT (Advanced Persistent Threat) or zero day attack. Our professional vulnerability assessments let clients know exactly where they stand in relation to today’s threat landscape, from weaknesses in policies and procedures based on their business model, operations and unique internal data landscape, to regulatory compliance issues. Then we move on to our proven penetration testing, where we take on the role of real-world black hat hackers to uncover any weaknesses that can be exploited, like susceptibility to social engineering, holes in public facing endpoints, outdated or unpatched systems and networks, internal threats, application security, mistakes in how WiFi networks are managed and how digital devices like smartphones and tablets are being controlled, managed and utilized, and a long list of other potential shortcomings. In the end, we will not only help an organization save money on cyber risk insurance premiums if they decide to go that route, but we will make them much more ready to face today’s cyber threats head on, and quite possibly eliminate the need to ever have to make a claim in the first place. Now that’s smart business.”
PROVEN SOLUTIONS TO DEFEND AGAINST CYBER THREATS
*Global Digital Forensics is a recognized industry leader in the fields of computer forensics, cyber security and emergency incident response, with years of experience assisting clients in the government, banking, healthcare, education and corporate arenas. For a free consultation with a Global Digital Forensics specialist, call 1-800-868-8189 about tailoring a cost-effective plan which will meet your unique needs, without wasting resources on solutions you simply don’t need. Emergency responders are also standing by 24/7 to handle intrusion and data breach emergencies whenever and wherever they arise. Time is critical if a cyber incident has occurred, so don’t hesitate to get help. For more information, visit our cyber security page.
The sixth annual cost of cybercrime study the Ponemon Institute released this week showed some alarming numbers on the growth of cybercrime costs for US companies. The New York Times broke down some of those numbers in this article published on Tuesday, October 6th. With averages showing increases hovering around 20% among the companies surveyed, it only proves that regular threat assessments, penetration testing and emergency incident response have never been more important to the success of an organization in today’s digital world.
The costs to businesses stemming from even one successful data breach can be immense.
“A successful data breach can hit a company on many fronts,” says Joe Caruso, founder and CEO/CTO of Global Digital Forensics (GDF), a premier national provider of cyber security solutions headquartered in New York City. “First there is the cyber espionage factor. Competitors and other corporate enemies may get their hands on valuable intellectual property, like design plans, manufacturing secrets and the like. There is really no limit to the damage which can be caused when a competitor beats you to market with your own ideas, processes and procedures.”
“Then there is the trust factor. Clients, vendors and investors can be a fickle bunch. When you’ve been compromised, they’ve been compromised, and unless you can prove to them you were not sleeping at the wheel and took every measure possible to protect them and their data and quickly identified and thoroughly rectified the problem, they’ll just hop over the fence to that competitor’s pasture, which in their mind must be greener. But with the right approach, you'll find even this fickle bunch are not totally unreasonable regarding the realities of cyber security.”
“Next up of course is cold, hard cash, yours and everyone else that may have trusted you with PII (Personally Identifiable Information), like account numbers, Social Security numbers, or anything else that could help an attacker commit theft and/or fraud, and this certainly does circle the wagons back to the trust issue in a hurry.”
“Then, to wrap it all up with a nice big bow, you’ve also got regulatory agencies to deal with, and the teeth of sanctions and fines they can bring to bear. Add it all together, and the costs can be crippling.”
The big three - assessment, testing and response
“While the costs associated with a successful breach continue rising, the fundamentals needed to help organizations survive the onslaught remain relatively consistent when it comes to surviving a data breach and its aftermath, and we help clients on all those fronts,” says Caruso. “We start with a thorough cyber threat assessment which takes into account a client’s unique needs, digital architecture and data work flow, reviewing policies and procedures, and helping them strengthen them, or create them from scratch if none are present. The threat vectors that are problematic for one industry or organization may not be a high priority for another. Our broad expertise lets us tailor the assessment to illuminate the right problem areas for any client.”
“Next is our comprehensive penetration testing, which is basically us taking the role of real-world hackers and trying to infiltrate the network using a wide variety of tools and techniques, from social engineering strategies, to sophisticated phishing and spear phishing campaigns. We have many tradecraft tricks up our sleeves, just like real hackers do, and so far we have never failed to compromise our target. Our successes will only help to spotlight weakness in the client’s cyber security posture so they can be significantly improved, but a real hacker’s success could cost the client everything.”
“Emergency incident response is next on tap, and is probably the most vital piece of the data breach puzzle. Our extensive experience in network forensics and security, as well as our ‘No Retainer Policy,’ make it both cost-effective and simple to ensure your organization has a response team standing by to handle the problem, mitigate the damage and ensure regulatory compliance, all with absolutely no downside or unnecessary expenses. It just doesn’t get any easier than that to have professional, experienced assistance you can rely on in the event the unthinkable happens. Experienced emergency responders can also help businesses avoid the extremely costly pitfalls of "over-notification" by helping to quickly determine exactly which records were compromised and exactly who should be notified about the event, because as with most things in life, unnecessary excess typically doesn't lead to a happy ending.”
To survive and thrive in the digital arena and reduce the potentially debilitating impact of successful cyber intrusions and data breaches, the decision to take control of cyber security responsibilities and emergency incident response is both crucial and necessary. So don’t wait until it’s too late to get started, call Global Digital Forensics today.
*Global Digital Forensics is a recognized industry leader in the fields of computer forensics, electronic discovery (eDiscovery), cyber security and emergency incident response, with years of experience assisting clients in the government, banking, healthcare, education and corporate arenas. For a free consultation with a Global Digital Forensics specialist, call 1-800-868-8189 about tailoring a plan which will meet your unique needs. Emergency responders are also standing by 24/7 to handle intrusion and data breach emergencies whenever and wherever they arise. Time is critical if a cyber incident has occurred, so don’t hesitate to get help. For more information, visit our cyber security page.
Healthcare IT News published an industry article on Wednesday, September 30th, titled Phishing threats cause sleepless nights for security pros. According to the article, Jennifer Horowitz, Senior Director of Research for HIMSS (Healthcare Information and Management Systems Society) came away from their recent survey of healthcare organizations with the realization that phishing attacks rank number one among cyber security concerns for those tasked with leading the charge to keep organizational and patient data safe.
To Joe Caruso, founder and CEO/CTO of Global Digital Forensics (GDF), a premier national provider of cyber security solutions headquartered in New York City, one of the most troubling things exposed by the survey is that less than a quarter of the organizations said their organizations had tried to improve their readiness with mock phishing exercises.
“Not doing everything humanly possible to get everyone in an organization in tune with the realities and consequences of falling prey to social engineering attacks, like phishing and spear phishing, is a recipe for disaster,” warns Caruso. “And since the most eye opening way to drill the security message home and raise awareness enterprise-wide is to have the staff experience it firsthand, never even bothering with a simulated training attack is pure lunacy, especially for healthcare organizations that are charged with securing data like PHI (Protected Health Information) and other PII (Personally Identifiable Information), which is among the most sought after by cyber criminals.”
Phishing: Preferred by cyber criminals across the globe
“It’s no accident that once most major data breaches are traced back to their origin, a phishing or spear phishing email turns out to be at the root of the breach. Hackers know organizations have been steadily beefing up their technology measures to thwart attackers, but no matter how strong or high the wall, how wide the moat, how advanced the detection system, if they can get just one individual in the organization to take the bait of a well-crafted phishing email, they can have the keys to the castle, and a trusted persona to boot, to just stroll right in through the front gate. Once inside, trying to distinguish an attacker from a trusted insider becomes a nightmare for IT security,” says Caruso, “a nightmare that obviously keeps most of them up at night more than any other threat.”
Combating the threat revolves around testing, awareness and response
“The social engineering aspect of cyber intrusions, which is where spear phishing would fall, is something we focus on heavily when we are called in to do cyber threat assessments and comprehensive penetration testing for clients, and we’ve done it numerous times for healthcare organizations. The scale and scope of the tradecraft we will employ is discussed and agreed upon in advance and then we go to work. Nothing we do will be destructive, but it will definitely be enlightening. We’ll do the same things real-world attackers would do. We’ll use publicly available information and anything else we can get our hands on, online, by telephone, or even in person, and craft a phishing campaign with the personal touches that help attackers make them so hard to spot these days. We’ll do everything from creating full blown dummy websites, to spoofing an individual or department within the organization itself. And so far, we’ve never failed to get a foot in the door,” says Caruso. “When we divulge our findings in our detailed report, it’s got a shock and awe factor that really sinks in deep. It has the powerful, double-barrel effect of exposing weak links in the organization’s cyber security posture, as well as serving as an excellent springboard to raise internal cyber-threat awareness significantly. From there we’ll tailor a remediation plan with the client. If the client chooses, we can even hold awareness seminars to get the entire organization on the same page, from what to look for and how to spot these types of threats, to what to do if a malicious threat is found. And of course we can also satisfy any cyber emergency incident response needs a client may have with our team of experienced cyber responders, strategically positioned across the country and on emergency call 24/7, just in case anyone does take the phishing bait and hands the keys to the castle over to the real bad guys.”
*Global Digital Forensics is a recognized industry leader in the fields of computer forensics, cyber security and emergency incident response, with years of experience assisting clients in the healthcare, banking, education and corporate arenas. For a free consultation with a Global Digital Forensics specialist, call 1-800-868-8189 about tailoring a cost-effective plan which will meet your unique needs, without wasting resources on solutions you simply don’t need. Emergency responders are also standing by 24/7 to handle intrusion and data breach emergencies whenever and wherever they arise. Time is critical if a cyber incident has occurred, so don’t hesitate to get help. For more information, visit our cyber security page.
On Tuesday, September 15th, the SEC’s Office of Compliance Inspections and Examinations (“OCIE”) issued a risk alert as they ramp up their second phase of examinations designed to bolster cyber security in the financial industries. The first phase kicked off in In April 2014, when OCIE published their initial announcement on the program as part of their vision for improving cyber security for the securities and financial markets.
The main topics highlighted in the alert are:
- Governance and Risk Assessment
- Access Rights and Controls
- Data Loss Prevention
- Vendor Management
- Training
“It’s an agenda we’ve been talking about with our clients for years, but it is great that the SEC is formalizing it a bit more for the securities and financial markets, because they are certainly prime targets, not just for “typical” hackers, but also for deep-pocketed and sophisticated players like organized cybercrime rings and nation-state actors,” says Joe Caruso, founder and CEO/CTO of Global Digital Forensics (GDF), a premier national provider of cyber security solutions headquartered in New York City. “But the idea whistles true for every organization plugged into the digital world; every one of those areas needs to be considered, planned for, and implemented post haste.”
It’s not about sophistication, it’s about readiness and constant vigilance
“Most cyber attacks on large institutions, financial and otherwise, aren’t normally quick in-and-out types of scenarios, they are longer term, with initial access being gained sometimes months, or even years in advance of the actual “job” being executed. All it takes is one successful phishing or spear phishing attack on someone on the network, or some clever social engineering to con someone into giving up access information, or even finding a way to get infected physical media plugged into a network device, like leaving an infected USB stick in the lobby or the smoking area and counting on natural human curiosity to do the rest. Everybody has to be up to speed, form vendors to employees, but to find the weak links, it will take a comprehensive cyber threat assessment as the first step, which will not only significantly help identify areas to boost data security, but also go a long way in satisfying examination requirements.”
One size does not fit all
“Every organization’s needs, based on their current strengths and weaknesses, are unique. So the first step is to have a competent and knowledgeable vendor like Global Digital Forensics perform a thorough cyber threat assessment,” says Caruso. “This will give the client a baseline to start with and aid in the decision making process to take the most efficient and cost effective steps to secure organizational cyber assets, from thorough network scans and penetration testing, to social engineering testing and policy, training and procedural review. The most important thing to remember is the cyber threat landscape is highly fluid and always evolving, so resting on yesterday’s laurels is certainly a dangerous and foolhardy approach to take. What may have been a relatively secure cyber environment yesterday could be turned on its ear, for instance, when employees start using their own non-secure devices. Like smartphones and tablets, to increase work efficiency and connectivity. They may be great for boosting production and accessibility, but if they are not considered in the big cyber security picture going forward, it could be just the springboard a hacker needs to get into the network and stay in, just waiting for the right time to strike.”
So don’t wait to become a victim of data exfiltration, identity theft, embezzlement, Denial of Service attacks, cyber warfare, or any one of the myriad of potential threats lurking in the dark places of the cyber realm, take a proactive approach with trained cyber security professionals which fight in the cyber trenches every day, know what’s going on and know how the enemies operate. Pros like the seasoned vets at Global Digital Forensics can help banks and other financial institutions plug the holes before they make headlines for all the wrong reasons, not to mention help in satisfying the tightening regulatory requirements that will only keep getting stricter as time goes on.
*Global Digital Forensics is a recognized industry leader in the fields of computer forensics, cyber security and emergency incident response, with years of experience assisting clients in the government, banking, healthcare, education and corporate arenas. For a free consultation with a Global Digital Forensics specialist, call 1-800-868-8189 about tailoring a cost-effective plan which will meet your unique needs, without wasting resources on solutions you simply don’t need. Emergency responders are also standing by 24/7 to handle intrusion and data breach emergencies whenever and wherever they arise. Time is critical if a cyber incident has occurred, so don’t hesitate to get help. For more information, visit our cyber security page.
Watching a cyber nightmare come to life in the privacy of one’s own home can be quite unsettling, just ask the family in Dayton who could do nothing more than sit back helplessly as a hacker took control over their digital world, as reported this week in TribLIVE on Wednesday, September 2nd. And while it may have made the whole situation that much more jarring to the senses for the family, they should feel lucky that their attacker was brazen enough to reveal their presence.
But just think about what can happen when cyber intruders lay low and don’t reveal themselves after having gained a foothold on a home network. To Joe Caruso, founder and CEO/CTO of Global Digital Forensics (GDF), a premier national provider of cyber security solutions headquartered in New York City, it’s a problem that should bear long and hard consideration by anyone responsible for an organization’s cyber security.
“Danger lurks everywhere in the cyber world,” says Caruso, “and that’s why more time and resources are being spent every year to try and combat the ever growing and evolving problem of cyber threats. But approaching it as an “only at work” issue can be a recipe for disaster. Just think about what happened to this family, they had an intruder not only snooping around their computers and able to steal, manipulate or destroy data at will, but he or she had eyes and ears throughout their home and access to every device connected to their WiFi network - cameras, microphones, everything. Every phone call, every conversation, every visitor in that home could be a source of valuable information which an attacker could leverage. Imagine an attorney discussing a case with a client, privileged information and all, or an insider discussing plans which could drastically affect stock prices in the near future, or sitting on the couch discussing trade secrets with a colleague, or simply accessing the office network from home, the possibilities are endless. It’s also a pretty easy leap to infect a mobile device that an employee uses both at home and the office which could introduce malware to the network at work. The fact is, if every employee is not being well trained and regularly updated on the basics of cyber security, an organization has no one to blame but themselves when the chickens come home to roost.”
“First and foremost, attackers need to find a way to get their foot in the door, and they have two choices,” says Caruso. “Either they can try to wade their way through a tangled web of stiff security measures, or they can find a human patsy to fool into unwittingly giving them the keys to the castle so they can walk right in the front gate. That’s what makes social engineering attacks like phishing and spear phishing campaigns so dangerous for organizations and so preferred by hackers, and without all the security bells at whistles which can often be found these days in the workplace, starting with an employee at home can be a much easier mark. It takes just one bite on the bait and the enemy is in, doing reconnaissance and possibly laying the groundwork for a lateral shift from home to the office.“
“Our vulnerability assessments and penetration testing plans are designed to find weak links in the security chain and solve problems,” says Caruso, “including raising awareness for every employee enterprise wide against social engineering ploys hackers commonly rely on, and uncover any existing and/or resident threats and thoroughly eradicate them. From proactive solutions to help thwart today’s cyber threats, to a proven track record as emergency incident responders, we certainly have plenty of experience helping all kinds of clients navigate not only the dangerous cyber threat landscape they face on a daily basis, but all the potential pitfalls and headaches that can arise should the unthinkable happen and a breach is successful. We can customize solutions to fit any client’s real needs, it’s just a matter of picking up the phone to get the ball rolling – with sooner being far better than later when it comes to combatting cyber threats.”
*Global Digital Forensics is a recognized industry leader in the fields of computer forensics, cyber security and emergency incident response, with years of experience assisting clients in the government, banking, healthcare, education and corporate arenas. For a free consultation with a Global Digital Forensics specialist, call 1-800-868-8189 about tailoring a cost-effective plan which will meet your unique needs, without wasting resources on solutions you simply don’t need. Emergency responders are also standing by 24/7 to handle intrusion and data breach emergencies whenever and wherever they arise. Time is critical if a cyber incident has occurred, so don’t hesitate to get help. For more information, visit out cyber security page.
Next weekend is Labor Day weekend, the last bash of the season and the unofficial end of summer (which astronomically, officially ends on September 22nd this year). For IT security personnel, it should also mark the perfect time to make sure no summer-induced cyber security hangovers linger on which could prove far more costly than a simple headache.
Joe Caruso, founder and CEO-CTO of Global Digital Forensics (GDF), a premier national provider of cyber security solutions and digital forensics services headquartered in New York City, has been fighting on the front lines of the cyber security battlefield for over two decades, and has seen many times what summer security breakdowns can turn into. “Hackers thrive on chaos and confusion, and summertime often tends to be loaded with both.”
Even the best of intentions can lead to trouble
“A client may have great cyber security policies and procedures in place with everyone humming along doing exactly what they should be doing in their realm of responsibility, but then someone goes on vacation and their responsibilities get shuffled temporarily to someone else who may not be as in tune with what needs to be done and how,” says Caruso, “or something happens like there’s a password they forgot to pass along before they left. So the person filling in innocently emails or texts John while he’s on vacation to find out what it is. It’s all very innocent, but then John answers, using a free Wi-Fi spot in the hotel which a hacker is using to intercept messages and install malware on his mobile device. Just like that the password is compromised, John’s device is infected with malware he has no idea about, which will quite possibly make the jump to business network when he returns to work, and an attacker has their foot in the door in two ways in one fell swoop. Now think about seasonal personnel that were granted access and are now leaving, or how much sense those summer phishing emails could make to an employee from attackers pretending to be from hotels or travel agents or restaurants or any one of a million other places that would seem out of the ordinary almost any other time of the year. All it takes is one person to fall for it one time for an intruder to gain access. Summer vacation time is supposed to leave you refreshed and reinvigorated, not put the entire organization behind the eight ball heading into the busy season.”
The time is now
“So it should be obvious that right now is a perfect time to schedule a professional vulnerability assessment and penetration test so your organization can put the summer in the rear-view mirror with a clean slate going forward. We can help make sure there are no resident threats in play with state-of-the-art deep scanning, we can analyze a client’s unique environment to determine what cyber threats they are most susceptible to, we can review security policies and procedures to make sure they are all up-to-date and effective, and we can perform penetration testing, which is letting the good guys, us, try to infiltrate a system just like the bad guys would, with extra focus on social engineering attempts like spear phishing campaigns as well. We can also often orchestrate the whole thing from our GDF Attack Center to make the whole process less intrusive and/or disruptive, and let’s just say our success rate is often quite eye-opening. With the free consultation we are currently offering, we eliminate a lot guesswork for the client and can get right to the heart of what’s needed, because our experts are trained to know just what to ask to find out what exactly is needed to achieve the most beneficial results. So don’t get stuck with the blues from summertime when a clean slate is just a phone call away.”
*Global Digital Forensics is a recognized industry leader in the fields of computer forensics, cyber security and emergency incident response, with years of experience assisting clients in the government, banking, healthcare, education and corporate arenas. For a free consultation with a Global Digital Forensics specialist, call 1-800-868-8189 about tailoring a cost-effective plan which will meet your unique needs, without wasting resources on solutions you simply don’t need. Emergency responders are also standing by 24/7 to handle intrusion and data breach emergencies whenever and wherever they arise. Time is critical if a cyber incident has occurred, so don’t hesitate to get help. For more information, visit our cyber security page.
In a world where professional and personal lifestyles are so interconnected with technology, it should come as no surprise that digital evidence can often become the game-changer when the truth about exactly what happened is being sought, and whether it’s a presidential candidate, a criminal or just a suspect employee who had access to sensitive business information, the tales data can tell can and do change futures every day. And as reported in The Washington Post in this article published on Thursday, August 20th, “A federal judge told lawyers for the State Department on Thursday that they should 'establish a dialogue' with the FBI to learn whether federal records remain on Hillary Rodham Clinton’s e-mail server.” For better or for worse for Hillary Clinton, digital forensics experts are on the clock, and the world is watching.
Welcome to the sometimes high stakes world of digital evidence, a world very familiar to Joe Caruso, founder and CEO/CTO of Global Digital Forensics (GDF), a premier national provider of electronic discovery (eDiscovery) and digital forensics solutions headquartered in New York City, who says, “When it comes to digital evidence, especially correspondence, there are many things about the unique situation that need to be considered, but it all starts with correctly dealing with the identification, acquisition, analysis and production of digital evidence, or eDiscovery (Electronic Discovery), in a proper, documented, repeatable and defensible manner. There are no shortcuts, especially if even the possibility of future legal action is part of the equation, for businesses and presidential candidates alike.”
“There are so many things digital forensics analyses can tell us,” says Caruso, “from finding a smoking gun in black and white, like if the FBI were to find an email or emails actually marked classified in this case, to the actions which may have been taken by a user to cover their tracks, because sometimes what’s not there can tell a whole story on its own. For instance, there are plenty of utilities available that allow a user to 'wipe' a drive so deleted data is overwritten on the media to render it irrecoverable, but those kinds of things leave trails of their own. We can often find out when a wiping utility was installed, when and how often it was executed and what user profile was active at the time. We can also often access certain system log records which are untouched by the wiping process that can lend valuable insight into what transpired. Sometimes there can be file fragments left which can be recovered, there can be traces left on cloud storage or webmail accounts, and remember, when it comes to email there is a sender and a recipient, so sometimes the other side of the 'conversation' can yield treasures too, you just have to have the experience and expertise to know how to find and follow the breadcrumbs the right way. We can also authenticate emails to verify nothing shady went on, like someone trying to plant bogus emails to incriminate someone, and much more.”
When digital evidence goes beyond email
Global Digital Forensics is a formidable ally when it comes to the identification, acquisition, analysis, production and expert testimony relating to electronic evidence, always using only industry proven and accepted methods and procedures so any evidence found remains pristine and admissible. GDF’s experience and savvy in dealing with some of the most complex ESI situations imaginable and unrivaled expertise during those initial and crucial tone-setting steps, like the meet and confer or discovery conference, will ensure the best chance for litigation success. Because with Global Digital Forensics on the job, those are opportunities to seize an early advantage, not a burden to be endured. And because Global Digital Forensics is highly experienced in virtually any type of digital media, should the trail lead to networks, smartphones, tablets, mainframes, webmail or even social networking sites, GDF can seamlessly transition to help clients find and make the most out of virtually any type of electronic evidence involved, wherever it resides.
*Global Digital Forensics is a recognized leader in the fields of computer forensics, eDiscovery, cyber security and emergency incident response. To speak with a digital evidence specialist about your unique situation, or any other computer forensics, eDiscovery or cyber security needs involving Electronically Stored Information (ESI), call 1-800-868-8189 anytime 24/7, the call and the initial consultation are free.
Forbes published an article on Wednesday, August 12th, called 6 Observations About Cybersecurity Based On Two New Surveys. Between the PricewaterhouseCooper (PwC) and Black Hat surveys, roughly one thousand executives participated. One of the most telling, and scary, statistics was that a full half of those surveyed don’t conduct periodic cyber security awareness and training programs, or cyber security training for new employees. With almost 80% of those surveyed saying they’ve experienced an incident/attack in the last 12 months, it only makes sense that the first impulse is to turn to technology solutions. But that still leaves the biggest culprit, and the most fallible when it comes to strong cyber security, largely unchecked – the human element.
In the cyber world, hackers looking to land a white whale often start with one little phish
“This should serve as a serious wake up call,” says Joe Caruso, founder and head of Global Digital Forensics (GDF), a premier national provider of cyber security solutions and digital forensics services headquartered in New York City, “because raising social engineering awareness enterprise wide is probably the most important thing an organization can do to secure their ESI (Electronically Stored Information) and other digital assets. Just about everyone has antivirus solutions running to stop many threats, and many organizations have personnel or vendors at least trying to hold the fort, so a majority of threats are actually thwarted. But the nasty ones, the ones that make punchlines of globally recognized companies and cause smaller business to close up shop every day, a vast majority of those all started with social engineering, typically in the form of phishing or spear phishing emails. And recently, boiler room operations that combine old-school phone rooms with evolving cyber attack techniques have been getting increasing play as well. But if everyone in an organization isn’t up to speed on what to watch out for on the social engineering front, and taught ways to better secure themselves, and by extension the organization, it’s all for naught.”
Professional help from those in the know
“We’ve been in the cyber security game for a long time,” Caruso says. “We know what hackers have done in the past, and how they are evolving today. That’s why we designed our vulnerability assessments and penetration testing with a strong focus on social engineering. We’ll of course identify and help rectify any technology, policy or procedural weaknesses, but we’ll also go the extra step of designing a full scale social engineering attack. We like to use phishing and spear phishing campaigns the most, because they are the vectors that compromise the most networks. When hackers get their hands on the master keys to the network, the sky is the limit for them, and exactly the opposite for the victim. We take great pride in never having failed to breach a network we’ve been hired to test. And we take just as much pride in watching the lessons they learn through the results of the assessment and testing process make them much stronger on their cyber security front going forward. And if a client wishes, we can help in other ways on the training front too.”
*Global Digital Forensics is a recognized industry leader in the fields of computer forensics, cyber security and emergency incident response, with years of experience assisting clients in the government, banking, healthcare, education and corporate arenas. For a free consultation with a Global Digital Forensics specialist, call 1-800-868-8189 about tailoring a cost-effective plan which will meet your unique needs, without wasting resources on solutions you simply don’t need. Emergency responders are also standing by 24/7 to handle intrusion and data breach emergencies whenever and wherever they arise. Time is critical if a cyber incident has occurred, so don’t hesitate to get help. For more information, visit www.evestigate.com.
There is one thing the Black Hat Conference always seems to accomplish; every year there is some kind of wow moment that captures national interest. This year, the Internet of Things (IoT) certainly made the spotlight. As reported by ABC News on Thursday, August 6th, all eyes were on car hacking after a hackers were able to take control of certain functions in a Jeep, including transmission and braking, from miles away.
“Those are the kinds of reports that open eyes to the realities that are out there on the cyber front,” says Joe Caruso, founder and head of Global Digital Forensics (GDF), a premier national provider of cyber security solutions and digital forensics services headquartered in New York City, “shock value always helps things sink in.”
“It’s not some distant future world we’re talking about, it’s unfolding today,” says Caruso. “And it’s not just Jeep, Fiat Chrysler made recalls, Tesla Motors already issued patches related to cyber vulnerabilities and a lot of money is involved all around. Maintaining trust a big deal, and with every new “thing” that gets connected to the Internet, more holes exist that allow hackers to stir up trouble. It doesn’t stop with cars either, not by a longshot. Who would have thought just a few years ago that hackers accessing a sniper rifle would have to be a concern, or a washing machine, a refrigerator, a medicine cabinet or a medical implant. Fact is, they are all entry points that now have to be scrutinized, or a company striving to make things more convenient for customers may just find they shot themselves in the foot for all their efforts instead. From new digital gadgets to application security, it all has to be on the table and considered from a security perspective. It’s hard to keep up, but that’s what we help clients do. We look at their big picture, help figure out where they are vulnerable and what they are vulnerable to security holes can get plugged. And if litigation becomes a concern or a reality, the Internet of Things may introduce an entirely new playbook when it comes electronic discovery (eDiscovery) which we can help with too.”
Responding to the unthinkable
“The mantra in today’s cyber threat landscape has to be this,” says Caruso, “cyber threats are evolving every day. Threats no one ever saw coming will pop up, or someone will slip up and leave an opening an attacker is just waiting for. The difference between survival and total demise will all come down to how an organization responds. One of our biggest strengths in the security industry are our 24/7 emergency incident response teams, strategically positioned across the country and the globe to ensure we can have boots on the ground within hours, not days, to almost any metropolitan area. But most of the time we work even faster than that, with remote response options, in many cases, which allow us to be instantly on the job. Anyone can call us in an emergency, but clients that use us for our vulnerability assessments and pen-testing have some big advantages; we’ll already know the lay of the land relating to their requirements, regulatory compliance issues, data flow and digital architecture, and we will have already helped them devise and/or improve their emergency response policies and procedures so they have an easy-to-follow road map and escalation matrix ready to be executed at the first sniff of trouble. Our clients can also have us waiting in the wings with the “no-retainer” response services we offer our pen-testing clients. If something happens, we’re a phone call away and can jump right in knowing exactly what’s what so we can respond as efficiently and cost-effectively as possible, and if nothing happens, having us on call won’t cost them a thing. And that’s as close as you can get to a no-lose scenario in today’s digital world. Black Hat 2015 offered up a lot of FUD (Fear, Uncertainty and Doubt) again this year, but we’re here to get you through whatever you actually encounter in the real world.”
*Global Digital Forensics is a recognized industry leader in the fields of computer forensics, cyber security and emergency incident response, with years of experience assisting clients in the government, banking, healthcare, education and corporate arenas. For a free consultation with a Global Digital Forensics specialist, call 1-800-868-8189 about tailoring a cost-effective plan which will meet your unique needs, without wasting resources on solutions you simply don’t need. Emergency responders are also standing by 24/7 to handle intrusion and data breach emergencies whenever and wherever they arise. Time is critical if a cyber incident has occurred, so don’t hesitate to get help. For more information, visit our cyber security page.
On Tuesday, July 28th, Symantec released a security industry whitepaper on The Black Vine cyberespionage group, who are thought to have been behind the attack on Anthem Inc. which resulted in one of the largest data breaches in history. Among the topics covered were zero day exploits, watering hole attacks and spear phishing campaigns.
For Joe Caruso, founder and CEO/CTO of Global Digital Forensics (GDF), a premier national provider of cyber security solutions and digital forensics services headquartered in New York City, one big thing all these threat vectors have in common is that they leverage trust. “Trust has always been the go-to weapon of choice for cyber criminals. Many users will trust their antivirus scanners without question, but zero-day attacks exploit that trust. Spear phishing campaigns trick users into clicking on a link to a malicious site or opening an infected attachment by sending an email posing as someone they are not, again counting on trust to do the work. The same goes for watering hole attacks, trust is the weapon. In essence, the only thing security personnel can truly trust in is the fact that nothing should be blindly trusted, because doing so will almost always be a strategy that leads to disaster.”
The poisoned well
“Watering hole attacks are an old favorite on the cyber threat landscape. By doing some simple research and figuring out what sites are frequented by the players from the particular industry or organization they want to target, hackers can then focus on compromising less secure peripheral industry sites which will allow them to be used as an ambush spot to quietly deliver a malware payload like a RAT (Remote Access Trojan) to all the unsuspecting industry visitors that simply stopped by for a routine visit, effectively giving them a backdoor into a variety of other targets in the industry they are targeting. Once that’s accomplished, the hackers have their foot in the door to all of those respective networks as well, free to steal, modify and/or corrupt ESI (Electronically Stored Information) at will, or use them as a springboard to attack even more targets. Watering hole attacks are another example of how hackers leverage trust to find success,” says Caruso. “These visitors are not being compromised because they are visiting dubious sites, they are being victimized by visiting sites they should be able to trust, like industry forums, vendor sites and specialized news outlets.”
Zero Day Exploits
“Since stealth is a main ingredient of any successful large-scale cyber attack or espionage campaign, zero-day attacks are one of the most preferred malware delivery vectors due to their near invisibility - because they have not yet been reported, documented and patched. This is the inherent flaw with typical anti-malware solutions,” says Caruso, “they rely on matching a signature, or footprint, against a database of only known threats. Zero-day attacks allow hackers to use the time from when they identify an exploitable flaw in a program’s code to the time it is finally discovered and patched as their window of opportunity, and sometimes that window can cover weeks, months, or more. Some even employ fake security certificates, relying on that ingrained trust factor to have the victim proceed down the dark road they want them to travel.”
There are of course some basic steps everyone should follow to significantly reduce the chances of being the victimized by most forms of malware, and simple but crucial things like raising user awareness enterprise wide can be key to stopping many social engineering attacks like spear phishing, but APTs (Advanced Persistent Threats) and zero-day attacks are often in a different class. They are among the hardest to stop using yesterday’s reactionary approach to IT security. They are the threats that can prove devastatingly destructive and costly to even the most recognized and technologically savvy organizations on the planet. Because while traditional antivirus and anti-malware solutions may do a great job of handling the vast majority of cyber threats businesses face on a daily basis, their radar is simply not designed to handle sophisticated threats like today’s APTs and zero-day exploits. GDF employs both industry-recognized solutions as well as internally developed state-of-the-art proprietary tools and methods designed by veteran cyber security experts that live in the trenches of the cyber battlefield every day and know how hackers work in the real world.
*Global Digital Forensics is a recognized industry leader in the fields of computer forensics, cyber security and emergency incident response, with years of experience assisting clients in the government, banking, healthcare, education and corporate arenas. For a free consultation with a Global Digital Forensics specialist, call 1-800-868-8189 about tailoring a cost-effective plan which will meet your unique needs, without wasting resources on solutions you simply don’t need. Emergency responders are also standing by 24/7 to handle intrusion and data breach emergencies whenever and wherever they arise. Time is critical if a cyber incident has occurred, so don’t hesitate to get help. For more information, visit our cyber security page.
On June 20th, Forbes published an article which offers some good food for thought about what mobile applications in the workplace mean for information security today, with one big takeaway being that far too few mobile users are connecting the dots that their personal mobile habits could have dire consequences for the organizations they work for. It’s time mobile apps and mobile devices move way up the board on potential security threats to businesses, and Global Digital Forensics has solutions that can help.
The blurry line between personal and professional computing
“It’s only been a few years since IT security personnel didn’t have to give a second thought to personal mobile devices as a threat to an organization’s cyber security posture, but those days are a fading memory now,” says Joe Caruso, founder and CEO/CTO of Global Digital Forensics (GDF), a premier national provider of cyber security solutions and digital forensics services headquartered in New York City, “and with even more personal computing devices and apps breaking into the market, the problem of controlling and securing digital assets and sensitive data is not going to get any easier any time soon. And don’t be fooled, it’s not just millennials, users from every age group are hooked on mobile computing and the app craze these days. Further complicating matters is the increasing use of popular, free and easy-to-use cloud-based online data storage sites like Dropbox which are popular ways to keep data at hand across multiple platforms, and the potential security headaches associated with comingling personal and professional files and data outside of the organization’s control are also important factors that must be seriously considered and monitored.”
“It should be crystal clear that stomping out potential security holes related to mobile devices and associated apps is not a problem that will likely be solved by trying to simply remove them from the equation. With so many individuals now using mobile apps and more and more companies turning to apps to increase worker productivity and enhance their clients’ online accessibility and experience, the potential for bad things to happen on the data security front is certainly not only plausible, but probable,” warns Caruso. “Another big problem is that there are an awful lot of people who have experienced being hacked or infected with a virus on their smartphones through the countless insecure apps that are readily available, and that means there is also a very good chance they will be a great delivery method for hackers to infiltrate the company network as well.”
Assessing, Testing, Building Awareness and Emergency Incident Response
“The best way to deal with the threats posed by now prevalent BYOD practices, and the other peripheral issues like cloud-based data storage, is by reshaping the organization’s cyber security posture to keep up with the newest trends in technology and user behavior, because relying on yesterday’s assessments, methods, policies and procedures will leave you exposed and vulnerable today,” says Caruso. “At GDF, we’ve been helping clients protect their most valuable digital assets and data for many years by providing cutting-edge cyber security solutions. Our network vulnerability assessment protocols are constantly being updated to include the newest trends and threats. Our comprehensive penetration testing framework is always being refined to simulate what hackers are doing in the real-world, right now today, from the newest techniques and malware, to full simulations of sophisticated spear phishing campaigns, the number one delivery method for advanced attacks. We work hand in hand with our clients through every step of the process, from identification all the way through remediation, including helping them significantly improve user awareness on today’s cyber threats on an organizational level, because without addressing the human element, everything else is just an exercise, not a solution. And if the unthinkable has already happened, like a data breach or cyber intrusion, we have emergency incident response teams strategically positioned across the country and worldwide who are on call 24/7 to respond to any cyber emergency. In most cases, we can even start the remediation process remotely, which means immediately.”
*Global Digital Forensics is a recognized industry leader in the fields of computer forensics, cyber security and emergency incident response, with years of experience assisting clients in the government, banking, healthcare, education and corporate arenas. For a free consultation with a Global Digital Forensics specialist, call 1-800-868-8189 about tailoring a cost-effective plan which will meet your unique needs, without wasting resources on solutions you simply don’t need. Emergency responders are also standing by 24/7 to handle intrusion and data breach emergencies whenever and wherever they arise. Time is critical if a cyber incident has occurred, so don’t hesitate to get help. For more information, visit our cyber security page.
An article published in BankInfoSecurity on Thursday, July 16, highlighted the headache the Office of Personnel Management (OPM) is now going through in their efforts to notify the over 20 million people who were affected by two massive data breaches. While numbers that size are not typical, any business plugged into the digital world is susceptible to a data breach and needs to have an effective emergency response plan in place should the unthinkable happen.
Joe Caruso, founder and CEO/CTO of Global Digital Forensics (GDF), a premier national provider of cyber security solutions and digital forensics services headquartered in New York City, has been on the responding end of these types of emergencies many times, and has seen repeatedly just how costly and destructive a successful breach can be to all kinds of organizations. “Without a well thought out plan in place before an attack occurs, the chances of coming though it in one piece are not favorable at all, especially for small to medium sized businesses that don’t have the deep pockets and resources which are available to the larger type corporations or government agencies. But things are far from hopeless, there are things that can be done to significantly increase an organization’s chances of being able to weather the storm, but waiting to implement them will often prove too much to overcome.”
Before a breach
“We start with a thorough cyber threat assessment which takes into account a client’s unique needs, digital architecture and data work flow, reviewing policies and procedures, and helping them strengthen them, or create them from scratch if none are present,” says Caruso. “The threat vectors that are problematic for one industry or organization may not be a high priority for another. Our broad expertise lets us tailor the assessment to illuminate the right problem areas for any client.”
“Next is our comprehensive penetration testing,” continues Caruso, “which is basically us taking the role of real-world hackers and trying to infiltrate the network using a wide variety of tools and techniques, from social engineering strategies, to sophisticated phishing and spear phishing campaigns. We have many tradecraft tricks up our sleeves, just like real hackers do, and so far we have never failed to compromise our target. Our successes will only help to spotlight weakness in the client’s cyber security posture so they can be significantly improved, but a real hacker’s success could cost the client everything.”
After a breach
“Emergency incident response is next on tap, and is probably the most vital piece of the data breach puzzle,” says Caruso. “Our extensive experience in network forensics and security, as well as our ‘No Retainer Policy’, make it both cost-effective and simple to ensure your organization has a response team standing by to handle the problem, mitigate the damage and ensure regulatory compliance, all with absolutely no downside or unnecessary expenses. It just doesn’t get any easier than that to have professional, experienced assistance you can rely on in the event the unthinkable happens. Experienced emergency responders can also help businesses avoid the extremely costly pitfalls of "over-notification" by helping to quickly determine exactly which records were compromised and exactly who should be notified about the event, because as with most things in life, unnecessary excess typically doesn't lead to a happy ending.”
“We will also work with the client, if necessary, to help them identify an internal CISO (Chief Information Security Officer). In today’s digital age, it is imperative to fill this role,” warns Caruso, “either internally, or with a competent and knowledgeable outside vendor. We will also help create an escalation matrix of responsibilities, procedures and emergency guidelines to ensure the right steps to be followed and maintained going forward are clearly spelled out.”
To survive and thrive in the digital arena and reduce the potentially debilitating impact of successful cyber intrusions and data breaches, the decision to take control of cyber security responsibilities and emergency incident response is both crucial and necessary. So don’t wait until it’s too late to get started, call Global Digital Forensics today.
The right solutions at the right price
*Global Digital Forensics is a recognized industry leader in the fields of computer forensics, electronic discovery (eDiscovery), cyber security and emergency incident response, with years of experience assisting clients in the government, banking, healthcare, education and corporate arenas. For a free consultation with a Global Digital Forensics specialist, call 1-800-868-8189 about tailoring a plan which will meet your unique needs. Emergency responders are also standing by 24/7 to handle intrusion and data breach emergencies whenever and wherever they arise. Time is critical if a cyber incident has occurred, so don’t hesitate to get help. For more information, visit our data breach response page.
ABC News reported on Thursday, July 9th, that the four month investigation into two hacks on the Office of Personnel Management (OPM) revealed, “more than 22 million people inside and outside government likely had their personal information stolen,” and that, “hackers allegedly rummaged through various OPM databases for more than a year.”
In the digital world, what you don’t know can hurt you
Joe Caruso, founder and CEO/CTO of Global Digital Forensics (GDF), a premier national provider of cyber security solutions and digital forensics services headquartered in New York City, has led emergency response teams for clients for many real-world data breach emergencies, and has no doubt it was not any kind of quick in and out attack. “Mega-breaches like this don’t happen quickly, and they aren’t easily discovered. Advanced malware threats hide on infected systems for a long time, and if you couple that with the fact that numerous cyber attacks like these are going unreported because many victims still have no idea that attackers already have, and may have had for a long time, a presence on their network, and the scope of the problem can be mind-boggling. These OPM breaches alone have affected roughly 15% of the US population, just let that sink in.”
Fully protected? Not a chance
“You would be hard pressed to find any company today without firewalls, virus scanners and a host of security measures implemented,” says Caruso. “Still malware gets through. First because these types of solutions can’t account for the biggest weakness in any organization, the human element, and their susceptibility to social engineering ploys like phishing and spear phishing attacks, or compromised vendors being used as a springboard for attacks by using their valid credentials against another target. And secondly, because typical antivirus and anti-malware solutions rely on signatures of known threats in order to detect, identify and remove them. But if a threat is unknown. Like a Zero Day exploit, or advanced enough to hide from security programs by disabling or fooling them by changing its “signature,” it simply isn’t detected, allowing it to remain hidden and function destructively for years at a time in many cases. Spyware, RATs (Remote Access Trojans), rootkits, polymorphic viruses, they can all be sitting right there on the system waiting for the attackers to use them to do what they do, out of sight, and out of mind.”
Regularity is key
“The main ingredients for success when it comes to enhancing an organization’s cyber security posture are commitment and regularity,” says Caruso. “Every company relying on the digital world in any form or fashion has to understand it’s not a choice today, it’s a necessity, and they have to be committed to making a stand and following through with it. They have to understand what they are vulnerable to, which can be very unique company to company, and they have to know what their weaknesses are. And it’s not a one shot deal, the process has to be repeated regularly to make sure the organization’s cyber security posture evolves with the cyber threat landscape. That’s why we always recommend combining our professional vulnerability assessments with our comprehensive penetration testing services, and since the human element in any security chain is typically the weakest link, that’s why we also put such strong focus on social engineering throughout. And since we have the real-world experience and an extensive, proven background covering a wide array of clients, we can typically flat-rate proposals to take the guess work out of the process. We also try our best to promote regularity by offering even further discounts when organizations sign up with us for bi-annual, or quarterly assessments and testing. The added advantage to that is we will find and eradicate any malware or intrusion that may have come into existence between cycles, and with many intrusions today often lasting months or even years, it’s much better to spot it and fix it sooner rather than later, not to mention far and away less costly to the organization in the end.”
*Global Digital Forensics is a recognized industry leader in the fields of computer forensics, electronic discovery (eDiscovery), cyber security and emergency incident response, with years of experience assisting clients in the government, banking, healthcare, education and corporate arenas. For a free consultation with a Global Digital Forensics specialist, call 1-800-868-8189 about tailoring a plan which will meet your unique needs. Emergency responders are also standing by 24/7 to handle intrusion and data breach emergencies whenever and wherever they arise. Time is critical if a cyber incident has occurred, so don’t hesitate to get help. For more information, visit our cyber security page.
When a hacker gains access to someone’s email account, it can lead to all sorts of trouble, both on the home front and at the office. On Wednesday, July 1st, the FTC issued a scam alert about a social engineering scam which cons a target into divulging their credentials as part of a verification process for a password reset instigated by the hacker. All they have to do is click for a password reset and then follow it up with a text to the target’s phone pretending to be the email provider asking them to verify it to complete the process. If the target is set up to receive those kinds of text notifications, which many people are these days, it will all seem normal. With access now, a hacker can peruse the victim’s email account for more personal information, see information on other accounts that may have been set up, use it as a launching pad to send phishing emails to friends, family or work colleagues, and even have future emails copied to them as well before the victim ever even notices the problem.
This kind of social engineering attack not only shows how hacker techniques continuously evolve, but it also shows what can happen in the aftermath of all those data breaches that have been making headlines this year that saw the personally identifiable information (PII) of millions put out “in the wild.” For this scam to work, all a hacker needs is someone’s email address and mobile phone number, making it obvious that stolen information doesn’t need to include social security numbers, passwords, or account numbers to cause all kinds of problems.
Joe Caruso, founder and CEO/CTO of Global Digital Forensics (GDF), a premier national provider of cyber security solutions and digital forensics services headquartered in New York City, has been beating the drums about social engineering dangers for years. “It’s the biggest cyber security weakness most organizations have,” he says, “someone from inside the castle falling for a social engineering ploy, whether it’s something like this, or just a simple phishing email. From there creativity is the only limitation for how attackers will leverage that access to steal from, destroy, take hostage, or control a corporate network.”
Regular testing and awareness training are crucial
GDF puts a strong focus on social engineering during their professional penetration testing, going through the same efforts real-world hackers do to craft these kinds of convincing campaigns, and then helps an organization raise awareness enterprise wide according to the results. To date, GDF has never failed to penetrate a client’s network, and the eye-opening results go a long way in making the lessons learned stick for everyone. GDF can also provide tailored social engineering awareness training for clients to help their employees better understand the threats that are out there, what to be on the lookout for, and what they should do if they suspect they may have been compromised.
Cyber survival today is also about how you respond when you get knocked down
It’s an undeniable fact; eventually, every organization gets hacked in some form or fashion, whether it comes from the outside, from within, or both, like a social engineering attack. But the organizations that will weather the storm will be the ones with predetermined emergency response policies and procedures ready to go. Global Digital Forensics has experienced emergency response teams on call and strategically positioned across the country and the globe to be able to respond quickly and effectively whenever an emergency strikes, day or night. And for organizations that use GDF to perform professional vulnerability assessments and penetration testing, no-retainer Service Level Agreements (SLAs) are available so you can always have expert responders waiting in the wings should an emergency event materialize, without having to spend anything if nothing happens. GDF can also help clients craft emergency response policies and procedures from scratch, if none exist, or help bring existing plans up-to-date to meet today’s threats, as well as design an effective escalation matrix which can be easily followed to make sure your initial response efforts move like clockwork. It’s as close to a no-lose-scenario as it gets to deal with cyber emergencies, from identifying and stopping the attack, to reporting procedures and other regulatory compliance issues that may be involved for specific industries.
The right help against today’s cyber threat landscape
*Global Digital Forensics is a recognized industry leader in the fields of computer forensics, electronic discovery (eDiscovery), cyber security and emergency incident response, with years of experience assisting clients in the government, banking, healthcare, education and corporate arenas. For a free consultation with a Global Digital Forensics specialist, call 1-800-868-8189 about tailoring a plan which will meet your unique needs. Emergency responders are also standing by 24/7 to handle intrusion and data breach emergencies whenever and wherever they arise. Time is critical if a cyber incident has occurred, so don’t hesitate to get help. For more information, visit evestigate.com.
According to a new study released by Raytheon/Websense, summarized here in this article published in Information Week’s Dark Reading on Tuesday, June 23rd, banks still garner the most attention when it comes to cyber attacks; three times more than any other industry. The attention, however, isn’t new, and banks and other financial institutions are usually on the cutting edge when it comes to technology solutions geared to keep their networks safe. “But there is still a soft spot that technology alone still can’t quite solve,” says Joe Caruso, founder and CEO/CTO of Global Digital Forensics (GDF), a premier national provider of cyber security solutions and digital forensics services headquartered in New York City, “and that soft spot comes in the form of personnel already inside the castle.”
Social engineering is still king when it comes to infiltrating a financial or corporate network
“Social engineering comes in many forms, but spear phishing is still public enemy number one for IT security personnel, for banks and corporations alike. Spear phishing emails can be extremely personalized, and depending on the skill level, resources and diligence employed by the attacker, they can be both very convincing and quite difficult to identify as a malicious threat. Spear phishers used to rely heavily on social media bait, like faked LinkedIn or Facebook invitations and other personal notifications, but now they are evolving into other types of notifications, like that a voicemail or fax from a known vendor came in, or package delivery notifications which make complete sense by referencing individuals, projects or departments employees are familiar with. Many times the information attackers use comes from an organization’s own website, press releases and/or other announcements. They will also apply advanced tactics like spoofed headers, basically changing the From: address to match up to the identity of the person or organization they are pretending to be. The worst part is if just one individual gets “conned,” any and all organizational digital assets could quite possibly be compromised as a result,” warns Caruso.
“From the CEO to the fresh new intern, everyone is vulnerable and could be all the foothold attackers need to see whatever agenda they have through to fruition, so don’t be afraid to pick up an actual telephone and confirm an unexpected email, and if it turns out to be a hoax, report it immediately to whoever is tasked with the organization’s cyber security.”
Combating the threat revolves around testing, awareness and response
“The social engineering aspect of cyber intrusions, which is where spear phishing would fall, is something we focus on heavily when we are called in to do cyber threat assessments and comprehensive penetration testing for clients, which range from very small businesses to well-known financial institutions. The scale and scope of the tradecraft we will employ is discussed and agreed upon in advance and then we go to work,” says Caruso. “Nothing we do will be destructive, but it will definitely be enlightening. We’ll do the same things real-world attackers would do. We’ll use publicly available information and anything else we can get our hands on, online, by telephone, or even in person, and craft a spear phishing campaign. We’ll do everything from creating full blown dummy websites, to spoofing an individual or department within the organization itself. And so far, we’ve never failed to get a foot in the door. When we divulge our findings in our detailed report, it’s got a shock and awe factor that really sinks in deep. It has the powerful, double-barrel effect of exposing weak links in the organization’s cyber security posture, as well as serving as an excellent springboard to raise internal cyber-threat awareness significantly. From there we’ll tailor a remediation plan with the client. If the client chooses, we can even hold awareness seminars to get the entire organization on the same page, from what to look for and how to spot these types of threats, to what to do if a malicious threat is found. And of course we can also satisfy any cyber emergency incident response needs a client may have with our team of experienced cyber responders, strategically positioned across the country and the worldwide and available any time of the day or night, just in case.”
Don’t wait
Every organization’s needs, desires and digital infrastructure are unique. But having veteran cyber security experts like the experienced team at Global Digital Forensics come in to professionally tailor a testing and response plan specifically geared to the individual client, can go a long way to not only preventing the initial gateway intruders can use to wreak havoc, but also substantially lessen the destructive aftermath should an attack or intrusion still manage to occur. There is no such thing as absolutely perfect protection, but the odds of being attacked and/or the consequences can be greatly affected with the right plan in place.
*Global Digital Forensics is a recognized industry leader in the fields of computer forensics, electronic discovery (eDiscovery), cyber security and emergency incident response, with years of experience assisting clients in the government, banking, healthcare, education and corporate arenas. For a free consultation with a Global Digital Forensics specialist, call 1-800-868-8189 about tailoring a plan which will meet your unique needs. Emergency responders are also standing by 24/7 to handle intrusion and data breach emergencies whenever and wherever they arise. Time is critical if a cyber incident has occurred, so don’t hesitate to get help. For more information, visit our cyber security page.
Ever since The New York Times, on Tuesday, June 16th, reported that the St. Louis Cardinals were being investigated by the FBI and Justice Department for allegedly hacking into a database owned by the Houston Astros, speculation about what actually happened and how it happened has run rampant. But at the very least, all the possibilities being floated should perk up the ears of anyone responsible for the protection of corporate digital assets, no matter what industry they’re in.
Joe Caruso, founder and CEO/CTO of Global Digital Forensics (GDF), a premier national provider of cyber security solutions and digital forensics services headquartered in New York City, has been involved in many cases dealing with stolen intellectual property (IP), from both the perspective of a cyber security expert and a digital forensics expert, and has seen firsthand what kind of devastation a business can suffer when IP is stolen through a hacking event.
“We’ve been on both sides of the fence for over two decades,” says Caruso, “from cyber emergency incident response and everything else cyber security related, to assisting attorneys with all their eDiscovery needs for litigation. IP cases have always been near the top of the list on both fronts. What actually happened between the Cardinals and the Astros in this case is simply a big unknown at this point from an outsider’s perspective and it’s going to take a while to unravel the truth, but with every new news article and new allegation, it’s like shining a spotlight on all the possibilities corporate IT security personnel have to be aware of and be prepared for. Initial reports suggested that reused passwords may have been the culprit which allowed Cardinals personnel to access the Astros’ proprietary database. But just as quickly, follow up reporting by Sports illustrated (like this exclusive on June 18th) has Astros GM Jeff Luhnow, who is at the center of the storm, vehemently denying that was the case. What actually happened and who is responsible is going to take a lot of digital forensics work, but from a security view, password policy and enforcement shortcomings really can cause major issues for businesses. That’s why we include it as one small but vital component in our professional vulnerability assessments, to help businesses identify any deficiency in policy and/or enforcement so the right changes can be made for added protection going forward.”
Insider threats are very real
The specter of an insider taking proprietary information was also raised in the Sports Illustrated exclusive, saying “that Cardinals officials were concerned that Mr. Luhnow had taken their idea and proprietary baseball information to the Astros.”
“Again, not making any kind of claim whatsoever that it happened in this case, it is a fact that insiders taking proprietary information with them when they leave for a competing organization is actually quite prominent and problematic in many cases,” says Caruso, “and to that end we developed an electronic exit interview process businesses can use to find out what an employee on the way out may be trying to take with them, as well as having a great deterrence effect.”
What Does an Electronic Exit Interview Entail?
“The first thing we do is make a forensic image of the employee’s hard drive, and if necessary, we can also do the same thing with mobile devices,” says Caruso. “Then one of our certified forensic technicians will extract all the electronic correspondence, like email, online chats and social networking etc., as well as documents and other information deemed pertinent according to the concerns of the client. Then we will generate a full forensics report detailing the drive contents, the results of our searches, and a full description of our forensically sound process with all the relevant technical data. And since we are intimately familiar with the world of electronic discovery and the nuances of digital evidence and computer forensics, our clients can rest easy knowing that our findings will stand up to even the highest levels of scrutiny from the opposition or the court if litigation becomes a reality.”
“Once we have a better understanding of the client’s unique situation, we can also set up package deals for multiple exit interviews, so that whenever an employee departs, for whatever reason, we’ll have the process in place to repeat it as often as necessary. It’s definitely a low risk and high reward situation if you consider what can happen when internal cyber assets are misused. And it should come as no surprise to anyone that when an employee is terminated, desperation and revenge can easily become driving forces which lead people to do unthinkable things. The key is protecting the business right out of the gate. Even on just a psychological level, if an employee is made aware of the electronic exit interview process, chances are they will think long and hard before trying any funny business with corporate cyber assets, but if they don’t, our electronic exit interviews will stack the deck for our client with the cards they’ll need should any future actions become necessary. Timing is everything when it comes to performing an electronic exit interview for a departing employee, so don’t wait until your sensitive company data is already out the door,” says Caruso, ”because by then, it may already be too late.”
*Global Digital Forensics is a recognized industry leader in the fields of computer forensics, cyber security and emergency incident response, with years of experience assisting clients in the government, banking, healthcare, education and corporate arenas. For a free consultation with a Global Digital Forensics specialist, call 1-800-868-8189 about tailoring a cost-effective plan which will meet your unique needs, without wasting resources on solutions you simply don’t need. Emergency responders are also standing by 24/7 to handle intrusion and data breach emergencies whenever and wherever they arise. Time is critical if a cyber incident has occurred, so don’t hesitate to get help. For more information, visit www.evestigate.com.
On May 12, 2015, tragedy struck. An Amtrak train on route from Washington to New York tried to take a turn rated for 50 mph while travelling in excess of 100 mph. When the smoke cleared, 8 were left dead and more than 200 injured. Among the injured was Brandon Bostian, the engineer, who seems to have no recollection of the events leading up to the disaster due to the trauma he suffered. So now, as reported by NBC News on Wednesday, June 10th, investigators are trying to fill in some of the gaps with mobile forensics on Bostian’s phone.
The quest for answers in a mobile digital world
“Mobile devices today can tell a lot of tales,” says Joe Caruso, founder and head of Global Digital Forensics (GDF), a recognized national leader in computer forensics and electronic discovery (eDiscovery) services. “The burning question for accident investigators, obviously, is what happened? And of course, the logical place to start is with the engineer at the controls, who unfortunately in this case though, can’t seem to remember anything. So without means to question the most important witness, investigators have to start flying theories using the information available to them. But in this case, a mobile phone is in the equation, which can make a big difference."
"Mobile devices can often reveal plenty of relevant information to investigators about an individual involved in an incident," says Caruso, "like their habits, interests and sometimes even their state of mind by analyzing texts, phone call records, pictures taken, Internet activity, emails and often geolocation data as well, which can be used to build a timeline of when and where things happened. But sometimes, they can also help investigators cross off things that didn’t happen, like whether or not an engineer at the controls during a tragic train accident was talking, texting, or being otherwise distracted by his smartphone. Because at the core of the investigative process, eliminating possibilities helps focus efforts and resources on other plausible scenarios.”
“Of the utmost importance though,” Caruso says, “is to make sure to collect that data as quickly as possible from as many devices as are available before any valuable data is overwritten or otherwise lost. Because in the end, it’s far better to have the data and not need it, than to need it and not have it. That’s why we started offering a Mobile Forensics Quick Analysis to make the process easy and affordable for investigators and attorneys that deal with accident investigations and/or litigation. For a flat rate of $1595, which is very low as far as comparable pricing across the industry, our Quick Analysis is designed to correctly collect all the data from mobile devices and help clients determine if a more thorough analysis is justified.”
THE GDF QUICK ANALYSIS PROCESS:
- 1. The suspect device is received, and logged.
- 2. A proper chain-of-custody log is created.
- 3. The suspect device is forensically duplicated (imaged) using court accepted procedures.
- 4. The original evidence is properly stored in compliance with court approved procedures.
- 5. GDF’s certified analysts search the entire mobile device for all recoverable data.
- 6. All recoverable data is extracted and provided to the client in easy to understand format.
- 7. GDF’s assigned lead analyst forwards the results to the client.
- 8. The results will help identify the presence of any evidence or indicators to help client determine evidentiary value and decide if a more thorough analysis is warranted.
No excuses
“Once we’ve done the Quick Analysis, all of the data will be preserved in the exact same state it was on the day we received it,” says Caruso, “and can then be used in multiple ways at any time afterwards. If the investigators or attorneys need to build a timeline, they’ll have the collected data available to do it. If they need to broaden their search scope after learning more about the case, we’ll be able to help with that too, using the data from the original collection. And if things get more complex, our vast experience and expertise in all things relating to digital evidence will let our specialists seamlessly transition to a more thorough analysis of any and all data if necessary, and assist with any further eDiscovery needs the client may have, all the way through production and expert witness testimony. It doesn’t get any easier or cost effective, so there should be no excuses when it comes to leveraging every benefit mobile forensics can offer, because when tragedy strikes, anything that can shed light on the who, what, when, where, why and how of a case can prove invaluable.”
The right choice when evidence goes digital
*Global Digital Forensics is a recognized leader in the fields of computer forensics, eDiscovery, cyber security and emergency incident response. To speak with a digital evidence specialist about your unique situation, or any other computer forensics, eDiscovery or cyber security needs involving Electronically Stored Information (ESI), call 1-800-868-8189, or visit GDF’s computer forensics page.
The IRS released an official statement on Wednesday, May 26th 2015, announcing that, “criminals used taxpayer-specific data acquired from non-IRS sources to gain unauthorized access to information on approximately 100,000 tax accounts through IRS’ “Get Transcript” application. This data included Social Security information, date of birth and street address.”
“You don’t even have to be in the cyber security industry to have to think it was only a matter of time, especially after all the headline stories this year of mega-breaches which have exposed PII (Personally Identifiable Information) on an unprecedented scale,” says Joe Caruso, founder and CEO/CTO of Global Digital Forensics (GDF), a premier national provider of cyber security solutions headquartered in New York City, “just look at the Anthem breach earlier this year; that one alone affected 80 million people, putting huge amounts of personal data out there to be used, sold or traded by cyber criminals all over the globe. And Anthem was far from alone. That’s why absolutely every business plugged into the digital world has to do their part. An intrusion or breach may not only affect them, but customers, employees, vendors, investors, they can all be affected. And by extension, a security problem stemming from their customers, employees, vendors and/or investors can quickly become their problem too. Either way, it can prove devastating to any business of any size.”
Business reputation is always on the line
“When a customer gets notification that their personal information has been compromised, the first thing they tend to do is mumble some not very nice things about the organization that exposed them and then check their accounts to see if any real cash is gone, and there is an instant dose of relief if they find everything is thankfully still in order. As has become routine, the company then gives them credit and fraud protection for a year and everyone is supposed to go on their merry way. But sophisticated cybercrime rings know the routine too. They also have a lot of patience. Take the IRS hack. No one knows yet where the attackers got the personal information they used to walk right through the front door with a key in hand, but chances are good they didn’t even steal it themselves. There is an entire underground 'dark web' that deals in stolen credentials, like email accounts, passwords, Social Security numbers, credit card numbers and whatever else you can think of. And with things like Social Security numbers, those don’t get changed often. So in reality, cyber criminals can “bank” that kind of information and pull it out in two or three years, long after the free credit protection is gone, and unleash all kinds of trouble. So for hits on an organization’s reputation, it can be the gift that just keeps on giving. Social media is also a haven for cyber criminals, so those adorable pictures of your favorite pet Spike, that comment on your mother’s strange maiden name, or reminiscing about your favorite elementary school teacher can all give an acute criminal eye another piece of the puzzle to pretend to be you when security questions stand between them and the access they are after,” warns Caruso.
“The really sad thing is that more than nine out of ten times it’s something simple and basic that gets the snowball rolling downhill, like a simple phishing attack or outdated software security patches,” says Caruso. “We offer services like professional cyber threat vulnerability assessments and expert penetration testing to help businesses uncover weaknesses and substantially strengthen their cyber security posture. We know every client is unique and has different needs, but having been in the business of helping a wide variety of clients protect their most sensitive digital assets for over two decades, we also know how to help all kinds of organizations get the most bang out of their cyber security buck by not loading them up with services or solutions they simply don’t need. Overpricing and flat out gouging are unfortunately going to be prevalent in any industry that deals in emergencies, and new cyber security companies are popping up every day trying to get in on an exploding market. But we’ve seen our fair share of horror stories of organizations getting fleeced then abandoned by some of these self-proclaimed 'security hotshots' that promise the world and fail to deliver. We want to help clients work best within their available resources, because we want to be their partner for a long time to come. In the real world, cyber security is not something you do once, assessments and testing need to be performed regularly to have any hope of surviving and thriving in today’s cyber threat landscape, so doing the job right, with integrity, and at a fair price, is how we build relationships for the long haul.”
From professional vulnerability assessments and expert penetration testing, to deep scanning, emergency incident response and helping organization raise social engineering awareness enterprise-wide, Global Digital Forensics offers services and solutions that will fit the bill.
*Global Digital Forensics is a recognized industry leader in the fields of computer forensics, cyber security and emergency incident response, with years of experience assisting clients in the government, banking, healthcare, education and corporate arenas. For a free consultation with a Global Digital Forensics specialist, call 1-800-868-8189 about tailoring a cost-effective plan which will meet your unique needs, without wasting resources on solutions you simply don’t need. Emergency responders are also standing by 24/7 to handle intrusion and data breach emergencies whenever and wherever they arise. Time is critical if a cyber incident has occurred, so don’t hesitate to get help. For more information, visit our cyber security page.
On Wednesday, May 20, 2015, CareFirst BlueCross BlueShield (CareFirst) announced that, “the company has been the target of a sophisticated cyberattack,” and that it, ”was discovered as a part of the company’s ongoing Information Technology (IT) security efforts in the wake of recent cyberattacks on health insurers.”
The most notable attack on health insurers was reported in February of this year when Anthem Inc., the nation’s second largest health insurer, revealed that they had suffered a data breach of historic proportions, having data on almost 80 million customers and employees exposed.
Joe Caruso, founder and CEO/CTO of Global Digital Forensics (GDF), a premier national provider of cyber security solutions headquartered in New York City, sees stories like this unfold in the real world every day, and hopes more businesses take CareFirst’s example to heart. “The Anthem hack was a huge story in the healthcare and health insurance industries, and if there is one good thing that can come from that kind of headline making cyber attack, it’s that sometimes it can spark the right action by the right people, in this case CareFirst, who decided to beef up their cyber security posture as a result,” he says. “That led to professional testing, and lo and behold, it led to uncovering an attack that occurred as early as June of last year and flew under the radar ever since. It also shows there is absolutely no substitute for having professional vulnerability assessments, deep scanning and penetration testing done regularly, even if there wasn’t an “event” detected. In today’s digital world, every business has to understand this, because we all know it’s not just the healthcare industry that is being targeted by hackers, everyone is at risk, and we also know that failure on the cyber front can lead to disastrous consequences, no matter how large or small or tech savvy an organization may be.”
But there are steps cyber security professionals like Global Digital Forensics can help businesses take to fortify their delicate cyber-ecosystems, without crushing budgets. Some of these include:
1) Identifying threat vectors and cyber policy shortcomings - Because every organization is unique, a one size fits all approach is very rarely successful. In one situation laptops and insiders may be the highest threat vector, in another it may be outsiders or removable media. GDF will use a proven variety of methods to expose the most likely threat vectors and weaknesses in internal cyber policies. With this valuable information, detailed reports with remediation recommendations will be generated.
2) Data Flow Mapping – Many organizations have certain system areas containing confidential ESI locked down like Ft. Knox, but there are many paths and forms data can take in its lifespan. Cyber security can inherently not exist if an organization doesn’t know where every bit of data has traveled and who has accessed it, from conception to disposal. GDF’s detailed Data Flow Mapping will uncover the vulnerable points and offer recommendations to fortify those vulnerabilities.
3) Penetration Testing – Compared to IT security personnel, hackers have it easy. While those tasked with protecting data have to plug a million holes, a hacker only needs to find one. A penetration test conducted by GDF serves to expose the weaknesses a real-world hacker may find by attempting to hack through an organization’s security using the same exploits, techniques and strategies an outside hacker would use to gain unauthorized access to data. Detailed reports and remediation recommendations will then be generated so the vulnerabilities can be corrected.
4) Emergency Intrusion Incident Response Teams - In the ever evolving cyber landscape, there is unfortunately no such thing as perfect security, so even the most advanced cyber security measures may eventually be compromised. GDF has a network of emergency responders strategically located, both nationally and globally, to respond to an intrusion in a matter of hours. By setting up a Service Level Agreement (SLA) with GDF in advance, the response procedures and policy will already be laid out, and the time-critical task of mitigating damage and loss due to a data breach will be substantially improved. Having GDF signed on as emergency incident responders also helps satisfy certain regulatory compliance issues.
It is proven time again that how an organization responds to a data breach will greatly affect client trust and the public perception of an organization’s integrity, so don’t wait until it’s too late; the right time to take control of data security is right now.
*Global Digital Forensics is a recognized industry leader in the fields of computer forensics, cyber security and emergency incident response, with years of experience assisting clients in the government, banking, healthcare, education and corporate arenas. For a free consultation with a Global Digital Forensics specialist, call 1-800-868-8189 about tailoring a cost-effective plan which will meet your unique needs, without wasting resources on solutions you simply don’t need. Emergency responders are also standing by 24/7 to handle intrusion and data breach emergencies whenever and wherever they arise. Time is critical if a cyber incident has occurred, so don’t hesitate to get help. For more information, visit our cyber security page.
Earlier this week, on May 13, 2015, the InfoSec Institute published an article titled Anatomy of an APT Attack: Step by Step Approach, explaining what is involved in creating and executing APTs (Advanced, Persistent Threats), the type of sophisticated cyber attack that can keep security professionals of even the largest and tech savvy organizations and agencies awake at night. These types of attacks can not only be highly effective and hard to detect, but they typically allow attackers to maintain a long term presence on a network to exponentially magnify the effects of their successful intrusion, both internally and beyond.
Joe Caruso, founder and CEO/CTO of Global Digital Forensics (GDF), a premier national provider of cyber security solutions headquartered in New York City, has lived on the cutting edge of the cyber security industry since the infancy of the Internet, and has seen firsthand just how far the ripples of a successful APT attack can reach. “APTs are certainly not the most prevalent type of cyber attack, but they can unquestionably be the most devastating. The sophistication of evasion techniques ATPs are designed to use tend to allow for unfettered access to the targeted networks for amazingly long stretches of time, sometimes years, putting not only an organization’s ESI (Electronically Stored Information) and digital assets at risk, but also providing a pipeline to expand their attack to vendors, clients, investors or anyone else “connected” to the compromised victim’s network. And for the whole circus to unfold, all it takes is something as simple as a single individual within an organization to take the bait of a phishing or spear phishing email and open an attachment or follow a malicious link. From there a backdoor gets installed and it’s off to the races.”
“APTs are not typically of the smash-and-grab attack variety; they are built for longevity. Although, if the attackers sense they have been or will be detected, they may accelerate the attack to do or get what they can while they’re in. That’s what makes testing regularity so important from a defensive front. The faster the attack can be detected, identified and eradicated, obviously the less severe the aftermath will be. Because the reality that must be faced is that there are always ways in and weaknesses must continuously be assessed, identified and remediated,” says Caruso. “Fortunately, strengthening cyber security doesn’t necessarily have to be expensive hardware or software based solutions, it can often come in the form of creating or updating security policy to keep everyone informed, trained and alert. No matter how you slice it, APT attackers have to first get their foot in the door, a vast majority of the time relying on social engineering against the human element to achieve that goal, so if you can stop that first event before it happens, you are way more than half way home.”
“For years we’ve been assisting hospitals, universities, financial institutions, businesses and corporations of all sizes to deal with the constantly evolving threats on the digital frontier,” says Caruso, “and so far we have never done a cyber threat vulnerability assessment, or a penetration test without finding numerous ways to help improve the client’s cyber security posture. Our background in dealing with such a diverse range of customers and such a wide array of threat verticals gives us great insight not only into the threats they face, but also how industry specific technologies are used and how they must conform from a regulatory compliance standpoint. And that means eliminating a lot of the guesswork and mistakes new players in our field often have to go through, while providing streamlined and effective solutions that don’t wreak havoc on the all-important bottom line.”
“The truth is, everyone is at risk," warns Caruso, "and until every organization with a presence online routinely addresses the reality of cyber security threats, proactively - not only after an incident has been identified, the consequences can not only devastate their own organization, but the ripples and subsequent aftermath can have a reach that’s mind boggling, not to mention the hits to business integrity, client trust and potential liability issues that can be crippling.”
Global Digital Forensics understands that cookie-cutter approaches to cyber security are simply not adequate when applied to the myriad of unique needs different clients in different industries have. So GDF tailors solutions according to each client’s needs and constantly strives to update offerings and solutions to make them as effective and current as possible, including professional cyber threat vulnerability assessments, advanced penetration testing, social engineering testing, deep scan detection and analysis, policy and procedure review, regulatory compliance assistance and 24/7 emergency incident response.
*Global Digital Forensics is a recognized industry leader in the fields of computer forensics, cyber security and emergency incident response, with years of experience assisting clients in the government, banking, healthcare, education and corporate arenas. For a free consultation with a Global Digital Forensics specialist, call 1-800-868-8189 about tailoring a cost-effective plan which will meet your unique needs, without wasting resources on solutions you simply don’t need. Emergency responders are also standing by 24/7 to handle intrusion and data breach emergencies whenever and wherever they arise. Time is critical if a cyber incident has occurred, so don’t hesitate to get help. For more information, visit our cyber security page.
Spear Phishing
Just as the name suggest, spear phishing is a more targeted form of phishing, where hackers leverage a more personal touch for highly increased effectiveness. On May 5, 2015, the InfoSec Institute published an article titled, Spearphishing: A New Weapon in Cyber Terrorism, in which they breakdown the perils of spear phishing and how terrorist groups can use this threat vector for everything from access and espionage, to cyber scams which can see real money funneled directly to financing terrorist activities.
For Joe Caruso, founder and CEO/CTO of Global Digital Forensics (GDF), a premier national provider of cyber security solutions headquartered in New York City, spear phishing has always been at the top of the charts when it comes to the myriad of dangerous threat vectors business are confronted with every day. But he hopes, “stories like this that put the word “terrorist” into the same sentence as spear phishing will help bring some much needed focus to the serious threat targeted social engineering campaigns like spear phishing can pose to any business, because next to having already been victimized by a cyber attack, fear is the next best motivator when it comes to businesses taking concrete steps to protect their valuable digital assets, and terrorist is certainly a buzzword that conjures fear.”
The personal connection attackers covet
“In this digital world, it’s easier than ever for an attacker to gather the details that make spear phishing so effective,” warns Caruso. “A WHOIS lookup for instance can give an attacker precious contact information, like names, phone numbers and email addresses of administrative personnel responsible for the organization’s Web presence. Online company profiles can give attackers an overall view of a business’s hierarchy, and again, often with names, pictures and contact information right there for the taking. Press releases can give easy insight into current events within an organization which can then be used to devise an email that makes perfect sense to the target, exponentially increasing the chance it will be opened, read, and interacted with. And that’s all it takes for malware to be introduced, which depending on the payload, can lead to any kind of cyber attack imaginable. Add social media to the mix, and the personal touch can become even harder to spot. When John posts on his Facebook account that he will be vacationing in the islands for two weeks and an email comes to his boss while he’s gone that has a spoofed header to look like it is coming from John’s email address that says, “The islands are great, check out this view,” chances are good John’s boss will open it, open the attachment, or follow the link, or do whatever “John” asks him or her to do. And that’s it – game, set, match - nothing fancy, nothing technical, just brutally effective. So of course cyber terrorists are interested, just like every other cyber criminal prowling in the dark corners of the digital landscape.”
Without urgency, count on an emergency
“What really shocks me is how many companies I see that have absolutely no training or awareness programs in place that talk about social engineering threats - at least one in three. Others, that at least talk about it, often miss key elements and don’t really drive the point home with any real enthusiasm. So awhile back we started crafting simple phishing emails as part of our penetration testing program and found that when you have the evidence in black and white, managers, directors and executives suddenly feel a little real fear. And ever since we started doing that, we kept evolving the process to incorporate different types of social engineering methods as well, like pretexting (assuming a fake identity), baiting (leaving manipulated digital media behind hoping for a “curiosity insertion” into a network system), phone calls, and full scale spear phishing expeditions with all the bells and whistles, like an accompanying phony corporate website. To date, no client has ever walked away from a GDF social engineering exercise without access credentials landing in our hands,” says Caruso.
Getting everyone on the same page
“We can also put together follow-up training classes tailored to a client’s unique weaknesses, which we expose during our penetration testing,” Caruso adds, “and when you have a group in front of you with list in hand of how they were just essentially compromised, let’s just say the focus and attention is very different than a yawn-fest morning meeting. We can also review policies and procedures to make sound recommendations on how to strengthen them and help clients leverage many more little tricks of the trade that bolster awareness and operational security. And yes, social networking and all the new vulnerabilities it can introduce are also covered. So like I said, maybe the specter of real enemy-of-the-state type terrorists being in the game will help spark action in some of those who just haven’t gotten on board with the realities of today’s cyber threat landscape yet.”
Professional help
*Global Digital Forensics is a recognized industry leader in the fields of computer forensics, cyber security and emergency incident response, with years of experience assisting clients in the government, banking, healthcare, education and corporate arenas. For a free consultation with a Global Digital Forensics specialist, call 1-800-868-8189 about tailoring a cost-effective plan which will meet your unique needs, without wasting resources on solutions you simply don’t need. Emergency responders are also standing by 24/7 to handle intrusion and data breach emergencies whenever and wherever they arise. Time is critical if a cyber incident has occurred, so don’t hesitate to get help. For more information, visit our cyber security page.
Disaster Ready
It’s a pattern that won’t relent anytime soon – when a deadly natural disaster strikes anywhere on this planet, cyber scammers will immediately be thinking up ways to leverage human sympathy and compassion for their own personal gain. And on April 30, 2015, US-CERT (United States Computer Emergency Readiness Team) issued an alert titled “Nepal Earthquake Disaster Email Scams,” warning users “of potential email scams citing the earthquake in Nepal. The scam emails may contain links or attachments that may direct users to phishing or malware infected websites.”
The worst kind of scoundrel
“It only takes one successful phishing email for an entire network to become compromised,” said Joe Caruso, founder and CEO/CTO of Global Digital Forensics (GDF), a premier national provider of cyber security solutions headquartered in New York City. “People tend to let their guard down a little bit when confronted with a tragic, heart-wrenching event. That's why all those emails start circulating with fictitious charities and aid groups every time a natural disaster takes place. They play on people's innate goodness to further their own devious ends. It makes me mad on two fronts; one, reputable organizations which are really helping people get readily dismissed for fear it is some kind of scam, and two, they victimize people that are trying to do something good. The victims don't only get swindled out of a donation, but they probably also gave the attacker valuable information or further access in the process, depending on the malware payload, which can lead to further problems down the road, both at home, and at work."
For many attackers, it’s go big or go home
"Many times the prize an attacker is after is just not a quick, dirty buck, it’s much bigger than that," warns Caruso, “it’s about gaining a foothold in corporate networks which they can leverage in hopes of finding an even grander opportunity to milk for all it’s worth, whether through theft, espionage, or extortion. All they have to do is design a clever phishing email and maybe even a matching website in the aftermath of a disaster event and wait for human decency to compel someone to take the bait by clicking on a link, opening an attachment or entering credentials. From there it obviously can have devastating consequences for any business, from getting spyware, ransomware or any other kind of nasty malware you can think of past perimeter security, whether directly or piggybacking on a mobile device like a smartphone or tablet, which many organizations now allow as part of the BYOD (Bring Your Own Device) explosion we’ve seen over the last couple of years.”
Cyber-based social engineering attacks have to be a main focus
“When we do cyber penetration testing for businesses, we also offer a thorough social engineering component. And by that I mean we design phishing emails, set up dummy sites and go through all the same steps an attacker would to show businesses where their weak points are on that front and just how serious a threat it is, so that employees can be better educated and trained, and policies and procedures can be updated, revised and refined. It's not uncommon for us to get 70% or more of our targets to fall for our social engineering tactics, which are modeled after real-world attacks in use every day. Add a disaster element, and it just makes it that much easier,” says Caruso. “At that point it's just about watching and counting how many people just gave us complete access to the business network, to steal, deliver a malicious payload, or do whatever else we would want to do if we were actual attackers."
While GDF penetration testing and vulnerability assessments are invaluable before an attack occurs, sometimes attackers will find that one weak link in the chain and get through. Again, it just takes one employee to unlock the gates. So if an intrusion event does occur, how a business responds will likely make the biggest difference in just how damaging the aftermath of the intrusion or data breach will be. Global Digital Forensics has emergency incident response teams ready to answer the call 24/7, and with responders positioned strategically across the country, and the globe, GDF's response times are unrivaled in the industry.
*Global Digital Forensics is a recognized industry leader in the fields of computer forensics, cyber security and emergency incident response, with years of experience assisting clients in the government, banking, healthcare, education and corporate arenas. For a free consultation with a Global Digital Forensics specialist, call 1-800-868-8189 about tailoring a cost-effective plan which will meet your unique needs, without wasting resources on solutions you simply don’t need. GDF’s emergency responders are also standing by to handle intrusion and data breach emergencies whenever and wherever they arise. Time is critical if a cyber incident has occurred, so don’t hesitate to get help. For more information, visit our cyber security page.
>
By definition, a CIO’s responsibility is to support the computer systems, technology and data for the enterprise relying on their judgement and expertise to keep digital assets and environments secure and running smoothly. But according to an article published in National Mortgage News on April 22nd, 2015, CIOs can many times actually be doing a disservice to their responsibilities by focusing too heavily on making sure all the i’s are dotted and t’s are crossed when it comes to company policy and industry best practices, and not enough focus on getting an outsider’s perspective regularly.
Best practices and sound policies are of course instrumental to effective cyber security, but they are just playbooks, playbooks that many hackers know inside and out as well, from common defense tactics to widely used emergency response practices. What cyber security professionals from outside the organization bring to the table is a fresh look from a real-world perspective, and that’s not just instrumental, it’s crucial.
Social engineering, beating the human element
Joe Caruso, founder and CEO/CTO of Global Digital Forensics (GDF), a premier national provider of cyber security solutions headquartered in New York City, has helped businesses of all sizes navigate the ever evolving cyber threat landscape since the infancy of the Internet, and if there is one thing he has seen proven time and time again, it’s that, “cyber security does not come in a one-size-fits-all solution, and that’s a problem when security is looked at through a purely academic lens. Trust me, the real world of cyber threats is far more brutal than what you’ll learn about in the halls of academia, and when the stability and success of an entire organization rests in the balance, the stakes are just too high to not approach the problem from a real-world cyber attacker’s point of view. If there are six words that need to get pounded into the heads of CIOs responsible for cyber security as often as possible, they are social engineering, social engineering, and social engineering. That’s how even goliaths that have every resource and security technology available to them still manage to get bested and victimized, from Target, to Sony, to Anthem and beyond.”
First assess, then test
Comprehensive cyber threat assessments and penetration tests by Global Digital Forensics are designed to look at the entirety of the big cyber-security picture. On the cyber threat assessment side, GDF takes a look at all those i’s and t’s CIOs love so much, by reviewing and understanding existing policies, procedures and enforcement, looking at any specific regulatory compliance issues a client may face in their particular industry, mapping the digital architecture and addressing the whole scope of it, including the burgeoning problems related to the increasing popularity of BYOD (Bring Your Own Device) policies, understanding the intricacies of the daily data flow, making sure emergency response plans are well designed to effective and fast, and helping clients recognize and remediate any other issues that may be found.”
The right way to really test cyber security is from a hacker’s perspective
“On the penetration testing side, GDF assumes the role of a real-world attacker, launching simulated cyber attacks just like the ones they would use. The tests get customized to a client’s unique situation, which can include everything from realistic and advanced spear phishing campaigns, to devious and clever ways we’ve devised to get a “GDF-infected” USB stick inserted into a target network, and much more. We take great pride in the fact that, so far, we have a 100% success rate when it comes to infiltrating a targeted network. And there is nothing more effective than actually showing a CIO, an executive, a manager, or even an employee that we did get by them, here’s how and here’s how to fix it. It’s also not unusual for us to then get retained to give cyber security awareness seminars for the entire organization afterward, and I can tell you that all eyes are forward and paying attention when you successfully phished 60-70-80% or more of the company, or can point out how many were fooled into inserting one of our “infected” USB sticks, effectively compromising the network. And if you can raise that awareness and make it stick, you already won more than half to the battle when it comes beating cyber attacks at the source,” Caruso says. “Those are just some of the tricks in our bag, but like today’s hackers, there’s always more things we can dig out of our arsenal to get the job done right for any unique situation and identify any weak links in the chain.”
It just takes one misstep for a disaster to unfold
“If you plug the holes which can lead to that initial intrusion that hackers use as the springboard to start moving sideways across the network, make everyone aware of their responsibilities and understand the ramifications even a single lapse in judgment can have and show them how to avoid being an unknowing accomplice to a cyber attacker, for both businesses and critical infrastructure alike, everyone will be safer in the long run,” says Caruso, “including whomever is filling that monumentally important position of Chief Information Officer for an organization in today’s dangerous digital world.”
*Global Digital Forensics is a recognized industry leader in the fields of computer forensics, cyber security and emergency incident response, with years of experience assisting clients in the government, banking, healthcare, education and corporate arenas. For a free consultation with a Global Digital Forensics specialist, call 1-800-868-8189 about tailoring a cost-effective plan which will meet your unique needs, without wasting resources on solutions you simply don’t need. Emergency responders are also standing by 24/7 to handle intrusion and data breach emergencies whenever and wherever they arise. Time is critical if a cyber incident has occurred, so don’t hesitate to get help. For more information, visit our cyber security page.
On April 14th, 2015, Symantec released Volume 20 of their Internal Security Threat Report, which they say, “exposes a tactical shift by cyberattackers.” With everything from frightening numbers on how many new malware variants were introduced in 2014 - almost a million a day - to how long it took for Zero Day threats to be identified and patched by prominent manufacturers – as long as 204 days – it is abundantly clear that doing business in a digital world can be fraught with peril, and that businesses, regardless of size or technical savvy, have to get a firmer grip on the reigns than ever before when it comes to cyber security on the home front.
Old Story with New Twists
“It’s excellent information and should be food for thought for every organization relying on digital information, in other words, just about everyone, but it’s far from a new story,” says Joe Caruso, founder and CEO/CTO of Global Digital Forensics (GDF), a premier national provider of cyber security solutions headquartered in New York City, “Since the infancy of the Internet, cyber attackers have never stood still regarding the tactics, tools and techniques they employ to achieve their endgame, whether it’s theft, extortion, destruction, or espionage. They are always refining techniques to avoid detection, and they are always raising their game in finding new ways to get that first foot in the door. Mass spam campaigns have given way to more targeted and much more effective spear phishing campaigns, and social media has also become a major conduit for explosive growth in cybercrime circles. Not only are they leveraging the “trust factor” social media inherently provides to get people to visit malicious sites and/or download malware directly, but they are increasingly using the personal details so many users make freely available online on sites like Facebook to help them craft their phishing and spear phishing campaigns. Whether it's coming from Aunt Mildred or John in accounting, a target is far more likely to read that email and open a malicious attachment when it looks like it's coming from someone they know and trust.”
Best Practices Significantly Improve Chances to Thwart Cyber Attackers
“From a pizza shop to a military defense contractor, cyber security has to be part of the business plan today. Avoiding that reality is a recipe for disaster,” warns Caruso, “but we also understand every client is different – different needs, different environments, different skill levels and different objectives. But some things are always constant, like the need to assess, test and address cyber security concerns with unyielding regularity. And that’s what we help clients do. Whether you’re a multinational corporation, or a mom and pop shop, you have to know what kind of threats you are particularly vulnerable to. Are mobile devices in play? Are PoS systems involved? Are seasonal or transitional workers part of the picture? Are there regulatory compliance concerns in your particular industry? Are you compliant? Is malware already present on the network? Are all system and application updates current? It’s all part of our vulnerability assessments. Then we move on to penetration testing, which is basically us assuming the role of a real-world attacker and testing your system defenses. Can we craft a spear phishing campaign that gets employees, managers or owners to take the bait and divulge credentials or open an attachment? Can we infiltrate the network with a brute force attack? Can we simply guess admin credentials because of poor password policies? It’s all part of the mix. And of course we also do deep scanning for identifying and eradicating any malware problems that may already exist, including special testing for zero-day threats. When all of that is done, we generate a report which details everything we found, and provides specific remediation recommendations for each."
"We can also assist with the entire spectrum of emergency incident response," says Caruso, "from helping develop emergency response procedures from scratch if none exist, to strengthening policies and procedures already in place. We also have experienced cyber emergency responders on call 24/7 who are strategically positioned across the country to be able to respond quickly and effectively in the event the unthinkable happens and your network is breached, which when done right almost always significantly reduces the costly aftermath of a successful attack. We can also assist with awareness training, the importance of which should never be overlooked, especially since the most common vector of infiltration is the most easily fallible one, the being behind the keyboard and screen, the human element. In a nutshell, we help clients get on board with best industry practices to make them stronger going forward, whatever the starting point.”
Getting the Right Help Is Essential for Better Cyber Security
*Global Digital Forensics is a recognized industry leader in the fields of computer forensics, cyber security and emergency incident response, with years of experience assisting clients in the government, banking, healthcare, education and corporate arenas. For a free consultation with a Global Digital Forensics specialist, call 1-800-868-8189 about tailoring a cost-effective plan which will meet your unique needs, without wasting resources on solutions you simply don’t need. Emergency responders are also standing by 24/7 to handle intrusion and data breach emergencies whenever and wherever they arise. Time is critical if a cyber incident has occurred, so don’t hesitate to get help. For more information, visit our cyber security page.
A tragic day
For the friends and loved ones of the 150 people who perished on Germanwings Flight 9525 when it slammed full speed into a desolate and largely inaccessible landscape high in the French Alps on March 24, 2015, the best chance of learning exactly what happened is going to come from electronic evidence.
As reported by CNN in this article on April 2nd, 2015, investigators have found incriminating evidence on a tablet and home computer system belonging to Andreas Lubitz, the co-pilot of the doomed flight. According to the Internet history found on those devices, Lubitz had looked up suicide and cockpit door security in the days preceding the crash, further cementing investigators’ original belief that he had intentionally piloted the plane to its fiery end after the first black box recovered revealed Lubitz had sealed himself in the cockpit behind the security door while the pilot could be heard outside banging on the door and yelling, “Open the Goddamn door!”
On April 3rd, it was then reported by Associated Press that the second black box was discovered and revealed Lubitz had actually accelerated the plane on its decent, implicating his willing part in this catastrophic disaster even further. “When there are no eyewitnesses to a tragic event, it’s often digital evidence that will end up answering the hard questions; who what, when, where, how, and with luck, even why,” says Joe Caruso, founder and CEO/CTO of Global Digital Forensics (GDF), a premier national provider of electronic discovery (eDiscovery) and digital forensics solutions headquartered in New York City. “The key is knowing what to look for and where to look for it, how to acquire it correctly, and how to understand and use the information found to get to the truth, and that takes advanced training, steadfast discipline, the right tools and the right experience to pull it all together into useful evidence investigators and litigators can rely on to make their case.”
Crash forensics and beyond
“As the world waits for answers, the digital truth found through the science and technology of computer forensics could still reveal many things,” says Caruso. “Even though there was heavy fire and impact damage to most things at the site, there is still a fairly decent chance that more electronic devices with crucial evidence will be found. If there was that kind of commotion on the plane, as evidenced by the first black box, there is a good chance that passengers on board recorded video and/or audio that will prove key to the investigation. These days just about everyone has a smartphone, and you’d be surprised at just how resilient the memory in those kinds of devices can be. We’ve forensically examined devices out of fiery car crashes before which revealed distracted drivers that were texting or talking on the phone at the time of impact, so it’s certainly not out of the question in a case like this for unexpected but crucial evidence to still be on the horizon, but it’s going to take a lot of time and persistence from everyone, whether they are the ones scouring the harsh environment on the side of that mountain for any devices they can find, or the investigators and analysts that will have to piece together what those devices contain. And it’s not just air disasters, the same goes for every-day traffic accidents too, from computing devices individuals were using, to on-board computers in vehicles that work a lot like that second black box found, telling you everything the vehicle was doing right up until the moment of impact.”
Dissecting a Life in the Digital World
“It’s gut-wrenching when a tragedy like this occurs and my heart goes out to the victims, their friends and their families,” said Caruso. “Unfortunately, it’s not the first time unfathomable acts like this have occurred, and unfortunately it will not be the last. It’s going to take real investigative elbow grease and a lot of connecting the dots to make any kind of sense as to the motivation and mindset of an obviously disturbed individual. The good news is that the chances of finding some kind of digital trail which will help investigators put the pieces of this young man’s life together and start answering the burning question of why are great. Lubitz was 28 years old; how many 28 year olds do you know that aren’t plugged in to the digital realm in some form or fashion, and that means, more answers will certainly be coming. Nothing will bring those lost souls back, but hopefully at the very least those kinds of answers will give all those grieving some modicum of closure in the end, as well as give air traffic authorities some insight on how to prevent a similar tragedy like this from ever occurring again in the future.”
The Digital evidence experts
*Global Digital Forensics is a recognized leader in the fields of computer forensics, eDiscovery, cyber security and emergency incident response. To speak with a digital evidence specialist about your unique situation, or any other computer forensics, eDiscovery or cyber security needs involving Electronically Stored Information (ESI), call 1-800-868-8189, or visit our digital forensics page.
An article in Fortune on Monday, March 23, 2015 highlighted a problem which could prove critical to organizations that deal with PCI (Payment Card Information); Why system testing, a critical aspect of data security, is worsening. Using numbers from Verizon’s 2015 payment card industry data security report, every major category out of the twelve measured improved, barring one – vulnerability scanning and penetration testing.
“With all the craziness that has gone on in the retail industry in the last couple of years, like the headline-making mega-breaches that hit goliath retailers like Home Depot and Target and exposed the PCI of tens of millions of customers, you would think scanning for vulnerabilities and testing cyber defenses would take a pretty high spot on the list of things to do for PCI reliant organizations,” says Joe Caruso, founder and CEO/CTO of Global Digital Forensics (GDF), a premier national provider of cyber security solutions headquartered in New York City, “but unfortunately, the results of Verizon’s study shows that unbelievably, that doesn’t seem to be the case.”
Regulatory compliance is not an option, it’s a necessity when a business deals with PCI
“PCI DSS (Payment Card Industry Data Security Standard) regulatory compliance was devised to establish ground rules for any entity involved in taking, maintaining, and/or using payment card information. And in those rules it is explicitly stated that organizations need to run a vulnerability scan at least once every three months, and a penetration test at least once a year,” says Caruso, “and if the organization lacks the expertise, tools or personnel internally to do it, and many do, a qualified third party vendor is supposed to be called in to get the job done right. The problem is, especially in the retail business, many of the decision makers find the prospect daunting for many reasons, like they think it will be an unruly and exorbitant expense, that they will have to devote internal personnel to the task full time, that they’ll experience too much downtime while the scanning and testing are going on, and all kinds of other thoughts which are really not the case. We’ve done hundreds of vulnerability scans and penetration tests for customers in just about every industry you can think of, from healthcare and financial institutions, to retailers and law firms, both onsite and remotely, and 99% of the time they are shocked at how easy, affordable, and most importantly, helpful the whole process is. In the end we will have provided a detailed remediation plan which lays out step-by-step what needs to be done to resolve any issues found. And it’s not going to take six figures or months to accomplish the scanning and testing, and they’re not going to have to shut down the business while we get the job done. If it needs to be done after hours, we’ll do it after hours, and like I said, we can often even do most of it, if not all of it, remotely. Our job is not to create stress, it’s to reduce it, which for any retailer should always be a byproduct of a significantly improved cyber security posture.”
Regularity is not only required, it’s essential for business survival in today’s digital world
“Threats are evolving every day, technologies changes all the time, new business needs and practices continuously emerge, and all of that has to be accounted for,” warns Caruso. “That’s what we help clients do, assess their vulnerabilities and test for weak links in their cyber security chain with proven state-of-the-art vulnerability scanning and penetration testing, from both an insider and outsider perspective. We can also assist in the emergency response arena, flexing an organization’s response plan to see how it stands up to real-world threats and isolate the shortcomings, and if a plan doesn’t exist, we’ll help them devise one from scratch. The biggest key is regularity, what would have worked last year will probably not stand up to today’s threat landscape, and what works today will undoubtedly be challenged by the threat vectors that evolve over the next few months or year. Like it or not, that’s today’s cyber reality, so either businesses have to be prepared to step up and play the game right, or pack up, take their ball and go home, because they will not win in the long run if they’re not ready to take the field on any given day. And in the world of PCI, losing that game can cost a business everything.”
*Global Digital Forensics is a recognized industry leader in the fields of computer forensics, cyber security and emergency incident response, with years of experience assisting clients in the government, banking, healthcare, education and corporate arenas. For a free consultation with a Global Digital Forensics specialist, call 1-800-868-8189 about tailoring a cost-effective plan which will meet your unique needs, without wasting resources on solutions you simply don’t need. Emergency responders are also standing by 24/7 to handle intrusion and data breach emergencies whenever and wherever they arise. Time is critical if a cyber incident has occurred, so don’t hesitate to get help. For more information, visit our cyber security page.
As reported on Thursday, March 19th in the Boston Globe, Day 10 of the Boston Bombing Trial saw attention shift to the digital world, with prosecutors introducing evidence meant to give the jury a glimpse into the mind of a young man accused of being a radical jihadi and self-motivated participant in one of the most horrific acts of terrorism ever carried out on American soil.
Joe Caruso, founder and CEO/CTO of Global Digital Forensics (GDF), a premier national provider of electronic discovery (eDiscovery) and digital forensics solutions headquartered in New York City, and his team of certified computer forensics analysts, have helped attorneys and investigators navigate the world of digital evidence many times, and knows well the hurdles and pitfalls that have to be overcome before potential can be turned to potency when ESI (Electronically Stored Information) is involved.
“With any trial involving digital evidence, especially one with as high a profile as this one, every conceivable aspect of the data found is going to be scrubbed and scrutinized to the limits. From acquisition and identification, through analysis and production, just one misstep by the digital forensics experts along the way can render everything found completely useless. A mishandled chain of custody, missing details in a report, shortcuts, the software and hardware used, not using court accepted and repeatable methods, any or all of it can leave critical evidence tainted and inadmissible,” says Caruso, “and that’s before even getting into the nitty-gritty of the actual evidence.”
What kinds of things can be found “in the data?
“In this case, the prosecution is obviously leaving no digital stone unturned, and they produced some strong evidence they believe to be in their favor, taken from laptops, desktops, thumb drives, smartphones and anything else they could get their hands on. Articles on ‘How to Make a Bomb in the Kitchen of your Mom’, speeches by radicals, English language Al-Qaeda propaganda, it all helps paint the portrait they are trying to, but as any attorney can tell you, electronic discovery is never that easy,” says Caruso. “When Tsarnaev’s defense team gets up to bat next week, their sole objective is to do everything in their power to cast doubt on the evidence laid out by the prosecution, who contend that Tsarnaev was radicalized on his own accord, and not simply as a result of his big brother’s influence. And they do have a leg to stand on, as it seems multiple people used many of the systems and devices which held the evidence. They will not only try to pick apart the way in which the evidence was acquired and analyzed, they will try to put every other possible person in the wheelhouse when the most damning evidence was created, accessed, viewed or modified. But with many things duplicated on multiple systems, devices and storage media, it could be an uphill battle, because there are many clues in many places these days in the world ESI. Location data from a smartphone could put someone in a certain location and exclude another, metadata (data about data) from photographs on some devices can give you time-stamped GPS coordinates showing exactly where and when it was taken, timelines from social media entries, emails and texts can be built, user logon information can be extracted and analyzed to determine usage patterns, intricate timelines can be established, the list goes on and on. It will be a dogfight no doubt, which in the end could come down to the expert witnesses on both sides, because when push comes to shove, the jury is going to be the deciding factor, and the expert that best lays out their findings in an understandable, meaningful and effective way is going to do more than anything to put a jury’s doubts to rest.”
In this digital day and age, Global Digital Forensics is formidable ally when it comes to the identification, acquisition, analysis, production and expert testimony relating to electronic evidence, always using only industry proven and accepted methods and procedures so any evidence found remains pristine and admissible. GDF’s experience and savvy in dealing with some of the most complex ESI situations imaginable and unrivaled expertise during those initial and crucial tone-setting steps, like the meet and confer or discovery conference, will ensure the best chance for litigation success. Because with Global Digital Forensics on the job, those are opportunities to seize an early advantage, not a burden to be endured. And because Global Digital Forensics is highly experienced in virtually any type of digital media, should the trail lead to networks, smartphones, tablets, mainframes, webmail or even social networking sites, GDF can seamlessly transition to help clients find, and make the most out of, virtually any type of electronic evidence involved, wherever it resides.
*Global Digital Forensics is a recognized leader in the fields of computer forensics, eDiscovery, cyber security and emergency incident response. To speak with a digital evidence specialist about your unique situation, or any other computer forensics, eDiscovery or cyber security needs involving Electronically Stored Information (ESI), call 1-800-868-8189, or visit http://evestigate.com for more information.
On March 12th, Forbes published an article titled #1 Cyber Security Threat to Information Systems Today, which was based on findings of a survey commissioned by Sungard Availability Services. So what claimed that dubious top spot? Vulnerable web applications, according to 55% of the respondents.
Converging factors
“There are a few factors that converge to make applications a tricky cyber security concern for many organizations,” says Joe Caruso, founder and CEO/CTO of Global Digital Forensics (GDF), a premier national provider of cyber security solutions headquartered in New York City. “First is sheer volume. There are so many web apps today which organizations use on so many different platforms that the numbers alone can be dizzying, not to mention the resources, experience, personnel and tools needed to effectively keep tabs on the security aspect of them all. Then there is the sea of developers building apps who come out of the woodwork from every corner of the globe with promises to deliver effective customized apps at bargain rates. But far too often, security is not entrenched in the DNA of these coders. In their world, functionality, convenience, and effectiveness are markers of success, and they often deliver those aspects very well. But what good is a Lamborghini if it has no brakes or safety features? By the same token, if security isn’t baked into the development cycle of an application, an organization can find themselves with a wide open door for hackers to exploit their most sensitive and valuable data, leaving a costly, tangled mess to rival the fireball that Lamborghini would be destined for.”
How can GDF help clients mange the risks posed by applications?
The most effective application security measures are about prioritizing threats, both from a cause and effect standpoint. Full in-depth testing of every single application is normally not an option. It may be for a small organization with a very limited amount of apps, but for larger organization with thousands on the books and new ones getting implemented all the time, the man hours and costs associated with that kind of testing would be prohibitive to say the least. But all apps are not created equal. Some pose an insignificant threat, they don’t relate to critical company information or client data, or don’t provide the means to provide a gateway to an intruder, these would be a very low priority, whereas others may be a medium or high risk and should be looked at accordingly. But that still leaves a lot of room open for interpretation and still requires specialized tools, methods and expertise to approach the problem with any real hope for success.
Assess, test, address
A professional vulnerability assessment to determine what risks exactly are posed by each application is essential, coupled with comprehensive penetration testing on every application which is determined to be susceptible to outside attack. Experts like Global Digital Forensics that specialize in testing, identifying, prioritizing, and remediating threats posed by vulnerable applications are key. Or as Caruso put it, “There are not many places out there that have the resources, professional affiliations, personnel, tools and knowledge base that we have at our disposal. We live and breathe this stuff, always staying on top of the newest trends and threats. So when we’re done with our application security testing, our clients can breathe a lot easier by knowing exactly where they stand, what they need to watch out for, and what it’s going to take to elevate and maintain the security of all those applications they are relying on to not only survive, but thrive in today’s competitive digital world. Our initial consultations are free, so there is nothing to lose to find out just how painless and reasonable we can make the entire process, so give us a call and see for yourself, because the alternative can be truly frightening, and costly.”
GDF can Help
*Global Digital Forensics is a recognized industry leader in the fields of computer forensics, cyber security and emergency incident response, with years of experience assisting clients in the government, banking, healthcare, education and corporate arenas. For a free consultation with a Global Digital Forensics specialist, call 1-800-868-8189 about tailoring a cost-effective plan which will meet your unique needs, without wasting resources on solutions you simply don’t need. Emergency responders are also standing by 24/7 to handle intrusion and data breach emergencies whenever and wherever they arise. Time is critical if a cyber incident has occurred, so don’t hesitate to get help. For more information, visit our cyber security page.
On Thursday, February 26th, Forbes published an article titled DIY Phishing Kits Make It Easy For Scammers To Steal Your Data, which stresses the ease with which just about anyone can get their hands on a DIY phishing kit, or any kind of malware kit for that matter. But it also touched on another important point about how everyone’s cyber security is intertwined when it covers some ways these kits are often implemented, “like compromising legitimate content management systems or blogs in order to install the kit on clean servers. They do this by exploiting vulnerabilities such as SQL injection bugs or remote code execution flaws in these sites.”
Joe Caruso, the founder and CEO/CTO of Global Digital Forensics (GDF), a premier national provider of cyber security solutions headquartered in New York City, has seen it all play out first hand many times. “Raising social engineering awareness across an entire organization on how to avoid attacks like phishing campaigns is a basic must in today’s digital society, and we help clients do that all the time. Because in truth, the human element, the user, is almost always the weakest link an organization’s cyber security chain. Some of the biggest breaches in history have started with a simple phishing email, allowing hackers to do everything from stealing credentials for network access, to delivering basically any kind of malware payload you can imagine, be it spyware for espionage, viruses for destruction and chaos, or even ransomware to hold your data hostage until the ransom is paid.”
You're not alone
“What many organizations don’t realize is even if they are not the targets of a particular phishing campaign, weaknesses in their security can make them an unwitting accomplice in propagating the problem when an attacker uses their compromised site or network to help launch their campaign against others,” says Caruso. “To some degree, every business with an online presence plays a part in the grand scheme of everyone else’s security, and that’s why it’s so important to stress the basics. Getting those down cold will thwart over 95% of the cyber threats out there, and the more businesses that get fully on board with at least nailing down the basics, the better off we all are.”
The power of security basics
“The first steps to getting that done are knowing where you stand right now, understanding the threats you face, and identifying and eradicating any threats which already may be present – regularly; all of which we can help with, from professional vulnerability assessments and comprehensive penetration testing with a focus on social engineering, to deep scanning networks and testing applications to significantly reduce the chances an organization can be exploited. Cyber attacks can cripple any business, no matter how large or small,” says Caruso, “so don’t rely on chance as a security strategy, get professional help today. Otherwise, it may not only be you paying dearly, the digital world connects us all.”
*Global Digital Forensics is a recognized industry leader in the fields of computer forensics, cyber security and emergency incident response, with years of experience assisting clients in the government, banking, healthcare, education and corporate arenas. For a free consultation with a Global Digital Forensics specialist, call 1-800-868-8189 about tailoring a cost-effective plan which will meet your unique needs, without wasting resources on solutions you simply don’t need. Emergency responders are also standing by 24/7 to handle intrusion and data breach emergencies whenever and wherever they arise. Time is critical if a cyber incident has occurred, so don’t hesitate to get help. For more information, visit our cyber security page.
Last weekend, on Valentines’ Day, The New York Times reported on revelations made by a prominent Russian Security firm about an organized cybercrime ring, dubbed the “Carbanak cybergang,” who they claim conducted a sophisticated long-term cyber-heist involving over 100 banks and financial institutions in over 30 countries, with a haul estimated to be anywhere in the range of $300 million to triple that figure.
“It sounds like something out of a Hollywood script,” says Joe Caruso, the founder and CEO/CTO of Global Digital Forensics (GDF), a premier national provider of cyber security solutions headquartered in New York City, “but when you consider most of the world’s wealth today exists exclusively in 1s and 0s, is it really any wonder there are thieves out there licking their chops and hatching sophisticated plans to get their hands on some of it, and that there are some with the skills and determination to see it through? The truth is the balance always tilts towards the attacker in the cyber world - security personnel have millions of holes to plug, but attackers only need to find one.”
The lure of easy money never fades
“Turning data into a cash is typically not instantaneous for hackers,” says Caruso, “buyers have to be found, currency has to get exchanged, and it all has to be done while remaining anonymous to avoid detection at every step. But if hackers can heist hard currency straight from a golden goose and remain undetected, that’s like a hitting the mega jackpot, with free pulls again the next day. These kinds of thieves don’t need to figure out how to lug gold bars out of a vault, they just need to manipulate data the right way and presto, they can just have the bank deliver it to their account, or better yet, just start spitting it out in cash at an ATM whenever they’re ready for it, all without tripping a single alarm. But before any of that black magic can happen, a few things are needed.”
Even the most sophisticated cyber attacks usually have humble beginnings
“First and foremost, attackers need to find a way to get their foot in the door, and they have two choices,” says Caruso. “Either they can try to wade their way through a tangled web of stiff security measures, or they can find a human patsy to fool into unwittingly giving them the keys to the castle so they can walk right in the front gate. That’s what makes social engineering attacks like phishing and spear phishing campaigns so dangerous for organizations and so preferred by hackers, it only takes one person on the inside to bite on the bait and the enemy is in, doing reconnaissance and laying the groundwork for a large-scale attack. From there it’s all about stealth, persistence and patience.”
“Our vulnerability assessments and penetration testing plans are designed to find weak links in the security chain, raise awareness enterprise wide against social engineering ploys hackers commonly rely on, and uncover any existing and/or resident threats and thoroughly eradicate them, all with an eye on the appropriate regulatory compliance issues many clients face in their industries, like GLB (Gramm Leach Bliley) compliance for the financial industry for instance. From proactive solutions to help thwart today’s cyber threats, to a proven track record as emergency incident responders, we certainly have plenty of experience helping financial clients navigate not only the dangerous cyber threat landscape they face on a daily basis, but all the potential pitfalls and headaches that can arise should the unthinkable happen and a breach is successful. We can customize solutions to fit any client’s real needs, it’s just a matter of picking up the phone to get the ball rolling – with sooner being far better than later when it comes to combatting cyber threats.”
GDF can help
*Global Digital Forensics is a recognized industry leader in the fields of computer forensics, cyber security and emergency incident response, with years of experience assisting clients in the government, banking, healthcare, education and corporate arenas. For a free consultation with a Global Digital Forensics specialist, call 1-800-868-8189 about tailoring a cost-effective plan which will meet your unique needs, without wasting resources on solutions you simply don’t need. Emergency responders are also standing by 24/7 to handle intrusion and data breach emergencies whenever and wherever they arise. Time is critical if a cyber incident has occurred, so don’t hesitate to get help. For more information, visit our cyber security page.
On February 4th, Anthem Inc., the second largest insurer in the US, revealed that they had been the victim of a massive data breach which exposed the records and PII (Personally Identifiable Information) of roughly 80 million current and former members and employees, including information like names, birth dates, member IDs, email addresses, Social Security numbers, addresses, phone numbers, and even employment information. One week later, on February 11th, Reuters ran a story about security industry experts warning 2015 could be 'Year of the Healthcare Hack.' Joe Caruso, the founder and CEO/CTO of Global Digital Forensics (GDF), a premier national provider of cyber security solutions headquartered in New York City, has worked with healthcare providers of all sizes and has seen many times how this kind of PII can be leveraged by hackers to orchestrate all kinds of attacks, especially targeted phishing campaigns, which he says, ”can be the springboard for almost every type of cyber attack imaginable, from gaining credentials and access to personal and/or corporate accounts, to being targeted to receive fraudulent solicitations for non-existent products and full-blown identity theft.
The business of hacking is like the oil business
“In general, hackers are a lot like shady oil prospectors, says Caruso. “They’ll start by blindly poking holes in all kinds of organizations’ cyber security until they find a well, and if they find one, they’ll try to cultivate it for all it’s worth. But if someone else finds an area that turns out to be on a gusher of premium quality crude, they’ll happily jump on the bandwagon and go after every bit of adjacent property so they can tap that same well as quickly as possible before its bled dry.”
“At the end of 2013, Target was the gusher in the retail business after tens of millions of customer credit cards were compromised, and massive breaches followed the retail industry throughout 2014, with giants like Home Depot and a slew of others accounting for tens of millions more. But in the aftermath, security was not only tightened, the wholesale prices of compromised card information on the Dark Web started bottoming out as well because the industry started making it harder for thieves to use the compromised card information; supply and demand played a role as well. Their 'sweet crude' turned into 'sour crude' and the prices they were getting reflected that. So on to the next honeypot, like insurers and healthcare providers. Anthem may well have been the new gusher, and you can bet a slew of 'prospectors' are marking their maps to get in on the action. That’s why initiatives are under way, like the one New York's Department of Financial Services announced on February 10th which they are rolling out to try to address a problem they, and the security industry, see on the horizon. Their approach starts with what we’ve been preaching to clients for years – regular, professional cyber vulnerability/risk assessments, like the ones we provide,” Caruso says.
Test, assess, address – early and often
“Cyber vulnerability/risk assessments and penetration testing are not luxuries in today’s age of cyber threats, they are a necessity, and the cornerstone of the foundation effective cyber security is based on," according to Caruso. "When we are called in to improve an organization’s cyber security posture, we start with a thorough cyber threat assessment. That means we look at the entire digital infrastructure and how it fits into an organization’s daily operations, needs and objectives. Are personal devices like smartphones and tablets part of the equation? Is remote access from home by employees a concern that should be on the table? And so on. Then we review all of the policies and procedures in place relating to cyber security, identify the weaknesses and help improve them. If no policy or procedure guidelines exist, we help craft them. If regulatory compliance is part of the picture, we focus on that too. The next step is comprehensive penetration testing, where we take on the role of real-world hackers to infiltrate the client’s network using the same tradecraft real-world hackers would use to compromise a network, from social engineering techniques like phishing and spear phishing campaigns, to brute force attacks and any other targets of opportunity. We’ve never failed to compromise our target during this phase, and that success only serves to make our clients stronger against all comers, as well as raising cyber security awareness every step of the way. And since threats are constantly evolving, doing both of these regularly is crucial, because what worked last year may not be the best approach today.”
Don’t wait until it’s too late
*Global Digital Forensics is a recognized industry leader in the fields of computer forensics, cyber security and emergency incident response, with years of experience assisting clients in the government, banking, healthcare, education and corporate arenas. For a free consultation with a Global Digital Forensics specialist, call 1-800-868-8189 about tailoring a cost-effective plan which will meet your unique needs, without wasting resources on solutions you simply don’t need. Emergency responders are also standing by 24/7 to handle intrusion and data breach emergencies whenever and wherever they arise. Time is critical if a cyber incident has occurred, so don’t hesitate to get help. For more information, visit our cyber security page.
With the success hackers had last year with CryptoLocker, malware which encrypted personal files on a single computer and then demanded payment from the user for the key necessary to decrypt the files, it was only a matter of time before even more malicious variants reared their ugly heads. Well, it looks like that has finally come to pass. Last week, on January 28th, Forbes reported on a story about a Swiss security firm that identified an attack that didn’t just affect a particular computer, but rather it went after the targeted financial organization’s entire Web presence, quietly encrypting their entire database over six months after hackers exploited an application. Once they “turned off the lights,” a demand for ransom quickly followed.
This type of attack actually highlights a couple weaknesses that many organizations have,” says Joe Caruso, the founder and CEO/CTO of Global Digital Forensics (GDF), a premier national provider of cyber security solutions headquartered in New York City. “First, you have the weakness of the application which was initially exploited, and then you have an attack longevity issue, six months of undetected operation, which in this case allowed for enough time for the regularly performed backups to be eventually replaced with the altered databases. Affecting the backups is especially problematic in a ransomware attack, because recovering from backups is often the only resort, next to paying the ransom and crossing your fingers that the attackers will actually release the decryption key to you.”
Application Security Testing
“One of the biggest issues with Web applications is the blind trust many organizations put into the designers from a cyber security perspective,” warns Caruso. “Because in truth, very few app designers really have the background and expertise in cyber security necessary for their apps to stand up to today’s constant onslaught of cyber threats. Their objectives are designing apps that increase efficiency and/or provide convenience, for either the organization internally, or for their customers’ experience. We provide application security testing expressly for this reason, putting an app through the ringer with both eyes focused squarely on the security aspect. If an endpoint app isn’t secure, for instance, it can be a wide open door for attackers to gain access to all sorts of digital assets, which can obviously translate into all kinds of mayhem for the victim.”
Professional scanning and penetration testing performed regularly are paramount for survival in today’s cyber threat landscape
“Effective cyber security will never be in the cards for an organization that approaches it with a set-it-and-forget it mindset,” says Caruso. “Threats change, technology changes, applications and other software are continuously upgraded and changed, personnel changes and a myriad of other variables make digital environments anything but stagnant. It’s the chaos hackers thrive on. That’s why performing deep scans and penetration tests at regular intervals is so important, the more frequently the better. Otherwise, you are basically allowing hackers an opportunity to have free reign on your network for large chunks of time. Yearly is really the absolute bare minimum, bi-annually is obviously twice as good and quarterly even better. We can actually scale penetration testing packages so they cost less individually when an organizations makes a commitment with us to perform them more regularly. We can do this because of the familiarity we will gain with an organization’s data structure, equipment and things like data flow, how everything is tied into the daily operations, familiarity with existing policies and procedures in place and these kinds of things, which we will have to thoroughly go through during the initial testing. This familiarity makes it easier for us to see exactly what is going on, understand what has changed and what needs to be changed, and generally speed up the entire process. In turn, it allows us to not only pass those saving on to the client, but make them that much safer in the long run, especially against long term events, which are usually the costliest for an organization to overcome.”
Relying on luck is a dangerous game to play when it comes to cyber security. Getting the right professionals involved early and often? Now that’s smart business
*Global Digital Forensics is a recognized industry leader in the fields of computer forensics, cyber security and emergency incident response, with years of experience assisting clients in the government, banking, healthcare, education and corporate arenas. For a free consultation with a Global Digital Forensics specialist, call 1-800-868-8189 about tailoring a cost-effective plan which will meet your unique needs, without wasting resources on solutions you simply don’t need. Emergency responders are also standing by 24/7 to handle intrusion and data breach emergencies whenever and wherever they arise. Time is critical if a cyber incident has occurred, so don’t hesitate to get help. For more information, visit our cyber security page.
Email correspondence is second nature in today’s digital world because of all the inherent advantages it affords. Among those advantages it provides a dated written record which can easily located and reviewed at any time, it can be sent in the middle of the night and will be waiting for the recipient whenever they next check their mail, and it can be accessed from just about anywhere in the civilized world on a host of different devices. So it’s no wonder that for most businesses today it is an integral part of daily operations. But what happens when an email account is hacked?
The FBI released a warning for businesses last week, on January 22nd, about a type of scam dubbed the BEC (Business Email Compromise), which they tabulated to have cost businesses worldwide $215 million in losses over 14 months, almost $180 million of which was suffered by US businesses alone. While the BEC scam seems to specifically target businesses working with foreign suppliers and/or businesses that regularly perform wire transfer payments, “the lessons that need to be learned apply to any kind of business that uses email as part of their daily routine,” says Joe Caruso, the founder and CEO/CTO of Global Digital Forensics (GDF), a premier national provider of cyber security solutions headquartered in New York City.
“First and foremost, cyber scams, like most confidence jobs, depend on leveraging trust,” says Caruso. “Compromised email systems and accounts give scammers ample ammunition to do just that, gain the trust of a user, or users, within an organization to help them achieve their endgame, which can be anything from long term cyber espionage campaigns to actual money heists, any of which can devastate a business. Just think about everything you do through email correspondence on a daily basis, and then imagine all of the information you divulge to trusted recipients falling into the wrong hands, the recent Sony hack being a great recent example. They’ll see your invoices, they’ll know when you are going on vacation, they’ll see who you trust and how you interact with each other, they’ll have account numbers and other inside information on your vendors, investors and every other relationship you’ve used email to communicate with. Put all that information in the hands of a motivated hacker and the sky really is the limit to the damage they can do. Spear phishing at that point really turns into something more akin to shooting fish in a barrel.”
Test, Assess, Address
“Spam, phishing and spear phishing have long been the leading ways intruders initially infiltrate business networks, but spotting those bogus emails is getting harder every day, and if they have insider information gleaned from a compromised email account, that task becomes exponentially harder,” warns Caruso. “That’s why we offer an optional social engineering component to our professional penetration testing offerings, because if we can help you test, identify and educate the weakest part of any cyber security chain, individual users, it will significantly strengthen the organization’s overall cyber security posture. The lessons learned from our social engineering testing can help everyone in an organization improve their ability to distinguish between real and fake correspondence, and if we can get that done, they can then easily use old-school easy-factor authentication – pick up the phone and call the right party for verification. That simple 'if you doubt it, call about it' approach can save more headaches and hardships than you can imagine, without killing your budget. The key is getting everyone on the same page on what to watch out for, which we help organizations with every day.”
“The cyber threat landscape is constantly evolving and it can be a daunting challenge to keep up with it all if it is not your prime focus every single day,” says Caruso, “but it is our main focus and it’s what we do best. So give us a call and talk to our experienced security specialists about customized solutions that can help you keep you doing what you do best.”
The Right Experts for the Job
*Global Digital Forensics is a recognized industry leader in the fields of computer forensics, cyber security and emergency incident response, with years of experience assisting clients in the government, banking, healthcare, education and corporate arenas. For a free consultation with a Global Digital Forensics specialist, call 1-800-868-8189 about tailoring a cost-effective plan which will meet your unique needs, without wasting resources on solutions you simply don’t need. Emergency responders are also standing by 24/7 to handle intrusion and data breach emergencies whenever and wherever they arise. Time is critical if a cyber incident has occurred, so don’t hesitate to get help. For more information, visit our cyber security page.
On January 20th, Cisco released their Annual Security Report for 2015. Among the key findings were things like big shifts in the techniques of launching spam attacks to make them more difficult to filter, the rise in popularity of lesser known exploit kits, the trend of combining lesser exploits to cause bigger problems, and users becoming a much more preferred vector for attackers to leverage in order to achieve their endgame of infiltrating business networks. Joe Caruso, the founder and CEO/CTO of Global Digital Forensics (GDF), a premier national provider of cyber security solutions headquartered in New York City, has watched all of these trends play out repeatedly over the last year with real-world clients and says, “There is definitely nothing out of the blue in Cisco’s report, but I am glad they put such a strong focus on the user aspect of cyber security. In our experience as national cyber emergency responders, most successful attacks we encounter these days start with a malware-laden phishing email. Either they get a user to directly divulge credentials with a convincing letter, or they get them to open an attachment with an infected payload, or get them click on a link to a malicious site. From there it’s just a domino effect with grave consequences waiting at the end.”
To successfully navigate any journey, knowing the starting point is a must
“With so many threats to deal with, the first step is knowing exactly where you stand right now and what kinds of threats pose the biggest threat to your unique data environment,” says Caruso. “Our proven vulnerability assessments are designed to do just that. Obviously the security needs of a bank are far different than a restaurant, just like a hospital’s needs are different than a defense contractor and a design firm has different concerns than an online retailer. That’s why the first thing we do is get a full understanding of the client’s data landscape, from data creation, how it’s used and by whom, to how and when it’s destroyed. Are mobile devices part of the equation? Are WiFi environments, or public facing websites, or seasonal employees in the mix? Every client is different, so we don’t rely on cookie-cutter assumptions, we get the clearest and most accurate picture possible so we can offer our clients knowledgeable recommendations which will be the most useful and cost effective solutions available for their particular situation. We’ve been doing this for over twenty years, and our longevity didn’t spring from fleecing clients with fancy sounding solutions they don’t want or need, it came from developing lasting relationships by providing industry leading solutions that make a real difference.”
Trial by fire, without the burn – penetration testing
“A penetration test is about learning in its most basic sense. It’s like being told as a kid not to touch the stove because it’s hot and will burn you,” says Caruso, “but in all honesty, was it those constant reminders that embedded the lesson in your brain, or was it the first time you actually experienced what hot and burn really meant when, of course, you eventually touched the stove. For instance, you can talk about spam and phishing until you’re out of breath, but nothing has the unforgettable impact on employees like actually getting burned in a controlled attack, like the ones we’ve performed for many clients as an optional component to the social engineering phase of our comprehensive penetration testing packages. We’ll use the same publicly available information hackers can easily find and generate a realistic attack, which have so far never failed to yield a bounty of live user credentials. With proof in hand, security officers have the best ammunition possible to raise user awareness enterprise-wide, and if they need some help and/or direction raising that crucial awareness, we can help with that too. Our goal is and always has been to help our clients strengthen their cyber security posture on every front possible, and that certainly includes the weakest link of all, the human element. If we can help an organization at least get a firm handle on covering the cyber security basics, we will have helped them be able to thwart more than 95% of the threats out there, and that is an essential point to get to before ever worrying about how to close the rest of that gap. That last 5% is when we get into the territory of the most advanced and sophisticated threats, which we can of course help with too, but simple math makes it pretty obvious what the first order of business should be.”
Every client needs customized solutions in today’s cyber threat landscape
*Global Digital Forensics is a recognized industry leader in the fields of computer forensics, cyber security and emergency incident response, with years of experience assisting clients in the government, banking, healthcare, education and corporate arenas. For a free consultation with a Global Digital Forensics specialist, call 1-800-868-8189 about tailoring a cost-effective plan which will meet your unique needs, without wasting resources on solutions you simply don’t need. Emergency responders are also standing by 24/7 to handle intrusion and data breach emergencies whenever and wherever they arise. Time is critical if a cyber incident has occurred, so don’t hesitate to get help. For more information, visit our cyber security page.
The NTSB (National Transportation Safety Board) released their 2015 Most Wanted List of Transportation Safety Improvements this week, which highlights the safety-critical actions that the DOT modal administrations, the U.S. Coast Guard, and the States need to take to help prevent accidents and save lives. Topping the list was the need to do more about the growing problem of electronically distracted drivers. It’s a problem that can certainly have deadly consequences, like the case involving the arrest of a Maryland Episcopal Bishop who posted bail for $2.5 million on Thursday after being accused of killing a cyclist on December 27th while driving drunk and texting.
“It’s really coming to a point that data from mobile devices like smartphones and tablets should be collected from just about any accident scene,” says Joe Caruso, founder and head of Global Digital Forensics (GDF), a recognized national leader in computer forensics and electronic discovery (eDiscovery) services for over twenty years. “We’ve certainly seen a spike in requests from accident attorneys to collect data from mobile devices to help determine what role, if any, electronic devices had in the accidents they are investigating, especially over the last few months. While the fact that there are certainly more people than ever relying on mobile devices every day may account for the rise, I think it also has to do with states like New York, among others, beefing up their texting-while-driving laws recently, or states like Florida looking to push legislation through for tougher laws as early as this spring, that may have prompted more attorneys to leave no phone unturned. Like with insurance, it’s far better to have the data and not need it, than to need it and not have it. And to that end, we’ve made the process easy and affordable for attorneys that deal with accident litigation. For a flat rate of $1595, which is very low as far as comparable pricing across the industry, we offer a Quick Analysis for mobile devices which is designed to correctly collect all the data from a mobile device and help attorneys determine if a more thorough analysis is warranted.”
The GDF Quick Analysis process:
- 1. The suspect device is received, and logged.
- 2. A proper chain-of-custody log is created.
- 3. The suspect device is forensically duplicated (imaged) using court accepted procedures.
- 4. The original evidence is properly stored in compliance with court approved procedures.
- 5. GDF's certified analysts search the entire mobile device for all recoverable data.
- 6. All recoverable data is extracted and provided to the client in easy to understand format.
- 7. GDF's assigned lead analyst forwards the results to the client.
- 8. The results will help identify the presence of any evidence or indicators to help client determine evidentiary value and decide if a more thorough analysis is warranted.
“Compared to other computing devices like PCs and laptops, mobile devices typically have much less storage capacity, which exponentially increases the chances of valuable electronic evidence being overwritten and lost from further use,” says Caruso, “so getting the device forensically imaged as soon as possible is critical. Once we’ve done the Quick Analysis, all of the data will be preserved in the exact same state it was on the day we received it, and can then be used in multiple ways at any time afterwards. If the attorneys need to build a timeline, they’ll have the collected data available to do it. If they need to broaden their search scope after learning more about the case, we’ll be able to help with that too, using the data from the original collection. And if things get more complex, our vast experience and expertise in all things relating to digital evidence will let our specialists seamlessly transition to a more thorough analysis of any and all data if necessary, and assist with any further eDiscovery needs the client may have, all the way through production and expert witness testimony.”
The right experts are just a phone call away
*Global Digital Forensics is a recognized leader providing cutting edge solutions in the fields of computer forensics, eDiscovery, cyber security and emergency incident response. GDF is strategically positioned with resources across the country and the globe to react quickly and efficiently with a staff of highly qualified and experienced specialists. Many Fortune 500 companies have trusted GDF with their most sensitive situations. GDF has the technology, skill and experience to ensure any computer forensics tasks and/or eDiscovery needs are handled in a highly cost effective manner, while always ensuring exceptional, defensible results. To speak with a GDF evidence specialist about a plan to suit your unique needs, call 1-800-868-8189. The call and the initial consultation are free. For more information, visit our mobile device forensics page.
Shakespeare may have immortalized the sentiment, but it’s a reality many organizations face every day; being betrayed by one once trusted, is the unkindest cut of all. Morgan Stanley, a financial services corporation that has been serving companies, governments and investors from around the world since 1935, announced on Monday, January 5th, that it recently got a small taste of that particular pain. According to a report published by CNN Money on the same day, an insider at Morgan Stanley exposed the personal details of hundreds of its richest wealth management clients, including names and account numbers, by posting them online, which they claim they found and took down on December 27th, before any of the 900 clients suffered any kind of economic loss due to the event. It could have been much worse though. According to the report, logs indicated the insider had accessed records on 350,000 clients, a portfolio that last year made up assets worth more than a whopping $2 trillion. Had the perpetrator been more successful, the full magnitude of the cut would certainly have been agonizing, if not fatal.
Joe Caruso, the founder and CEO/CTO of Global Digital Forensics (GDF), a premier national provider of cyber security solutions headquartered in New York City, says, “If they have totally contained the problem and got everything pulled down before any damage was caused, they really dodged a bullet. They can be very thankful they have the resources and personnel to be able to relentlessly scour the dark corners of the Web to uncover sensitive data that got carried out of the castle by one of their own. The vast majority of businesses don’t have that luxury, but every one of them is facing the possibility of an insider going rogue every single day.”
Assessing the threats from within
“The first step to controlling the insider threat problem is knowing what you’re up against,” says Caruso. “Our cyber vulnerability assessments take into account who has access to what kinds of data internally for just that reason. Just because someone is hired by a company, doesn’t mean they should have carte blanche to everything. Access should always be restricted to only those with a direct need to access certain kinds of data. By working closely with the organization’s IT staff to get a better understanding of the data flow, how it’s used and who has and/or needs access, we can help identify trouble spots and offer ways to help solve them. We also offer electronic exit interviews which can help reveal what an employee on their way out may have accessed, downloaded or copied before leaving the company, helping to ensure that important data stays in-house instead of finding its way into the hands of a competitor or is used to cause trouble by a disgruntled ex-employee.”
The malicious insider – scene 1
“From the ever present eye-in-the-sky in Vegas casinos, to the counter at a 7-Eleven, video surveillance has become a front line tool for not only protecting organizations from outsiders doing bad things, but also serving as a formidable deterrent against insiders behaving badly as well. So why not put that double edged sword to work protecting your network as well?” says Caruso. “To that end, we’ve developed the C-All User Activity Monitor/Recorder, which records screen captures and keystrokes from any and all systems with the C-All client installed. C-All makes it easy to spot, understand and be able to prove exactly what kind of insider abuse or misuse may be occurring now, or has in the past. It also captures remote desktop sessions in full video and allows the playback of the sessions by user, or by session. Once installed, C-All begins capturing activity and archiving it on a secure server on the network with a compression scheme that doesn’t hog precious drive space and resources at all, capturing all sessions and storing them for easy playback. C-All also allows for real-time monitoring. From deciphering inexplicable declines in productivity, to arming legal staff or other company personnel with concrete, indisputable evidence of any illicit or destructive activity, our C-All User Activity Monitor/Recorder is the tool that shifts the balance of power back where it belongs, in the hands of trusted IT security staff, administrators, executives and business owners. So no more mysteries that can’t be solved or proven, and no more feeling out of control. C-All is easy to use and very customizable, so you can set triggers to alert IT security when certain files are being accessed, when certain sites are visited, or even when certain keywords are typed in, and those alerts can even be sent via email to get the right people on the problem right away. Yes, insider threats can be devastating, but there are certainly things that can be done to drastically reduce the chances of becoming the next headline-making victim of a rogue insider.”
*Global Digital Forensics is a recognized industry leader in the fields of computer forensics, cyber security and emergency incident response, with years of experience assisting clients in the government, banking, healthcare, education and corporate arenas. For a free consultation with a Global Digital Forensics specialist, call 1-800-868-8189 about tailoring a cost-effective plan which will meet your unique needs, without wasting resources on solutions you simply don’t need. Emergency responders are also standing by 24/7 to handle intrusion and data breach emergencies whenever and wherever they arise. Time is critical if a cyber incident has occurred, so don’t hesitate to get help. For more information, visit our cyber security page.
With the holidays in the rear view mirror and a New Year ready to unfold, it’s time for businesses to shake off the feasts, festivities and the sometimes over-indulgent merriment to focus on the now most pressing task at hand – creating a prosperous New Year. And in today’s digital world, cyber security has a bigger part to play than ever. According to an article published by NBC News earlier this week on December 30th, it looks like hackers are planning to build on their unparalleled 2014 successes too, with their forecast of “5 Threats to Watch in 2015” bearing that out. Joe Caruso, the founder and CEO/CTO of Global Digital Forensics (GDF), a premier national provider of cyber security solutions headquartered in New York City, has been helping businesses of all sizes and stripes face the ever evolving cyber-threat landscape for over 20 years, and to him, “January is absolutely the best time for a business to see where they were, were they are, and where they need to go to get a firm grip on the overall security of their digital assets going forward.”
Put 2014 safely to bed
“The holidays are typically the most unusual time of the year for many businesses, and hackers thrive on chaos and irregularity,” says Caruso. “Employees are talking time off for the holidays, co-workers are taking up some of the slack by doing things they are not typically tasked with, people are doing some work or checking business mail from home, and it all magnifies the potential for a successful cyber attack. Business owners and IT security staff have to take all of it into consideration, especially with mobile devices, cloud computing and remote access so common and accessible today. A personalized spear phishing mail from Aunt Mildred in the guise of a holiday greeting, whose name they gleaned from a social media post the employee made, makes sense so it gets opened, the link gets followed or the attachment gets opened, and now that employee’s home computer is compromised. With spyware now installed on their system and an attacker accessing their data, keylogging passwords they’re using for their at-home-for-the-holidays-access, and even cross-infecting their tablet or smartphone when they get synchronized, the door cracks open for access to the corporate network. So vulnerability assessments and penetration testing to start the year off will ensure the network gets thoroughly scanned so threats can be identified and eradicated quickly and effectively, giving a business a clean slate to start with, without any kind of dangerous hangover from 2014.”
Keep a good start going
“Hackers are a diverse bunch, from lone wolves, to nation-state cyber warriors and organized cybercrime rings. But one thing they all have in common is they are more than willing to let it ride on a winning horse until it quits paying off. So expect the favorites, phishing and spear phishing, RATs (Remote Access Trojans), ramsomware, watering hole attacks and other third-party compromises, to keep getting ridden hard in 2015,” warns Caruso. "But expect them to be even better and harder to spot, backed with better technology, better research, better grammar, and better graphics, not to mention better lists to hunt thanks to the unprecedented breaches of the last year which saw hundreds of millions of valid emails and credentials get compromised. So the commitment every business has to be willing to make if they want to survive and thrive on the digital frontier is a commitment to regularity. Assessments and testing are not a one-and-done propositions, they need to be performed regularly to ensure continued security. Some attackers have access to networks for years before they are discovered, but getting things professionally checked out once a quarter, or even semi-annually on the outside, will help root out intruders, identify malware, improve awareness against the newest threats and solidify an effective emergency response plan should the unthinkable happen. As threats change, businesses have to change, because when it comes to cyber security, the surest way to fail is to stand still.”
*Global Digital Forensics is a recognized industry leader in the fields of computer forensics, cyber security and emergency incident response, with years of experience assisting clients in the government, banking, healthcare, education and corporate arenas. For a free consultation with a Global Digital Forensics specialist, call 1-800-868-8189 about tailoring a cost-effective plan which will meet your unique needs, without wasting resources on solutions you simply don’t need. Emergency responders are also standing by 24/7 to handle intrusion and data breach emergencies whenever and wherever they arise. Time is critical if a cyber incident has occurred, so don’t hesitate to get help. For more information, visit our cyber security page.
Sony Pictures Hack Perfect Example of the Reach a Single Cyber Attack Can Have

A successful cyber attack can leave any organization in a very bad spot
The hack on Sony Pictures Entertainment has caused a firestorm on many fronts for many people, from embarrassing communications coming to light, to exposing other sensitive information which could handicap them in their industry going forward. The founder of Global Digital Forensics lends some expert insight into how hackers can leverage a single attack into a multi-faceted assault and some things businesses can do to minimize that risk.
The aftermath of the November 24th hack on Sony Pictures Entertainment has caused quite a stir, not only in Hollywood, but worldwide. As reported in the Los Angeles Times on December 18th, the ripples of that attack are starting a finger-pointing game which could put some high level executives’ very jobs at risk. But they are not the only ones affected, regular employees who had their email correspondences exposed could be in for some embarrassing times ahead, agents and lawyers could be in for some tough sledding now that their tactics and opinions have been dragged into the light, and even the movie stars Sony has worked with, or wanted to work with, may have second thoughts after some unflattering revelations, and that’s just the tip of the iceberg. Private thoughts by executives on the President with a racial lean surfaced, unreleased films were exposed and sexually biased pay scale questions have been raised.
“If there was ever a candidate for a case study on the many forms of devastation that can come in the aftermath of a single successful cyber attack on a business, this one would be high on the list,” says Joe Caruso, the founder and CEO/CTO of Global Digital Forensics (GDF), a premier national provider of cyber security solutions headquartered in New York City. “Just look at what has happened so far,” says Caruso, “class action suits are being discussed, activist groups of all stripes are up in arms and calling for answers - and heads, movie stars are venting their frustration in the main stream media and other social media sites, a movie premiere was cancelled, the public is in a froth, and even the government is looking into the possibility that this was a state-sponsored act of cyber terrorism and weighing potential responses. So you can bet this is going to cost Sony a ship-load of money before the dust settles for good.”
“What seems surprising from the public’s perspective is how easy Sony made it for these hackers to victimize them, but from an industry perspective, it’s really not so surprising at all. We see many of the same bad cyber security habits that have so far been exposed all the time when we are called in to do vulnerability assessments and penetration testing for new clients,” Caruso admitted. “These hackers now have terabytes of confidential information to leverage when, where and how they see fit, and the full extent of the devastation it will cause will not be able to be tallied for months, if not years. But hopefully, it will at least serve as a much needed wakeup call to other US businesses that poor cyber security habits and not having at least the fundamentals well covered can easily put an entire organization at risk on many, many fonts, and that it takes action, not just good intentions, to survive and thrive in today’s digital world.”
Once an attacker has the keys, everything is up for grabs
“The critical step for any attacker is to gain that initial access, which is most often accomplished through phishing and spear phishing emails which “con” the recipient into opening a malware laden attachment or clicking a link to a malicious site. Once an intruder has gained that initial access, they are free to move sideways through the network, and it’s all downhill from there. That’s also when bad security habits get magnified. Like in the Sony attack, once they were able to access emails, they found passwords to various accounts that were actually sent by email from one party to another. So in one shot, multiple accounts were compromised, and so on, and so on,” Caruso says. “It may seem old-school these days, but you’re probably much better off giving someone a call to talk about private things, because if you type it, anywhere, there is always a chance someone will get their hands on it eventually.”
Before, during and after an attack – Real cyber security experts can help you get through it
“With all the high profile hacks that have occurred over the last year making headlines one after another, it should be obvious to every business by now that there is no such thing as perfect protection, and if any cyber security expert tries to tell you otherwise, run away, don’t walk, because they are trying to sell you bad fiction, not truth,” warns Caruso. “The reality is that any organization can potentially be hacked, from your favorite family owned pizza parlor down the street, to the largest and most well-known companies and agencies on the planet. The real keys to surviving today’s cyber threat landscape are making the likelihood of being attacked as low as conceivably possible to start with by getting a firm handle on the basics, which will thwart over 95% of threats out there and help identify suspicious activity when it occurs, and having an effective emergency response plan in place to stop and eradicate any threat that manages to make it through as quickly as possible, which will be invaluable when it comes to minimizing the damage, protecting business integrity and customer trust, and controlling the costs of the aftermath which can otherwise spiral out of control. That’s what we help clients do every day, with over 20 years of real-world experience to back it up. So don’t wait until it’s too late, the right help is available, you just have to make the call.”
*Global Digital Forensics is a recognized industry leader in the fields of computer forensics, cyber security and emergency incident response, with years of experience assisting clients in the government, banking, healthcare, education and corporate arenas. For a free consultation with a Global Digital Forensics specialist, call 1-800-868-8189 about tailoring a cost-effective plan which will meet your unique needs, without wasting resources on solutions you simply don’t need. Emergency responders are also standing by 24/7 to handle intrusion and data breach emergencies whenever and wherever they arise. Time is critical if a cyber incident has occurred, so don’t hesitate to get help. For more information, visit our cyber security page.
It’s No Secret - This is the Trifecta Most Cyber Attackers Rely on to Hit it Big

All kinds of data can put a busniness at risk if it lands in the wrong hands
From Target to Sony Entertainment, mega-breaches have been making headlines all year. On the heels of a revealing exposé recently aired on 60 Minutes, the founder of Global Digital Forensics offers some expert industry insight and commentary about some tangible and achievable security goals that every business plugged into the cyber threat landscape that is today’s digital world should consider to help avoid becoming the next big headline story.
Last Sunday, November 30th, 60 Minutes ran a story about the banner year cyber criminals have been having and laid out some harsh statistics that should be on the radar of any business, corporation, organization or agency with a digital presence. The two that should be most troubling for any IT security personnel responsible for the security of digital assets were easily the volume of businesses that have been hit by a cyber attack, 97%, and the amount of time intruders were able to spend on average on a network before ever being detected, which came to almost two full thirds of an entire year, 229 days.
Joe Caruso, the founder and CEO/CTO of Global Digital Forensics (GDF), a premier national provider of cyber security solutions headquartered in New York City, has been helping clients do battle in the cyber trenches for over two decades and has seen it all unfold in the real world before. “We find evidence of intrusions, data theft, malware infections and every other cyber threat imaginable all the time, and it is often the case that there were not any noticeable events or signs which would have led to suspicion, they were only uncovered due to in-depth testing we performed for clients that called us for professional vulnerability assessment and/or penetration testing services. That’s why the single most important aspect of a strong cyber security posture is professional threat testing with regularity and frequency, the more often the better. Once a year should be the absolute bare minimum, but what businesses have to consider if they go that route is that they could very conceivably have an intruder stalking their network for basically a whole year, and if you think that average of 229 days seems high, consider that we’ve been called into situations where we discovered attackers had access for years until we booted them to the curb. So needless to say, testing quarterly is a much, much better bet.”
Size doesn’t matter.
“Sony Entertainment is just the latest casualty on the cyber battlefield with a high enough profile to make national news, but the truth is, devastating cyber attacks are a reality for many businesses each and every day. Most go unreported for fear of losing the trust of their customers, vendors and/or investors. And then there are those that have been breached and never knew it even happened, or worse, those that have been breached and have an intruder on their network right now, right under their noses, without even an inkling that every single digital asset and bit of data they control is at risk,” warns Caruso. “And without a doubt, in a vast majority of cases we see, attackers get their initial foothold on a network by exploiting the human element, not holes in technology.”
The not-so-secret secrets to hacker success
“It’s not like there are hush-hush industry secrets that cyber security specialists are keeping from the business community as to how cyber criminals manage to wreak so much havoc when everyone knows they are out there and constantly on the prowl. The trifecta they rely on? Trust, stealth and longevity,” says Caruso.
“Exploiting trust is the realm of social engineering, which only takes a hacker leveraging the trust of one individual, through a phishing email, by phone, on social media or any number of methods, which get them to divulge their credentials," explains Caruso. "Not only can this give a hacker keys to their own business network, but can also lead to a breach of other businesses by exploiting that trust relationship, like the Target hack that started when a heating and air conditioning vendor of theirs was breached, allowing hackers to leverage that “trust relationship” to infiltrate Target’s network to the tune of stealing 40 million customer credit card numbers.”
“Once they are in, hackers typically do everything in their power to remain undetected," Caruso says, "with the exception being hackers that want to make some kind of public statement, as may have been the case with Sony Entertainment when skulls started appearing on their screens heralding the attack. Being successful on the stealth front is also the most important ingredient to the most dangerous and potentially devastating aspect of a cyber breach, longevity. An intruder with long term access is bad news on so many fronts there is no way to list them all. It gives them unencumbered ability to steal, disrupt, damage, incapacitate and embarrass any victimized party at will at that point, all of which can dramatically affect any business’ bottom line, no matter how large or small they are.”
It's better to trust the view from the outside looking in
One other tidbit that should not go overlooked from the 60 Minutes piece is the fact that most of those mega-breaches were not discovered by inside IT personnel, they were detected by third-party cyber security specialists. Global Digital Forensics has the experience, tools and expertise to do the job for organizations of any size. From vulnerability assessments to help clients determine exactly what threats they are most vulnerable to, and in-depth testing to identify, neutralize and eradicate attacks and intruders, to a national network of emergency responders ready to respond immediately if the unthinkable happens, GDF can customize solutions and services to meet any client’s unique needs. So make the call. The call is free and so is the initial consultation – so the only way to lose is by doing nothing.
*Global Digital Forensics is a recognized industry leader in the fields of computer forensics, cyber security and emergency incident response, with years of experience assisting clients in the government, banking, healthcare, education and corporate arenas. For a free consultation with a Global Digital Forensics specialist, call 1-800-868-8189 about tailoring a cost-effective plan which will meet your unique needs, without wasting resources on solutions you simply don’t need. Emergency responders are also standing by 24/7 to handle intrusion and data breach emergencies whenever and wherever they arise. Time is critical if a cyber incident has occurred, so don’t hesitate to get help. For more information, visit our cyber security page.
Holiday Phishing Can Pose Real Threat To Business Networks

Holiday phishing attacks can be the unwanted gifts that keep on giving
The chaos surrounding the holidays can add effective cover for cybercriminals looking to do some holiday phishing, and as the lines between home and business computing continue to intertwine, this can prove costly for businesses both short and long term. The head of Global Digital Forensics offers some industry insight into how hackers can leverage the holidays to their advantage and some things businesses should consider during the holiday season for a stronger cyber security posture.
In an article published on Tuesday, November 25th, USA Today reported that an analysis performed by IBM apparently concluded that there was no significant increase in cyber attacks against small and medium sized businesses during the holiday months. But, “there may be more at play under the surface than a looking at attack numbers during these months can gauge,” says Joe Caruso, the founder and CEO/CTO of Global Digital Forensics (GDF), a premier national provider of cyber security solutions headquartered in New York City, "and businesses need to keep their vigilance focused accordingly.”
“Network compromises are typically not smash-and-grab type incidents in today’s digital world, they tend to longer term operations which see hackers maintain a prolonged presence on the network to attain their goals, which can be everything from cyber espionage and data ex-filtration campaigns to malware infections and other destructive actions,” says Caruso. “The exception to the rule would probably be the growing threat of ransomware attacks we’ve seen over the last year, where hackers encrypt large blocks of data and then hold the decryption key as ransom for payment before there is any hope of getting it back; they typically like to get in and out as fast as possible so they can get the collection phase started right away. So by extension, any successful holiday phishing or spear campaign is not likely to show up “on the books” until weeks or months down the road. It may also take some time to filter between home systems and company networks, which is one of the biggest dangers holiday phishing scams pose to both individuals and businesses alike.”
Phishing relies on gaining user trust
“What makes the holiday season so attractive to phishers and spear phishers is the irregular user behavior that is so prevalent during this time of year. Not only can a phishing email come in the guise of a communication from a retailer, bank, or parcel service, counting on all the out-of-the-ordinary purchases that are typically made this time of year to add to their air of legitimacy, which will basically tempt users to click on links or download attachments against the better judgment they normally exercise just to see what the heck it is about since they don’t remember it, but hackers can also use ploys like spoofing email headers to make it look like holiday greetings from friends, relatives and acquaintances. If a friend or relative gets compromised and their contact list is exploited, the familiarity can certainly make them a lot harder to identify as fraudulent, and the daisy-chain can really get some mileage stemming from just one successful breach this way as well. And then of course are all the charity scams that pop up this time of year, relying on good will and holiday spirit to bait the hook. One click on one email is all it takes, and from there the problem grows legs, legs that can run all the way to a business network and get hackers in the door to pose all kinds of potential long-term problems.”
Seasonal workers can also significantly raise the difficulty for IT security professionals over the holidays
“Temporary employees not up to speed on cyber security policies and procedures can also pose a significant threat,” warns Caruso, “so making sure their cyber responsibilities are covered right at the beginning is very important. They may not be part of an organization’s yearlong force, but one slip up from their ranks can easily give a business headaches long after they’re gone.”
Awareness and incident response are critical bases to keep covered
“Phishing relies on human mistakes, not technology, so the number one way to combat this particularly effective form of social engineering is to raise awareness enterprise-wide. We make social engineering a strong focal point during our vulnerability assessments and penetration testing services for this very reason. The more we can drag the problem into the light, the better chance an organization has to stop the number one entry vector for cyber criminals and significantly reduce the threat of network compromises. But by our very nature, human beings have never been perfect, so having effective emergency incident response plans in place to respond immediately if the unthinkable happens is paramount. We have a network of experienced emergency responders ready to answer the bell quickly, and we’ll have responders on call 24-7 throughout the holiday season. Time is your enemy after a cyber breach or incident, so every second counts. The faster the problem is identified and eradicated, the less costly it will be in the long run for the entire organization. So don’t hesitate, if you experience a cyber incident, pick up the phone and get proven cyber security professionals on the job right away, otherwise the chances the aftermath will be far more severe and costly rise exponentially.”
The professionals you can trust to get the job done right
*Global Digital Forensics is a recognized industry leader in the fields of computer forensics, cyber security and emergency incident response, with years of experience assisting clients in the government, banking, healthcare, education and corporate arenas. For a free consultation with a Global Digital Forensics specialist, call 1-800-868-8189 about tailoring a cost-effective plan which will meet your unique needs, without wasting resources on solutions you simply don’t need. Emergency responders are also standing by 24/7 to handle intrusion and data breach emergencies whenever and wherever they arise. Time is critical if a cyber incident has occurred, so don’t hesitate to get help. For more information, visit our cyber security page.
Nothing Builds a Timeline for Attorneys on a Case like Digital Evidence

Digital evidence can make or break a case.
Timelines built using digital evidence can be an attorney’s best friend in cases ranging from lawsuits against mega-corporations, like the one that has now been filed in Arizona over an ignition switch recall by GM, to putting a child predator behind bars. In light of Arizona now being the first state of 48 currently investigating the recall to formalize their position by filing a 3 billion dollar lawsuit against GM, the head of Global Digital Forensics talks about the hidden advantages that can be gained from a thorough computer forensics analysis and the invaluable timelines that can be derived from the process in complex cases like these.
From civil matters to criminal investigations, digital evidence can be one of the most powerful tools attorneys and the courts can rely on to get to the truth. The timelines afforded by ESI (Electronically Stored Information) can shed a brand new light and perspective on a legal matter, which can be essential when wealth, reputation, freedom and even life itself can be on the line.
Just look this story about GM’s ignition switch recall, as reported by CBS news in this article posted on November 10th, which alleges new emails have been found that put the manufacturer’s knowledge of the defect two months before notifying the federal government. Over two and a half million cars have been recalled and 32 people may have lost their lives as a direct result, according to CBS’s numbers. And on Thursday, November 20th, The New York Times reported that the attorney general of Arizona said on Wednesday that the state had filed the suit in Maricopa County Superior Court against General Motors (State of Arizona v. General Motors LLC, the Superior Court of the State of Arizona, County of Maricopa, No. CV2014-014090.), claiming that the automaker had defrauded the state’s consumers of an estimated $3 billion. Reuters also reported on the same day that Arizona became the first state to throw their hat in the litigation ring out of the 48 states currently investigating the matter and deciding on whether or not to follow suit. “You can bet the existence and validity of those emails are going to be investigated by the states and weigh heavily in their decisions, prior knowledge would be a big deal in a case like this,” says Joe Caruso, founder and head of Global Digital Forensics (GDF), a recognized national leader in computer forensics and electronic discovery (eDiscovery) services for over twenty years. “Our experience in assisting with numerous class action suits also shows that in today’s world, regardless of what many people tend to believe, emails never quite die, even the ones a user tried to delete. The trick is having the knowledge and expertise to find them and put them into counsel’s hands, and that’s where computer forensics experts like us come in.”
Based in New York, but with a national presence, Caruso and his team have had plenty of experience in helping attorneys turn the tide of litigation. “One of the most satisfying things about being a computer forensics specialist is we don’t have to stress ourselves into a moral quandary over guilt or innocence, our job revolves completely around the facts the data presents. We don’t offer legal opinions, we don’t bend the truth, we just help counsel acquire, sift through, analyze and present electronic evidence from the myriad of digital devices and systems in play every day, from PCs and laptops, to smartphones, tablets and even on-board vehicle computers. We help them build strong and coherent timelines of events, we look for and verify, or invalidate, the behavior or actions in question, and we make sure every step and action we take is documented and done in a way that evidence remains pristine and admissible in court, in case that's where the matter ends up,” says Caruso, “but that’s not to say it’s not gratifying when we get to put a smoking gun into a client’s hands, as we have done countless times as qualified experts in jurisdictions across the country, and watching the truth come to light.”
Beware: There is no hiding from the digital world
“In our experience, most people simply have no idea how many digital footprints they leave behind every day,” says Caruso. “For example, take a criminal case we assisted on that had to do with a predator and child pornography. Of course the defendant was swearing up and down that he never took any of the pictures in question, didn’t know the victims and had never been anywhere near the alleged scene of the crime on the days in question. But thanks to digital footprints, like geo-location tracking data equipped on his smartphone, and a plethora of EXIF (Exchangeable Image File Format) data the particular device he used tracked, like the make of the device, the time the images were taken and even the GPS coordinates at the time, and other metadata (data about data, like MAC times - modified, accessed and created date and time stamps) we were able to help prosecutors build a substantial timeline of events and actions that simply could not be disputed, not only on the days in question, but the days preceding and following the incidents as well. Needless to say, that was game, set, match, and it was indeed one of those times it felt good to help counsel present what actually happened and get justice served. But just like all the good things that can come from leveraging digital evidence to get to the truth, there is also another side to the coin. Computer forensics is a precise science, and there are many pitfalls which can render any evidence found completely useless. If anyone without the knowledge, experience, tools and expertise tries to “play CSI” when it comes to digital evidence, chances are it will be tainted, inadmissible and just plain useless, no matter how incriminating or exonerating it may have been if seasoned professionals were on the job. So if you are involved in any kind of litigation, don’t make a huge mistake to save a few pennies, because in the end it could very well cost you the successful resolution to your case – truth be damned.”
Experts in every sense of the word
*Global Digital Forensics is a recognized leader providing cutting edge solutions in the fields of computer forensics, eDiscovery, cyber security and emergency incident response. GDF is strategically positioned with resources across the country and the globe to react quickly and efficiently with a staff of highly qualified and experienced specialists. Many Fortune 500 companies have trusted GDF with their most sensitive situations. GDF has the technology, skill and experience to ensure any computer forensics tasks and/or eDiscovery needs are handled in a highly cost effective manner, while always ensuring exceptional, defensible results. To speak with a GDF evidence specialist about a plan to suit your unique needs, call 1-800-868-8189. The call and the initial consultation are free. For more information, visit our computer forensics page.
Cyber Espionage Room Service - DarkHotel Hackers Target High Ranking Business Executives and Agency Officials

Don't give hackers the combination to your digital treasures
Business executives and government officials are being targeted by a hacker group dubbed DarkHotel, who use hotel Wi-Fi networks to orchestrate sophisticated cyber espionage campaigns, according to a recent report. GDF’s founder discusses how advanced threats like these can bring a compromise right to the doorstep of a corporate network and the importance of regular assessments and testing to keep long-term, highly advanced threats like these at bay.
When it comes to cyber threats, it doesn’t get much scarier for IT security departments than the thought of facing a sophisticated and well-crafted APT (Advanced Persistent Threat), and the level of sophistication, planning and patience detailed in this exposé on DarkHotel published on Wired’s website on November 10th, 2014 certainly would qualify. From advanced kernel-level keyloggers rarely seen in the wild, to selective targeting for malicious payload deployment, it’s clearly not a band of amateurs at work.
Joe Caruso, founder and CEO/CTO of Global Digital Forensics (GDF), a premier national provider of cyber security solutions headquartered in New York, summed it up by saying, “It’s just another recent example of the dangers that abound on the cyber front, and any business that doesn't take the threat of cyber attack seriously is not only playing with fire, they’re doing it while being doused in gasoline. In this day and age, unfortunately, maintaining a pristine network forever safe from cyber threats, outside of completely severing it from the outside world, is a pipe dream. More realistically, every company should approach cyber security from a perspective that not only have they probably already been attacked, but that an attacker could be enjoying free reign on their network right now. Technology alone will never be able to achieve perfect perfection, especially as long as “the human element” is involved anywhere in the security chain. Even with DarkHotel, all the sophistication and planning that went into it all boils down to one thing to make it all work, a human being deciding to click their mouse just once on what an attacker wants them to, that’s it. Welcome to today’s cyber attackers’ favorite weapon, social engineering.”
Advantage: Hackers
“Just think about the playing field IT security professionals have to deal with, and why they need all the help they can get,” says Caruso. “There are mobile devices like smartphones and tablets being used more than ever before, all with seemingly endless choices of software and applications, and all providing a potential threat vector for cross-platform intrusions and attacks. There is the increasingly blurred line between business and personal computing, which make a successful attack on just one employee, even an attack suffered at home, or in a hotel, a potential intrusion threat thanks to things like shared media, reusing passwords across multiple accounts for both work and play, divulging personal information on social media sites which attackers can use to their advantage when crafting social engineering campaigns like spear phishing and other targeted attacks, and a whole host of other bad cyber habits that play right into hackers’ hands. From there the only limitation for an attacker is their imagination. And that’s what tips the scales in their favor. You can plug every technology hole known to exist, and tomorrow some attacker thinks up a new clever way to get some human being to make a bad decision and they’re off and running again. That’s where regular professional threat assessments and penetration testing come in, they are the biggest keys to keeping attackers stretching on the sideline, or at least limiting them to a quick, fairly harmless jog, rather than a potentially devastating marathon.”
“Our assessment and testing solutions are designed to cover the most important bases needed for effectively managing today’s cyber threat landscape and significantly improving the safety of any cyber environment and/or digital assets,” says Caruso. "With our perfected and proven process, we’ll not only find and eradicate any existing threat on a client’s network, we’ll also help minimize the threat of future intrusion by making sure any and all security policies and procedures are up to date and up to snuff, and perhaps most importantly, we help our clients raise social engineering awareness enterprise-wide. We’ll even go as far as crafting realistic social engineering campaigns designed to trick personnel into divulging their credentials, and to date, we’ve never failed. The deer-in-the-headlights moment when we call out the 10, 20 or even 50% of staff that fell for our social engineering tactics is a more powerful awareness raising tool than just about any you can imagine. And if we can help strengthen that human link in the chain, our client’s network will be a whole lot safer going forward. But assessment and testing are not a once and done deal, they need to be done regularly. Threats evolve, personnel changes and compromises do happen, but regularly assessing and testing any organization’s unique digital environment will keep both the danger of a successful compromise, and the potentially costly aftermath, to a bare minimum.”
Real solutions for real threats
*Global Digital Forensics is a recognized industry leader in the fields of computer forensics, cyber security and emergency incident response, with years of experience assisting clients in the government, banking, healthcare, education and corporate arenas. For a free consultation with a Global Digital Forensics specialist, call 1-800-868-8189 about tailoring a cost-effective plan which will meet your unique needs, without wasting resources on solutions you simply don’t need. Emergency responders are also standing by 24/7 to handle intrusion and data breach emergencies whenever and wherever they arise. Time is critical if a cyber incident has occurred, so don’t hesitate to get help. For more information, visit our cyber security page.
Targeted Cyber Attacks Expected to Rise in 2015

With targeted attacks, hackers can really hit their mark
According to a new industry report, targeted attacks are expected to rise in 2015. GDF’s founder talks about the importance of covering the cyber security fundamentals necessary to withstand the onslaught, which will be more important than ever for any business with a digital footprint.
TrendLabs released a report on November 5th called The Invisible Becomes Visible, in which they outline their industry predictions on what the cyber threat landscape is expected to look like in 2015. And with hackers having so much success against prominent targets over the last year, like the mega-breaches suffered by Target and Home Depot which saw over 100 million combined customer credit cards compromised in those two intrusions alone, “it’s no wonder an expected increase in targeted attacks made the list,” says Joe Caruso, founder and CEO/CTO of Global Digital Forensics (GDF), a premier national provider of cyber security solutions headquartered in New York.
The scales are tipped against businesses
“Hackers have so many things working in their favor, from anonymous currencies and “Dark Web” sites which allow them any easy way to turn stolen information into real cash, to the nightmare it is to not only find them, but to have any real success in prosecution and recovery due the global nature of the problem and the tangled mess of foreign jurisdiction,” says Caruso. “It simply makes the risk versus return quotient too enticing to resist, and it’s businesses that will end up on the hook to pay the piper in the end. But that doesn’t mean businesses have to just take it lying down, they can fight back. The key is tipping the odds back in their favor with a vigorous commitment to information security.”
Forget the law of averages, hackers learning targeted attacks pay off much better
“The NFL has nothing on hackers when it comes to being a copycat league. When something works well, more and more hackers will try to exploit it until it gets stopped, whether it’s hijacking data by encrypting it and holding on to the key until a ransom is paid (ransomware), or the monumental successes they’ve had by using RAM scrapers to pilfer credit card information right at the point of sale from right under the noses of some of the biggest retailers in the world. Then of course there are the old favorites which are still devastatingly effective, social engineering like targeted spear phishing campaigns, using a third party like a vendor to gain network access, or watering hole attacks that can help them exploit specific industries or organizations. It’s all on the table and businesses better come to grips with those realities in a hurry if they want to survive and thrive in today’s digital world,” warns Caruso.
The challenges posed by threat diversity means cyber security basics are more important than ever
“The cyber threat landscape is certainly not a static one, it evolves every single day, says Caruso. “New exploits are constantly discovered, cybercrime rings seem to be continuously popping up in countries not even on the threat radar a few years ago, and the technologies businesses use are always in flux. Just think about the proliferation of smartphones and tablets over the last couple of years as the BYOD (Bring Your Own Device) phenomenon exploded, and now the “Internet of Things” is creeping into the picture too. Just about every digital convenience businesses turn to in order to make employees more productive open new threat vectors, making life easier for attackers as well. But there are some constants in the world of cyber threats too; hackers typically like the path of least resistance, and the human element will always be the weakest link in the security chain. And that’s what makes covering the fundamentals of cyber security so important. Getting a good handle on the basics alone will help a company thwart over 95% of the threats out there, and that’s what we help new clients do every day, improve their cyber security posture from the ground up.”
Every organization’s needs, desires and digital infrastructure are unique. But having veteran cyber security experts like the experienced team at Global Digital Forensics come in to professionally tailor a testing and response plan specifically geared to the individual client, can go a long way to not only preventing the initial gateway intruders can use to wreak havoc, but also substantially lessen the aftermath should an attack or intrusion still manage to occur. There is no such thing as absolutely perfect protection, but the odds and/or aftermath can be greatly affected with the right plan in place.
Get the right help before it’s too late
*Global Digital Forensics is a recognized industry leader in the fields of computer forensics, cyber security and emergency incident response, with years of experience assisting clients in the government, banking, healthcare, education and corporate arenas. For a free consultation with a Global Digital Forensics specialist, call 1-800-868-8189 about tailoring a cost-effective plan which will meet your unique needs, without wasting resources on solutions you simply don’t need. Emergency responders are also standing by 24/7 to handle intrusion and data breach emergencies whenever and wherever they arise. Time is critical if a cyber incident has occurred, so don’t hesitate to get help. For more information, visit our cyber security page.
Third Party Hacks Can Pose Significant Threat to Businesses, Just Look at the Fortune 500

Hackers with access are bad news, no matter how you slice it
According to a recent report, employees from 221 Fortune 500 companies had credentials exposed by third party hacks, which can leave corporate digital assets highly vulnerable to costly attacks. GDF’s founder talks about how hackers can use the information gathered from a successful attack on a third party to exploit business networks, and shares some keys to significantly improving an organization’s stance against this common problem.
Almost half of the country’s most prominent companies could find themselves in a very precarious situation according to a study done by Recorded Future, as highlighted in this NBC News article published on October 29th. For a little over 9 months, Recorded Future set themselves to task to find out just how prominent the problem of exposed employee credentials really is in the corporate world, and they came up with some eye-opening numbers. They determined 221 Fortune 500 companies had employees whose credentials had been exposed, with roughly half of the financial firms, technology companies and public utilities on the list among them. Joe Caruso, founder and CEO/CTO of Global Digital Forensics (GDF), a premier national provider of cyber security solutions headquartered in New York, hopes reports like these will help draw some much needed focus to this potentially devastating problem.
“Most corporate IT security departments and personnel seem to have blinders on when it comes to hacking events that occur outside the realm of their immediate responsibility,” says Caruso, “but what happens to their employees on the outside can certainly come back to bite them if those attitudes don’t change in a hurry. Just one compromised employee who uses the same credentials for multiple sites, which is a huge problem by the way, can leave the entire business network exposed to a whole slew of potential bad guys looking to gain access to their company’s sensitive digital assets. Not only does immediate and direct access by a malicious intruder become a concern, but the ability for hackers to leverage compromised credentials and other personal information gleaned from third party sites boosts the effectiveness of their social engineering attempts, like spear phishing campaigns. Because the truth is, social engineering is all about trust, and any bit of personal information that can be used to add a personal touch to a spear phishing email exponentially increases the chances that one or more employees in an organization will open a malicious attachment which could download a RAT (Remote Access Trojan), or follow a link to a malicious site, giving the attacker exactly the access they covet that way. And let’s not forget about watering hole attacks, which is a practice commonly used by hackers to target a specific industry or company by using a legitimate and trusted third party site that has been previously compromised to push out malware directly. If cyber criminals can gain your trust with a personalized social engineering ploy, they’re starting near the finish line.”
The potential danger social engineering poses is also borne out by another report released on October 29th by the Georgia Institute of Technology, titled Emerging Cyber Threats Report 2015, where it sums up the issue well - “Humans are no longer the last line of defense against cyber attacks, but often represent an end run around security measures. Convince a user to open an attachment and dismiss a security warning, and an attacker’s job is mostly done.”
Boosting social engineering awareness, assessing vulnerabilities and testing for weaknesses company-wide can all be done together for added cost effectiveness.
“The main ingredients for success when it comes to enhancing an organization’s cyber security posture are commitment and regularity,” says Caruso. “Every company relying on the digital world in any form or fashion has to understand it’s not a choice today, it’s a necessity, and they have to be committed to making a stand and following through with it. They have to understand what they are vulnerable to, which can be very unique company to company, and they have to know what their weaknesses are. And it’s not a one shot deal, the process has to be repeated regularly to make sure the organization’s cyber security posture evolves with the cyber threat landscape. That’s why we always recommend combining our professional vulnerability assessments with our comprehensive penetration testing services, and since the human element in any security chain is typically the weakest link, we also put a strong focus on social engineering throughout. And because we have the real-world experience and an extensive, proven background covering a wide array of clients, we can typically flat-rate proposals to take the guess work out of the process. We also try our best to promote regularity by offering even further discounts when organizations sign up with us for bi-annual, or quarterly assessments and testing. The added advantage to that is we will find and eradicate any malware or intrusion that may have come into existence between cycles, and with many intrusions today often lasting months or even years, it’s much better to spot it and fix it sooner rather than later, not to mention far and away less costly to the organization in the end.”
*Global Digital Forensics is a recognized industry leader in the fields of computer forensics, cyber security and emergency incident response, with years of experience assisting clients in the government, banking, healthcare, education and corporate arenas. For a free consultation with a Global Digital Forensics specialist, call 1-800-868-8189 about tailoring a cost-effective plan which will meet your unique needs, without wasting resources on solutions you simply don’t need. Emergency responders are also standing by 24/7 to handle intrusion and data breach emergencies whenever and wherever they arise. Time is critical if a cyber incident has occurred, so don’t hesitate to get help. For more information, visit our cyber security page.
Another FBI Cyber Attack Warning for US Businesses

Distance doesn't matter in the world of cyber threats
The FBI issued a warning this week to alert US businesses about hackers suspected to be affiliated with the Chinese government targeting “high-value” digital information from both commercial and governmental organizations. GDF’s founder highlights some of the security basics essential for protecting organizational digital assets on the cyber front from a wide array of threats.
Threats everywhere
For the second time in less than a month, the FBI has issued a warning on cyber security risks facing US businesses. On September 23rd, the warning was about the insider threat posed by disgruntled or former employees. And now, according to this Reuters report, on Wednesday, October 15th, the FBI issued a flash warning for US businesses about possible cyber espionage attacks by a “group of Chinese Government affiliated cyber actors who routinely steal high-value information.”
Never surrender
“With the constant stream of headlines and warnings just about everywhere you look, It’s no wonder the task of securing cyber assets can seem do daunting, especially for small to medium sized businesses; threats seem to be coming from everywhere, inside and out,” says Joe Caruso, founder and CEO/CTO of Global Digital Forensics (GDF), a premier provider of cyber security solutions. “But the last thing an organization should do is throw their hands in the air and surrender to hopelessness, because focusing on the fundamentals of cyber security will not only stop a vast majority of common threats out their like cyber criminals and hacktivists, they also help organizations identify and respond to even the most sophisticated and advanced threats out there as well, like state sponsored actors and organized cybercrime rings. And in our experience helping clients secure digital assets since the infancy of the Internet, when clients do finally take a stand against cyber threats and give us a call, they are surprised with how far we can help them make their limited resources go towards a significantly improved cyber security posture. Anything less is playing with fire with the range of threats on today’s cyber battlefield.”
Assessing, testing and responding brings cyber security full circle
“Cyber security may not be may not be what makes your business go, but failure to pay attention to it can certainly stop it in its tracks,” says Caruso. “The good news is you don’t have to figure out everything from the wheel to rocket ships to get started, we’ve got a proven framework of solutions to get businesses on a far better and safer track, no matter where they are on the readiness scale. We start by helping them figure out where they are starting from with our comprehensive vulnerability assessments, which helps an organization understand the threat vectors they need to worry about based on their unique business needs, regulatory requirements and the entire digital infrastructure they rely on, including everything from networks to digital devices like smartphones and tablets. Then we move on to penetration testing, where we play hacker to identify actual weaknesses by using the same kinds of techniques real-world hackers are using every day with great success. We put a lot of focus on social engineering awareness during this phase as well, because it is by far the most productive tool in a hacker’s arsenal when it comes to getting that first foot in the door to successfully exploit a network. Then of course we help create an effective emergency response plan, from a policy and procedure perspective, all the way through devising an appropriate escalation matrix to save valuable time in the event of an emergency incident. Because as far as reducing the costly aftermath of a successful breach or intrusion, nothing is more important than cutting down the time it takes to identify and eradicate the threat, and start managing the longer term damage to things like public trust and confidence. In a nutshell, partnering with an experienced and trusted cyber security solution provider like GDF lets you focus on what you do best, by letting us do what we do best.”
Ready to help businesses survive and thrive in today’s digital world
*Global Digital Forensics is a recognized industry leader in the fields of computer forensics, cyber security and emergency incident response, with years of experience assisting clients in the government, banking, healthcare, education and corporate arenas. For a free consultation with a Global Digital Forensics specialist, call 1-800-868-8189 about tailoring a cost-effective plan which will meet your unique needs, without wasting resources on solutions you simply don’t need. Emergency responders are also standing by 24/7 to handle intrusion and data breach emergencies whenever and wherever they arise. Time is critical if a cyber incident has occurred, so don’t hesitate to get help. For more information, visit our cyber security page.
Cybercrime Insurance Industry Poised to Explode, But Danger Lurks

Things aren't so simple when calculating cyber risk
With mega-breaches of high profile retail and banking giants making so many headlines over the last year, interest in cybercrime insurance has intensified across the global business landscape, and the CEO of Lloyd’s of London said this week she expects that interest to surge even more. GDF’s founder discusses this burgeoning trend and offers some advice, and warnings, for businesses looking into taking the plunge.
Lloyd's getting in the game
In an interview with Guy Johnson on Bloomberg TV in London this week (October 8, 2014), Inga Beale, CEO of Lloyds of London, the world’s oldest and most famous insurance market, said she expects interest in cyber risk insurance to "grow dramatically with all the hacking incidents that have been around." But big news on the topic wasn’t just confined to the other side of the pond. Two days earlier (October 6, 2014), Reuters reported that former United States Secretary of Homeland Security, Tom Ridge, had also jumped into the fray, revealing news about a new cybercrime insurance product he is launching for US businesses with the backing of five syndicates at Lloyd’s of London. With the business industry grapevine starting to heat up with talk about cybercrime insurance, Joe Caruso, founder and CEO/CTO of Global Digital Forensics (GDF), a premier provider of cyber security solutions, took some time to talk about some of the pitfalls that may lie ahead and what businesses will want to do before even thinking about pursuing cyber risk insurance.
Big year for hackers
“It has certainly been a banner year for hackers. Just look at some of high profile targets they managed to victimize in the last year to the tune of hundreds of millions of dollars and affected customers, companies like Target, Home Depot, JPMorgan Chase, Albertsons, Supervalu, Michaels, Neiman Marcus, Dairy Queen, and the list just continues to grow. So it shouldn’t come as any surprise that US businesses are looking for more ways to insulate themselves against the tremendous losses cyber attacks can inflict,” says Caruso.
It's all about risk
“But just like any type of insurance, premiums always boil down to one thing for insurers – the risk involved. And therein lies the rub. In our experience assessing cyber threats and risk, far too many businesses really have no idea what threats they may be vulnerable to, or just how vulnerable they are, and honestly, it’s also fairly new ground for the insurance industry. So correctly calculating risk is going to be the first big hurdle that needs to be cleared. Because in the end, a cybercrime insurance policy is going to have to cover a lot of ground, from direct monetary losses which can be fairly straightforward, to the longer-term-impact things like a tarnished reputation and lost customer trust can have, all of which will be unique to each and every client. They will also have to cover things like business interruption, extortion, sabotage, IP (Intellectual Property) theft, data theft, client exposure, reporting costs and much more. So obviously it is not realistic to expect premiums to come cheap, it’s just not going to happen.”
Cyber risk insurance doesn't replace cyber security
“One thing that scares me about cyber insurance is how it will be perceived and utilized in the business world. Surveys, studies and our own experience all highlight the fact that many businesses don’t even have the security basics covered, which would stop 95% or more of the threats currently out there. And usually lack of time, money and/or expertise are cited as the primary reasons more isn’t being done internally to strengthen their own cyber security posture. Cyber security does take all those things, albeit not to the degree most businesses expect, but more importantly it takes a continuous commitment. Human nature gravitates towards ease and convenience, and if companies start thinking of cyber risk insurance as an easy and convenient replacement to bonafide and proven cyber security practices because now they’ll be 'covered' against losses, some long, dark days are coming,” Caruso warns.
Insurance premiums for the healthy or the sick are always worlds apart
“If a business is even contemplating cyber risk insurance, they better first get all their ducks in a row. Think of it just like health insurance. Someone that is healthy, keeps themselves in great shape by exercising, eating right and avoiding unhealthy habits is going to be paying far less in premiums than an overweight, largely sedentary alcoholic that smokes two packs a day, because obviously the risk chart says the latter is a much greater risk and the chances the insurer will have to make a large payout are exponentially higher. That’s where companies like ours can make a huge difference, not just in helping to drastically reduce an organization’s insurance risk profile and puting a huge dent in premiums, but also in the daily battle against cyber criminals to thwart the vast majority of attacks before they ever happen, and helping clients effectively and efficiently manage the emergency response process if the unthinkable does manage to occur, like an APT (Advanced Persistent Threat) or zero day attack. Our professional vulnerability assessments let clients know exactly where they stand in relation to today’s threat landscape, from weaknesses in policies and procedures based on their business model, operations and unique internal data landscape, to regulatory compliance issues. Then we move on to our proven penetration testing, where we take on the role of real-world black hat hackers to uncover any weaknesses that can be exploited, like susceptibility to social engineering, holes in public facing endpoints, outdated or unpatched systems and networks, internal threats, application security, mistakes in how WiFi networks are managed and how digital devices like smartphones and tablets are being controlled, managed and utilized, and a long list of other potential shortcomings. In the end, we will not only help an organization save money on cyber risk insurance premiums if they decide to go that route, but we will make them much more ready to face today’s cyber threats head on, and quite possibly eliminate the need to ever have to make a claim in the first place. Now that’s smart business.”
Proven solutions to defend against cyber threats
*Global Digital Forensics is a recognized industry leader in the fields of computer forensics, cyber security and emergency incident response, with years of experience assisting clients in the government, banking, healthcare, education and corporate arenas. For a free consultation with a Global Digital Forensics specialist, call 1-800-868-8189 about tailoring a cost-effective plan which will meet your unique needs, without wasting resources on solutions you simply don’t need. Emergency responders are also standing by 24/7 to handle intrusion and data breach emergencies whenever and wherever they arise. Time is critical if a cyber incident has occurred, so don’t hesitate to get help. For more information, visit our cyber security page.
Disgruntled Employees Can Be Insider Cyber Threats Waiting to Happen, Warns FBI

Don't let disgruntled or former employees sneak away with the keys to your network
The FBI recently issued a warning regarding the considerable threat disgruntled employees can pose to businesses by using their access privileges and knowledge of company networks to steal proprietary data and other IP (Intellectual Property), cause destruction and/or disrupt business operations. GDF’s founder discusses a two-pronged approach that can help businesses control insider threats like these.
From friend to foe
The FBI and DHS (Department of Homeland Security) have been observing an increase in cyber espionage and attacks carried out against US businesses by disgruntled and/or former employees, prompting them to issue a warning on September 23rd to elevate awareness about this potentially devastating problem. “It’s a very precarious situation for employers,” says Joe Caruso, founder and CEO/CTO of Global Digital Forensics (GDF), a premier provider of cyber security solutions. “Obviously employees need to be granted access to certain digital assets and information to perform their jobs effectively, but that’s exactly what makes it such a dangerous set of circumstances when a current or former employee breaks bad. To tackle the problem, you have to approach it from both ends. Current employees need to be monitored and controlled, and when it’s time for an employee to move on, the organization needs to know exactly what they’ve been doing prior to their departure and measures have to be taken to strip them of their golden ticket – their privileged access.”
Employers have to know who’s doing what, when, how and how often on their network to control insider threats
“If a business has to secure a physical perimeter against unwanted access, chances are some kind of surveillance system will be put in place,” says Caruso. “In today’s cyber driven world, the same holds true when it comes to an organization’s network and ESI (Electronically Stored Information). To fit that bill, we offer the C-All User Activity Monitor|Recorder, which is basically a surveillance system for your network. C-All incorporates the tools managers and security personnel need to stay on top of any or all activity taking place on the network they are charged with protecting, and best of all, it’s very easy to use.”
Easy and effective
“But don’t let its simplicity fool you, it’s an enormously powerful ally in the fight to protect digital assets and data from those already inside the gates. With C-All, you can record any user activity as a screen capture movie, which can then be played back to show exactly what a user did in indisputable video form. This goes for remote user sessions too, which is vital in today’s digital landscape. For added functionality, it also allows security staff to monitor activity in real time, as well as set triggers for virtually any activity an employer wants to keep track of, from certain keywords being typed or particular sites being visited, to particular files being accessed, among countless other options. Once a trigger is tripped, C-All will record the session, log it, and index it so it is easy to retrieve by keyword or activity when it’s needed. Triggers can even be set to notify security staff by email when they are tripped so action can be taken swiftly in real time if need be. C-All also stores everything in a highly compressed format, so storage space is typically not an issue. With C-All on the job, mysteries are solved, unknowns become non-existent, and indisputable proof of user actions is always at your fingertips. That’s the kind of power that puts insiders on notice that malicious behavior of any kind will not be tolerated, hidden or overlooked.”
Electronic exit interviews keep former employees in check
“There are all kinds of ways company data can be maliciously used by a disgruntled former employee, from exposing intellectual property secrets, stealing client and vendor information, identity and credit card theft, to flat out embezzlement, just to name a few. This prompted us to develop an effective, yet cost-efficient program to fill this important gap and give businesses the ability to see exactly what data could have been exposed and give them the information they need, all acquired in a forensically sound and defensible manner, should legal steps need to be taken,” says Caruso. “So when an employee leaves the company, voluntarily or not, we will make a forensic image of the employee’s hard drive, and if applicable, we can also do the same thing with mobile devices like smartphones and tablets. Then one of our certified forensic technicians will extract all the electronic correspondence, like email, online chats and social networking, as well as documents and other information deemed pertinent according to the concerns of the client. Then we will generate a full forensics report detailing the drive contents, the results of our searches, and a full description of our forensically sound process with all the relevant technical data. And since we are intimately familiar with the world of electronic discovery and the nuances of digital evidence and computer forensics, our clients can rest easy knowing that our findings will stand up to even the highest levels of scrutiny from the opposition or the court should things escalate into a litigation setting. We can also set up package pricing to reduce the costs even further when multiple exit interviews are needed. ”
The right solutions to do the job
Insiders and ex-insiders can wreak havoc on a business, but by utilizing GDF’s two-pronged approach, businesses can take back control. So don’t wait until it’s too late, take action now.
*Global Digital Forensics is a recognized industry leader in the fields of computer forensics, cyber security and emergency incident response, with years of experience assisting clients in the government, banking, healthcare, education and corporate arenas. For a free consultation with a Global Digital Forensics specialist, call 1-800-868-8189 about tailoring a cost-effective plan which will meet your unique needs, without wasting resources on solutions you simply don’t need. Emergency responders are also standing by 24/7 to handle intrusion and data breach emergencies whenever and wherever they arise. Time is critical if a cyber incident has occurred, so don’t hesitate to get help. For more information, visit our cyber security page.
Survey Shows Cyber Emergency Response Plans Need to be Regularly Flexed to Stay Effective

What happens when you break the glass during an emergency shouldn't be a mystery
The Ponemon Institute’s new survey shows improvement in some areas of emergency incident response, but also spotlights some big concerns that most businesses need to address for their response plans to be, and stay, effective. GDF’s founder weighs in on some of the results and talks about the importance of regular reviews and testing which are instrumental in keeping incident response measures up-to-date and potent.
Some Good News
The Ponemon Institute released the 2014 results from their second annual survey on data breach preparedness sponsored by Experian on Wednesday, and some of the trends were certainly promising. There was a 12% uptick in how many companies have data breach response plans, previously 61%, a 5% increase in how many had emergency response teams in place, a 10% rise in the number of companies that have privacy and data protection awareness programs, from 44 to 54%, and a surge in companies that are making data breach or cyber insurance policies a part of their emergency preparedness plans, increasing more than twofold, from 10% to 26%, compared to last year’s survey.
Some not so good news
Some other numbers, however, were not good news. 43% of those surveyed said they had experienced a data breach, up 10 percentage points from the 2013 survey, and of those, 60% said they suffered more than one breach in the last two years, compared to 52% in 2013, which according to Joe Caruso, founder and CEO/CTO of Global Digital Forensics (GDF), a premier provider of cyber security solutions, are probably much higher numbers in reality.
After a data breach, silence isn't golden
“Data breaches are notoriously under reported by businesses of all sizes. Integrity and public trust are valuable business assets, and if they take a hit, they know their bottom line will suffer. So many businesses make even the discussion of being breached or hacked taboo turf when it comes to anyone on the outside. If it wasn’t for the regulatory compliance rules many industries face, and the threat of severe sanctions and/or fines for failure to comply, total radio silence would be par for the course. And even with all the regulations, it’s quite common for business victims to do everything in their power to keep as many details under wraps as possible. But that’s just trouble waiting to happen, because once a breach is exposed that a business tried to sweep under the rug and out of sight, customers, associates, investors and vendors all feel betrayed, and then their bottom line will suffer exponentially, often irreparably.”
Business survival often depends on emergency response
While the survey showed more business than ever have response plans in place, it also shows that only 30% of those businesses feel their plans will be at least effective, with the same amount feeling their plans are ineffective, 17% unsure, and the rest somewhere in the middle.
“Those are troubling numbers,” says Caruso, “and according to the survey, a lot of that skepticism comes from the “set it and forget it” mentality many business employ when it comes to setting up and maintaining their plans. Only 22% could make the claim that they review and update their response plans at least once a year, which should be the bare minimum. All the rest either have no defined timeframe for reviews and updates, or have not done it even once since their plans were first devised and implemented. That’s a recipe for disaster. Threats are evolving every day, technologies changes all the time, new business needs and practices continuously emerge, and if your emergency response plan is going to be effective, all of that has to be accounted for. That’s what we help clients do, assess their vulnerabilities and test for weak links in their cyber security chain with proven state-of-the-art penetration testing, from both an insider and outsider perspective. And if a business has an emergency response plan in place, we will flex it to see how it stands up to real-world threats and isolate the shortcomings, and if they don’t, we’ll help them devise one from scratch. The biggest key is regularity, because what would have worked last year will probably not stand up to today’s threat landscape, and what works today will undoubtedly be challenged by the threat vectors that evolve over the next six months or year. Like it or not, that’s today’s cyber reality, so either businesses have to be prepared to step up and play the game right, or pack up, take their ball and go home, because they will not win in the long run if they’re not ready to take the field on any given day.”
Get emergency response experts involved before disater hits
*Global Digital Forensics is a recognized industry leader in the fields of computer forensics, cyber security and emergency incident response, with years of experience assisting clients in the government, banking, healthcare, education and corporate arenas. For a free consultation with a Global Digital Forensics specialist, call 1-800-868-8189 about tailoring a cost-effective plan which will meet your unique needs, without wasting resources on solutions you simply don’t need. Emergency responders are also standing by 24/7 to handle intrusion and data breach emergencies whenever and wherever they arise. Time is critical if a cyber incident has occurred, so don’t hesitate to get help. For more information, visit our cyber security page.
Don’t Let Data Breach Fatigue Cause Dangerous Cyber Security Complacency

Effective cyber security is a constant cycle
With retail giant Home Depot finally putting numbers to the largest compromise of customer credit card information in history this week, and yet maintaining steady sales numbers this quarter and a positive growth forecast for next year, cyber security complacency can become a real danger. GDF’s founder discusses what the ugly side of a data breach can look like to businesses that are not giants in their respective industries and the importance of constant vigilance.
Massive data breaches the new norm?
Earlier this week, Home Depot revealed that up to 56 million of their customers may have had their credit card information pilfered by hackers, surpassing the 40 million Target tallied late last year, spawning a slew of headline articles like this one published by Bloomberg on September 18th, but those weren’t the only eye opening numbers.
“Most people tend to focus on how many credit card numbers were stolen, almost like it’s a way to score a game,” says Joe Caruso, founder and CEO/CTO of Global Digital Forensics (GDF), a premier provider of cyber security solutions for businesses, “but the numbers that should really be seeing the spotlight more are the ones that put dollar signs to the costly aftermath of a successful breach.”
According to the Bloomberg article, Target estimated that as of August 2nd it had spent $146 million in expenses directly related to the massive breach they suffered during last year’s holiday season.
“Sales dipped, trust and integrity took a beating, and their bottom line was obviously heavily affected. But this time the tune is playing a bit differently, Home Depot’s numbers and projections seem to be rolling on like it was just a relatively minor blip on the radar, with their shares actually ticking up by a percentage point since the revelation about the breach first came to light at the beginning of this month. What concerns me is that both consumers and businesses may be getting numb, as in desensitized, to the crippling and costly aftermath a successful breach can have on any business,” warns Caruso.
Survival of the deepest pockets
“In March of last year, the U.S. House Small Business Subcommittee on Health and Technology conducted a study which determined that nearly 60% of all small businesses that were victims of cybercrime closed their doors within 6 months. That is the reality most businesses face still today. Weathering the storm to the tune of almost $150 million like Target has is just not in the realm of reality for small to mid-sized businesses, and it’s enough to fatally choke even some of the largest. Home Depot expects a little over $60 million in expenses related to their breach this year alone, with their insurance company flipping almost half that bill, but they are huge, so they can absorb numbers like that and keep the wheels turning. They can afford credit protection services for almost 60 million cardholders, they can afford the insurance spike sure to come, and they can still function though the black eye because they will still have throngs of loyal Do-It-Yourselfers, contractors and handymen coming through their doors. But if your business isn’t on that top rung of the ladder, the fallout of a data breach could easily prove too much to bear. That’s why becoming complacent because you see these headline-making superstores survive breaches and stay open is such a danger, it’s apples and oranges compared to the devastation a typical business can face,” says Caruso.
Staying on top of the basics is paramount when it comes to cyber survival
“While having antivirus and anti-malware solutions always up and running should be a no-brainer for everyone “plugged in” to the digital world today, there is a lot more to having the basic bases covered,” says Caruso. “You need to have regular vulnerability assessments performed to zero in on what threats are most likely to affect you. Every organization has a unique data environment and needs to know what threat vectors pose the most likely threat, and since technology and threats both continue to evolve rapidly, regularity is important. Next you need to identify the weak links in your particular security chain, so regular penetration testing goes hand in hand. We take on the role of real-world hackers and shine a light on your weakest points, whether in may be insider threats, all those new mobile devices many businesses are relying on more every day, outdated and/or unpatched software, social engineering like phishing or spear phishing campaigns, or even zero day exploits that have not been reported, documented and patched yet, we cover it all. And then there is probably the most important element, having an effective emergency incident response plan, preferably with experienced emergency responders in the loop ready to jump into action immediately at the first sign of trouble. We have strategically positioned emergency responders across the country on call 24/7 so that our response time is unrivaled in the industry, and many times we can start the process of identifying and stopping the attack remotely from one of our attack centers, But if boots on the ground are required, we’ll have them there within hours, not days. We can not only help clients beef up and modernize their emergency response plans and procedures, we can even help clients create them from scratch if none exist, and that will go a long way to alleviating many of the headaches and pitfalls organizations face when dealing with regulatory compliance issues so many industries face, from financial institutions and healthcare providers, to retailers and universities. We’ve seen it all before and have that experience, so all you need to do is make the call and let us help you get and keep all your ducks in a row.”
Customized security solutions for the uniqueness of every kind of client
Global Digital Forensics is a recognized industry leader in the fields of computer forensics, cyber security and emergency incident response, with years of experience assisting clients in the government, banking, healthcare, education and corporate arenas. For a free consultation with a Global Digital Forensics specialist, call 1-800-868-8189 about tailoring a cost-effective plan which will meet your unique needs, without wasting resources on solutions you simply don’t need. Emergency responders are also standing by 24/7 to handle intrusion and data breach emergencies whenever and wherever they arise. Time is critical if a cyber incident has occurred, so don’t hesitate to get help. For more information, visit our cyber security page.
Hacking Whales of the Retail World Can Start With Just One Little Phish

All that's needed for a major data breach is one little phish to take the bait
Make no mistake about it, retailers are at war on the cyber battlefield, and far too many are losing their battles every day, according to cyber security experts who live on the cyber front like Joe Caruso. With Home Depot recently confirming another retailer mega-breach, GDF’s founder sheds some light on how one of the most simple and common threats, phishing, can often be the culprit leading to the kinds of mega-breaches which can put the finances of tens of millions of customers at risk in one fell swoop, and why regular penetration testing with a focus on social engineering is so important in today’s digitally dominated marketplace.
Adding up to big trouble
The number of retail customers estimated to have been affected by massive retailer breaches over the last year is staggering, just look at some of the big names in this article published on September 8th in The New York Times, with Target and Home Dept alone tallying an estimated 100 million cardholders compromised. “If the current pace of these huge retailer data breaches continues to surge like it has over the last year, how long can it really be before every consumer in America finds themselves under the “credit protection” umbrella of a major retailer trying to hide a black eye because their customers’ private payment information was stolen by hackers,” says Joe Caruso, founder and CEO/CTO of Global Digital Forensics (GDF), a premier provider of cyber security solutions and 24/7 emergency incident response, “but the real stomach turner is that the attacks that have been so very successful over the last year are not even on the high end of advanced or complex, just hackers using basic techniques and malware. They only need to find a way to get one foot in the door to make it all work.”
Hackers make themselves at home
“Any time an intrusion occurs, it’s definitely not a good thing,” says Caruso. “But if you can identify the attack and stop it quickly, the long term damage to an organization is likely going to be negligible, like the annoyance of an unwanted houseguest. But when the intruder gets to set up camp right in the bedroom closet, takes control of the TV remote and the car keys, empties out the fridge, steals money from your wallet and ogles your significant other every chance they get, for months on end, the annoyance factor eventually bubbles up into a full-blown family crisis. That’s what these major data breaches are like, not a one night inconvenience, but a methodical disintegration of everything you worked so hard to achieve and maintain. And true to form, the breaches Home Depot, Target and even financial institutions like JPMorgan Chase suffered didn’t happen overnight, they lingered on for months before their “guests” were finally confronted and kicked out of the house, but the car and cash were already gone, the snapshots from the bedroom closet were already taken and a packet of ketchup was all that was left in the fridge. That’s why regular professional vulnerability assessments and penetration testing are so important, we’ll check all the closets, look under every bed, find your keys, make sure your fridge stays well stocked, and you’ll finally be able to change the channel to something enjoyable again.”
Gone phishing
“Hackers do enjoy the path of least resistance, and the weakest link in any security chain is almost always the human element. So it shouldn’t come as a surprise that the top tool in their arsenal is often social engineering,” warns Caruso, “and phishing and spear phishing emails are generally the weapons of choice, especially when they are hunting whales. National retail chains, financial institutions, the healthcare industry, they all spend enormous resources on cyber security, yet every time you look up another massive data breach is making headlines. So how do hackers keep on having such great success, seemingly at will? It’s simple, they focus on that crucial first step, getting that first foot in the door, and that’s where social engineering comes in. When we do penetration testing for clients, which is us putting on the black hat of a hacker to test an organization’s cyber security posture, we’ll run phishing and/or spear phishing campaigns just like real world hackers would. We’ll research the company online, we’ll craft an email that maximizes any publically available information to make it look legitimate, sometimes even with a signature of someone high up in the organization if we can find documents, memos or marketing materials which display it online, and we’ll even create a dummy website that looks like the real thing using links and images from their own real sites, eventually calling for the target to take action, like clicking on a link, or divulging their access credentials. We’ve done it many times, and to date we have never failed to get at least a small percentage of users in the targeted organization to take the bait. And since it only takes one set of credentials to get that initial toehold into a client’s network, which would basically give us free reign to introduce malware, exfiltrate sensitive ESI (Electronically Stored Information), or set up a stealth presence to observe everything happening and continue to escalate privileges by moving sideways across the network once inside, it becomes easy to see how even the best laid security plans are rendered moot when every single user is not fully up to speed when it comes to social engineering awareness. But they will be when we get done with our assessment and testing, we’ll have the proof in hand. Believe me, nothing has a more long lasting and powerful impact than being caught and called out, and nobody is nodding off when we present our findings and remediation suggestions. Phishing can basically turn anyone in an organization into an insider threat, even if they never meant to be, and we help clients arm their employees with the knowledge they need to avoid being caught in that position, and by extension, significantly improve their cyber security posture.”
Trusting luck is not a sound security policy, so don’t wait until it’s too late
*Global Digital Forensics is a recognized industry leader in the fields of computer forensics, cyber security and emergency incident response, with years of experience assisting clients in the government, banking, healthcare, education and corporate arenas. For a free consultation with a Global Digital Forensics specialist, call 1-800-868-8189 about tailoring a cost-effective plan which will meet your unique needs, without wasting resources on solutions you simply don’t need. Emergency responders are also standing by 24/7 to handle intrusion and data breach emergencies whenever and wherever they arise. Time is critical if a cyber incident has occurred, so don’t hesitate to get help. For more information, visit our cyber security page.
Are the Dominoes Starting to Fall After Historic Bounty of User Credentials Stolen?
Are the dominoes starting to fall?
When news surfaced last month that over 1.2 billion user credentials were stolen by an organized cybercrime group thought to be operating out of Russia, the dominoes were just starting get to lined up. The founder of Global Digital Forensics, Joe Caruso, talks about the recently reported attack on hosting provider Namecheap and why it should be considered a warning shot across the bow for any business depending on a secure network to function properly.
Harbinger?
It’s been a crazy run on the cyber front in the last couple of weeks, big name banks came forward about being hacked, a slew of celebrities had their private photos exposed for the world to see, and another huge US retailer, Home Depot, is investigating a potentially massive breach which may have exposed the credit card numbers of millions of customers. But on the edge of that cluttered radar, there was a brute force attack on hosting provider Namecheap which didn’t garner as much attention, even though it may have been the first real domino to fall in the aftermath of the biggest compromise of user credentials ever, tallying 1.2 billion plus according to a report in The New York Times last month on August 5th. “IT security departments and professionals should take notice,” says Joe Caruso, founder and CEO/CTO of Global Digital Forensics (GDF), a premier provider of cyber security solutions, ”because this is a show that could be coming soon to a network near you.”
Use a mountain of credentials and see what sticks
According to the security warning published on Namecheap’s website on September 1st, the early stage of their investigation seems to have them convinced the attack they suffered was due to hackers leveraging the massive credentials bounty previously stolen by the Russian group to launch a brute force attack. Software was used to emulate different web browsers like Chrome, Firefox and Safari, allowing attackers to issue repeated login attempts very quickly and burn through any credentials list they may have to see if they can gain access, and with billions of credentials in their arsenal, chances were good at least a few would stick.
Don’t be the next domino to fall victim to avoidable password-based breaches
“The connection to the credentials stolen by the Russian group is certainly not definitive yet,” says Caruso, “and we have not been privy to any details uncovered during their internal investigation to make our own professional determination, but whether or not it was actually the case this time, it is most certainly in the realm of possibility. That’s why businesses should take heed, because attacks like these happen every day, and with that huge collection of credentials already being sold on hacker black market sites, you can bet your bottom dollar others will try the exact same tactic against other targets going forward, tipping domino after domino. The good news is it’s not a complicated fix to avoid being the next domino if approached correctly, and we help clients with these kinds of issues every day.”
In the cyber world like the real world, bad habits can have dire consequences
“Individuals exercising weak password practices, non-existent or subpar password policies and/or enforcement, and simply not being cognizant of the huge threat these mistakes pose are unfortunately all too common occurrences,” says Caruso. “When we do our vulnerability assessments and penetration testing for clients, we uncover all these weak links and help organization’s correct them effectively. I can’t tell you how many times we see ridiculously easy passwords come in when we launch a spear phishing campaign during our penetration testing phase, which is basically us assuming the role of real-world hackers in order to identify weaknesses in the client’s cyber security posture without them suffering the dire consequences a real attack would have, because nine times out of ten, that’s what hackers are after – access. Once they have that, they can do whatever they want, from stealing IP (Intellectual Property), funds or other sensitive ESI (Electronically Stored Information), to malware infections that can grind an entire organization to a screeching halt. And with so many people in the bad habit of using the same credentials for all kinds of different sites, it’s a smoldering cinder just waiting to ignite into a firestorm. We can help clients identify these bad habits internally and correct them. Like Aristotle famously said, “We are what we repeatedly do. Excellence then, is not an act, but a habit.” We always strive to embody that idea in everything we do, and we do everything in our power to help our clients develop and maintain a habit of excellence when it comes to their cyber security. And bad password habits are certainly high on the list of things to tackle when excellence is the objective.”
Customized cyber security solutions that fit any client’s unique needs and budget
*Global Digital Forensics is a recognized industry leader in the fields of computer forensics, cyber security and emergency incident response , with years of experience assisting clients in the government, banking, healthcare, education and corporate arenas. For a free consultation with a Global Digital Forensics specialist, call 1-800-868-8189 about tailoring a cost-effective plan which will meet your unique needs, without wasting resources on solutions you simply don’t need. Emergency responders are also standing by 24/7 to handle intrusion and data breach emergencies whenever and wherever they arise. Time is critical if a cyber incident has occurred, so don’t hesitate to get help. For more information, visit our cyber security page.
US/EU Safe Harbor Notice
Global Digital Forensics (“GDF”) is a United States-based corporation which adheres to the US/EU Safe Harbor Framework for personally identifiable information (“PII”) relating to its clients and its work. This Safe Harbor Notice (the "Notice") sets forth the privacy principles followed by GDF in connection with the transfer and protection of PII received from the European Union ("EU") or Switzerland.
Mission Statement
GDF is a self-certifying company which complies with the U.S.-EU Safe Harbor Framework and the U.S.-Swiss Safe Harbor Framework (collectively the “Framework”) as set forth by the U.S. Department of Commerce. GDF conforms to the Framework regarding the collection, use, and retention of personal information from European Union member countries and Switzerland. GDF has certified that it adheres to the Safe Harbor Privacy Policy of notice, choice, onward transfer, security, data integrity, access, and enforcement. Information regarding the Framework and information regarding GDF's certification are available at http://www.export.gov/safeharbor
About the Safe Harbor Framework
Established in June 2000, the "Safe Harbor" was a joint project of the United State Department of Commerce and the European Commission. The goal of Safe Harbor was to provide a regimen for transferring personal information from the EU to companies in the Unites States. Since certain EU privacy standards are more stringent than those in the United States, companies which adhere to the Safe Harbor Framework take on additional responsibilities with respect to PII.
"PII" relates to natural persons and includes such information as: name, address, telephone number, email address, photograph, or other identifying characteristic. PII does not include encrypted, coded or otherwise “neutral” data which cannot be tied to a particular person.
Scope
PII transferred from countries in the EU or Switzerland to the United States in connection with GDF is covered by this notice. It applies to PII in any format, electronic or otherwise.
Safe Harbor Privacy Principles
The following privacy principles apply to the transfer, collection, use or disclosure of personal information from the EU by GDF.
Operations Notice:
GDF conducts its business pursuant to a contract called a Client Services Agreement (“CSA”). GDF does not specifically collect information regarding individuals pursuant to the work performed under a CSA. GDF does not share PII with any third parties and does not collect information for any purposes other than those outlined in its CSA (or an accompanying Statement of Work pursuant to a CSA). GDF’s CSA provides specific descriptions of its responses to governmental and/or judicial demands for information and GDF complies with all municipal, state and federal laws regarding its collection and use of PII.
Data Security:
GDF employs all reasonable and prudent safeguards with respect to its data, its clients’ data and any other data GDF receives in the course of business.
Access and Correction: Upon written request to GDF, GDF will provide EU individuals with reasonable access to their PII. GDF will also take reasonable steps to allow EU individuals to review their information for the purposes of correction. GDF adheres to all grants and limitations of access, as set forth in the US Department of Commerce's Safe Harbor website: http://www.export.gov/safeharbor/
Recourse:
GDF maintains internal protocols to verify its compliance. GDF’s privacy officer will address any questions or concerns and will seek to resolve any disputes. GDF has committed to further dispute resolution proceedings as necessary and proper under the Framework and as required by US/EU law.
Contact Information:
Questions or comments about this Notice should be directed to:
GDF, Inc.
2838 Long Beach Rd.
Oceanside, NY 11572
Attn: Michael P. Reynolds, JD
Big Name Bank Hacks Highlight the Importance of Regular Testing and Effective Emergency Response

Security personnel have their hands full every day
JPMorgan Chase & Co was one of the seven top-fifteen banks reported earlier this week to have recently suffered a cyber attack, which in their case allowed hackers to set up camp on their internal network for an extended stay without raising alarms, only to finally be discovered during routine security testing. Global Digital Forensics founder, Joe Caruso, discusses some of the lessons businesses should take from this perfect example of today’s realities in the world of cyber threats, and the difference regular testing and effective emergency response can make for businesses to survive a breach and its aftermath.
Hackers zero in on their white whales
When a prominent bank reveals a successful cyber attack, national headlines will quickly ensue, as happened on Wednesday, August 27th, when news began surfacing about the FBI probing into a successful attack on JPMorgan Chase & Co and at least one other bank. But when news gets out that the FBI is actually investigating attacks on seven prominent banks, everyone starts thinking about their own accounts and how they may be affected, and the buzz quickly goes viral. Bloomberg followed up on Friday with a more detailed exposé which provides the latest insight into the attacks. Joe Caruso, founder and CEO/CTO of Global Digital Forensics (GDF), a premier national provider of cyber security solutions, hopes businesses will take the lessons these attacks highlight to heart. “Many important lessons can be learned from attacks like these,” Caruso says, “from the reality of the power of APTs (Advanced Persistent Threats), to the need for regular testing to catch stealthy threats which may already be residing on your network, and the importance of having an effective emergency response in place to help identify and stop an attack when it happens and significantly diminish the costly aftermath and regulatory nightmares which tend to follow.”
There is No Such Thing as “Perfect” Cyber Security
“High profile entities, especially banks like JPMorgan, aren’t known for taking cyber security lightly, and committing a reported quarter billion dollars to the effort, I think, illustrates that fact very clearly,” said Caruso. “But it also drives home another fact; no organization, no matter how huge and powerful, is totally immune to the threat posed by hackers, regardless of how many resources are thrown at the problem. But on the other side of the coin, it also doesn’t take a fortune to significantly improve an organization’s cyber security posture to help them thwart the vast majority of the threats out there. We help clients do it every day. The key is understanding the client’s data needs, digital architecture and assets, and marrying them to a customized solution that’s actually doable, from both a financial and reality standpoint. A restaurant probably doesn’t have to worry too much about state-sponsored foreign hackers spending months or years devising a plan to break into their network, like all the fingers pointing towards Russia so far for these hacks, but they would have to worry about semi-sophisticated organized crime rings targeting them for the bounty of credit card numbers which could be had. But a bank with the size and reach to influence the global economy, they do have to be thinking about APTs 24/7 and plan everything accordingly, and that is fleshed out by our experience in dealing with clients from both ends of the spectrum. In the end though, it usually comes down to effective emergency response. That’s what usually proves to be the difference between those who survive and thrive after a successful attack, and those who don’t and won’t. That’s why we have a network of experienced responders positioned across the country and on call 24/7, and yes, even on holidays like Labor Day coming up on Monday. It allows us to have response times unrivaled in the industry, and many times we can even start the remediation process remotely. So all it takes is one call and we can get on top of it right away.”
Testing for Resident Threats Early and Often
“Another lesson which should be taken from the hack on JPMorgan is the fact that they finally spotted the attack during routine security testing of their internal systems. Which is a point I can’t stress enough,” says Caruso, “the more often you have professional testing and deep scanning done, the less time a stealthy intruder will have with your network to wreak havoc. With all their resources, policies and procedures, all devised by some of the brightest minds in the security industry, they still missed the payload when it first got planted. But that’s the unfair security paradigm we all have to face - security has millions of holes to plug, attackers only have to find one, and often it’s a zero-day attack, which is an as-of-yet-unknown exploit which can be leveraged for access. It could also have been something as simple a phishing or spear phishing email, or a USB stick someone found left on a bench somewhere and decided to plug into their work system to see what’s on it, only to deliver an attacker's malware payload and give them the access they were after all along when they left their malware laden bait on the bench in the first place. Our vulnerability assessments and penetration testing plans are designed to find those weak links, raise awareness against social engineering ploys hackers commonly rely on, and uncover any existing and/or resident threats and thoroughly eradicate them, all with an eye on the appropriate regulatory compliance issues many clients face in their industries. So whether it’s things like GLB (Graham Leach Bliley) compliance for the financial industry, to HIPPA (the Health Insurance Portability and Accountability Act) for healthcare providers, or PCI DSS (Payment Card Industry Data Security Standard) for retailers, if a client falls under any compliance regulation concerning PII (Personally Identifiable Information), we have plenty of experience helping clients navigate all the potential pitfalls and headaches."
Customized Cyber Security Solutions to Fit Any Organization
*Global Digital Forensics is a recognized industry leader in the fields of computer forensics, cyber security and emergency incident response, with years of experience assisting clients in the government, banking, healthcare, education and corporate arenas. For a free consultation with a Global Digital Forensics specialist, call 1-800-868-8189 about tailoring a cost-effective plan which will meet your unique needs, without wasting resources on solutions you simply don’t need. Emergency responders are also standing by 24/7 to handle intrusion and data breach emergencies whenever and wherever they arise. Time is critical if a cyber incident has occurred, so don’t hesitate to get help. For more information, visit our cyber security page.
This Time Prominent Hospital Group Falls Prey to Hackers Believed to be Based in China

Cyber security can't be an afterthought anymore, especially in the healthcare industry
The diplomatic tension with China over cyber attacks may have just gotten another infusion of fire to deal with after it was reported earlier this week that one of the biggest hospital groups in the US was the victim of a data breach which yielded 4.5 million records containing Personally Identifiable Information. The founder of Global Digital Forensics discusses why healthcare organizations are prime targets for hackers, and why regularly testing for vulnerabilities and advanced malware is essential for this often targeted industry.
Hackers like healthcare targets
On Monday, August 18th, The New York Times (NYT) reported on a data breach suffered by Community Health Systems, which operates over 200 hospitals nationwide, that saw the compromise of 4.5 million records containing Personally Identifiable Information (PII) like names, phone numbers and social security numbers. According to Mandiant, who was engaged to investigate the incident, the belief is the attack emanated from an advanced group of cyber attackers based in China, who they say are more well known for targeting Intellectual Property, like advanced designs and research, rather than this type of PII. Thankfully, at least actual medical data does not appear to have been compromised. “The healthcare industry is a huge target for hackers,” explains Joe Caruso, founder and CEO/CTO of Global Digital Forensics (GDF) , a premier provider of cyber security solutions, “because there is a lot of potential money and/or leverage to be had on many fronts, from the competitive edge which could be gained by stealing confidential R&D and other IP (Intellectual Property), and would certainly pique the interest of foreign state-sponsored attack groups or any other competitor looking for an edge, to very personal medical information which organized criminal groups will be more than happy to exploit to its fullest, as in full blown identity theft, or even targeted social engineering attacks which prey on victims facing some of the most desperate medical situations imaginable by concocting things as simple as spear phishing emails dangling the false hope of the perfect new “miracle” cure, for a hefty price at the end course. Our vulnerability assessments and penetration testing offerings focus strongly on social engineering, so we can help shore up that front not only for the organization itself, but we can also offer assistance which will see employees come away with better insight on what to watch out for as far as phishing and spear phishing techniques which they may run into at home too. And that can help the organization by strengthening another commonly weak threat vector, employees getting compromised at home and opening the door for attackers to breach the organizational network by unknowingly schlepping in malware or foolishly re-using compromised credentials from home at work, which we see all the time.”
Regular testing is key to combatting APT longevity
“Advanced Persistent Threats, or APTs, are well named,” says Caruso, “they are advanced, as in hard to detect and often complex; they are persistent, commonly letting attackers reside on a network to do their thing for weeks, months, or sometimes even years, and they are definitely a threat. That’s why professional testing and deep scanning at regular intervals is so important. APTs are almost never going to be uncovered by off-the-shelf signature-based antimalware or antivirus solutions, and that’s why you need an arsenal like ours that goes way beyond those basic capabilities. We can even hunt down and eradicate many as of yet undiscovered zero-day threats. We can also help coach up internal staff on system behavior and other clues to look for to spot threats early, and help them devise an effective emergency response plan and escalation matrix, or strengthen any existing emergency response policies and procedures.”
The scope of the problem is costing the healthcare industry plenty
“The NYT article also highlighted some numbers which should be pasted prominently on the wall of every IT security department in the healthcare industry. It siad last year an ESET researcher calculated that the numbers broke down to the protected health information records of 24,800 Americans being exposed every single day! And judging by the record breaches this year already, I doubt that number is shrinking this year. So when you consider healthcare organizations are going to end up paying a hefty cost for each and every compromised record, from the time and resources it’s going to take to notify everyone affected and consumer protection plans they will have to shell out for, to the stigma which can affect patient trust and organizational credibility, it becomes very clear that the cost of doing nothing will end up being far greater than the cost of letting proficient cyber security experts help substantially improve your cyber security posture against future attack attempts and eradicate any existing threats already residing on the network, as well as assist with 24/7 emergency response should the unthinkable happen. And yes, we are fully versed in the regulatory compliance issues like HIPAA (Health Insurance Portability and Accountability Act) which apply to the healthcare industry and can help make full compliance as painless as possible," Caruso said.
Customized for the uniqueness of every client
*Global Digital Forensics is a recognized industry leader in the fields of computer forensics , cyber security and emergency incident response, with years of experience assisting clients in the government, banking, healthcare, education and corporate arenas. For a free consultation with a Global Digital Forensics specialist, call 1-800-868-8189 about tailoring a cost-effective plan which will meet your unique needs, without wasting resources on solutions you simply don’t need. Emergency responders are also standing by 24/7 to handle intrusion and data breach emergencies whenever and wherever they arise. Time is critical if a cyber incident has occurred, so don’t hesitate to get help. For more information, visit our cyber security page.
Having an Effective Response Plan is Crucial After a Cyber Attack, but Survey Results Show Most Businesses Playing With Fire

With threats coming from everywhere, having an effective cyber emergency response plan is essential
The scales of time and money can seem hard to balance for many businesses when it comes to emergency cyber response plans, but the recent results from a survey conducted by the SANS Institute showing that only 9% of the businesses surveyed rate their cyber response plans as “very effective” is a real problem which could have far reaching consequences for those trusting luck to keep their sensitive ESI (Electronically Stored Information) and other digital assets safe. With time and money being listed as the primary factors keeping most of those surveyed from having effective response plans, Global Digital Forensics founder, Joe Caruso, talks about how knowing where you stand in the world of cyber threats, pinpointing security weaknesses, developing a reliable response plan, and having emergency responders waiting in the wings, can cost far less time and money than many businesses think.
A big problem
This last Tuesday, on August 12th, the SANS Institute released the results of a survey titled, Incident Response: How to Fight Back . The results don’t bode well for US businesses at all, with over 90% admitting they do not have a “very effective” emergency cyber response plan in place. 62% cited the time involved to develop one as the obstacle, and 60% cited budget constraints. "These are simply unacceptable numbers and reasons,” says Joe Caruso, founder and CEO/CTO of Global Digital Forensics (GDF) , a premier provider of cyber security solutions, “because it doesn’t have to become a sinkhole of time and resources to develop and maintain an effective cyber emergency response strategy, if you approach the problem the right way.”
Assessment, Testing, Hardening and Response Can be Handled Together
“The best way to reduce cyber security costs, without sacrificing effectiveness, is to tackle more than one front at the same time,” says Caruso. “Every worthwhile plan needs a starting point, and in the world of cyber security, the starting point has to be assessing the threats you face. Every business is unique, so relying on any type of one-size-fits-all solution is simply destined to fail. Our vulnerability assessments are designed to show you exactly where you stand. We look at the entire digital landscape, from the technology in use and the data needs of the client, to regulatory compliance issues and response policies and procedures. So we’ll not only understand the lay of the land and the entire lifecycle of data from creation to destruction, we’ll also be able to show a client where their resources can most effectively be used, without saddling them with unnecessary bells and whistles which will have no real bearing on their cyber security posture. Once we finish the assessment phase, we move on to the penetration testing phase, assuming the role of a real-world attacker to see if we can break through their security. We’ll do everything from launching realistic spear phishing campaigns, the number one gateway for attackers, to making phone calls posing as support to gather network credentials, which is also a common tactic, as well as attempt to exploit other vectors, like operating system and software applications which have not been updated with the latest security patches. And after we’ve gone through the assessment and testing phases, we’ll know the client’s data environment intimately, allowing us to help our client devise an effective response plan from scratch in none exists, or strengthen any existing response policies and procedures based on what we’ve found.”
The Help Needed to Get Back Up After Getting Knocked Down
“The harsh reality is, anyone can become a victim of cyber attackers,” warns Caruso, “from corporate giants like Target, to the watchers themselves like the NSA. The paradigm of cyber security has always favored the attackers because the security side has millions of holes to keep plugged every day, but hackers only need to find one, and it can be new one that’s not even on the radar yet. So it’s not a matter of if, it’s a matter of when, and an organization’s survival will depend on how quickly and effectively they respond. Yet, the survey results showed that over 60% of the organizations that participated don’t have a reliable emergency incident response plan in place because of either the lack of time, and/or budget constraints. But the truth is, it doesn’t have to be such a costly or time consuming nightmare, and we’ve proven it time and time again. We even offer no-retainer SLAs (Service Level Agreements) to our assessment and testing clients so they can not only have experienced professional responders on call 24/7 who are already familiar with their digital landscape, but thanks to our network of responders strategically positioned across the country, we can have boots on the ground in hours if necessary, not days, to assist with the response. But many times we can even start the process of identifying, stopping and remediating the attack instantly with remote capabilities. And the best part is, if there is no attack, having us in the wings ready to go won’t cost the client one red cent. Regular vulnerability assessments and testing are not luxuries, they are necessities in today’s digital world, and we can not only cover those bases for clients, but we can help them develop a customized professional response plan and escalation matrix while we’re at it, all based on the insight we will have already gained through the assessment and testing process. So forget the time and money excuses, the right assistance to help you survive a cyber attack is only a phone call away.”
Customized Cyber Security Solutions Save Time, Money and Aggravation
*Global Digital Forensics is a recognized industry leader in the fields of computer forensics , cyber security and emergency incident response, with years of experience assisting clients in the government, banking, healthcare, education and corporate arenas. For a free consultation with a Global Digital Forensics specialist, call 1-800-868-8189 about tailoring a cost-effective plan which will meet your unique needs, without wasting resources on solutions you simply don’t need. Emergency responders are also standing by 24/7 to handle intrusion and data breach emergencies whenever and wherever they arise. Time is critical if a cyber incident has occurred, so don’t hesitate to get help. For more information, visit our emergency response page.
With Russian Hackers Stealing over a Billion Credentials, Business Password Policies in the Spotlight

Don't let one stolen password give a hacker the keys to everything
With recent reports about Russian hackers assembling the largest recorded cache of stolen user credentials in history, the vulnerabilities businesses could be exposed to warrant a close look at organizational password policies. Joe Caruso, founder of Global Digital Forensics, talks about the ramifications incidents like these can have on businesses, and how professional vulnerability assessments can sniff out weaknesses in password policies, procedures, compliance and more.
Massive Haul
On Tuesday, August 5th, The New York Times ran a story about Russian Hackers who managed to pilfer and collect over 1.2 billion user credentials, user names and passwords. To help put some heft to the gravity of numbers like these, consider this; the United Nations released results of a study in May of this year which arrived at the conclusion that by the end of 2014, three billion people around the world will be connected to the Internet, leaving a full 60%, or roughly 4.2 billion, still on the outside looking in. So if every stolen credential could be assigned to a unique individual, over 1 in 3 people connected to the Internet would have their credentials in this group’s hands, who can sell, use for identity theft, or leverage them in any other way they see fit. And according to Joe Caruso, founder and CEO/CTO of Global Digital Forensics (GDF) , a premier provider of cyber security solutions and incident response, “Businesses really need to take the hint when they see a story like this and wonder just how safe their networks are. Bad password habits are a killer when it comes to security, but you’d be shocked to know how many organization’s we’ve seen after incidents which could be traced to completely unacceptable, or totally non-existent password policies, procedures and enforcement.”
Science will eventually solve human laziness when it comes to the password dilemma, but in the meantime…
“One of the biggest problems is just the sheer volume of passwords most people have to keep tabs on for an ever-increasing number of accounts. So human nature steps in and deals with the problem by having that little voice inside convince us that it’s OK to use the same password on different sites,” Caruso says, “Less to remember, right? Then the little voice rationalizes it; no one knows my password, I’ve never had my credentials stolen, so what’s the harm? Well, the harm is by doing that you are not only putting your own identity and accounts at risk, but in many cases you’re also putting your employer and the entire business network at risk – in other words, your livelihood. If hackers manage to steal your credentials from one site, even if it’s through no fault of your own, like an inferior security posture and vulnerabilities on their end, it doesn’t take a lot to automate the process of using your matched credentials to test all kinds of sites, from your Facebook page or email account, to PayPal, eBay or even your bank, and yes, your business network too. Science will eventually solve this problem, but what the solution will look like is still anyone’s guess. Some kind of biometrics is a good bet, and they already have a lot of things on the table on that front, common ideas like fingerprinting, like on the new iPhones, or retinal scans, to the more unique and outlandish, like your heart rhythm or hand dimensions, or even way-out-there ideas like your very own flavor of body odor serving as the key to your data. But for now, passwords are still something you have to somehow remember and enter with your keyboard, and armed with the secret characters, anyone can do it for you, or as you.”
With professional vulnerability assessments, password vulnerabilities can be exposed and solved
“The way to expose vulnerabilities in any environment is to test for them,” Caruso says, “and password problems are no different. When we do our vulnerability assessment and penetration testing (pen-testing) for clients, we usually launch a full blown spear phishing campaign to see who we can dupe into giving us their credentials, and we’ve never failed to get users on the hook in any organization we’ve ever tested. And when the responses start rolling in, we get to see the passwords people are using, and let me tell you, it can be frightening to see. The really dumb stuff like “qwerty,” “abc123,” and “god” protecting access to sensitive business data or digital assets still pop up so often it makes you really wonder what some folks could possibly be thinking. It’s so ridiculous it can sometimes border on amusing. Then there is the usually another crew that like to use names and dates of loved ones and events, many of which could be easily figured out just by visiting their Facebook page, which hackers love to roam for that kind of information. But when we bring it up during the reporting stage and call out the offenders, no one is laughing. And once we’re armed with the evidence, we go to work, hand in hand with the client, to create, fix or strengthen their policies, procedures, and enforcement concerning passwords, while also identifying any other weak links anywhere along the cyber security chain. There are many ways to approach solving the problem, but armed with our testing results and an in-depth knowledge of the client’s digital landscape, data flow, business requirements and regulatory compliance issues after the assessment and testing process, we can help them tailor a plan which will fit just right.”
Custom solutions for today's cyber threats
*Global Digital Forensics is a recognized industry leader in the fields of computer forensics , cyber security and emergency incident response , with years of experience assisting clients in the government, banking, healthcare, education and corporate arenas. For a free consultation with a Global Digital Forensics specialist, call 1-800-868-8189 about tailoring a cost-effective plan which will meet your unique needs, without wasting resources on solutions you simply don’t need. Emergency responders are also standing by 24/7 to handle intrusion and data breach emergencies whenever and wherever they arise. Time is critical if a cyber incident has occurred, so don’t hesitate to get help. For more information, visit our cyber security page.
Black Hat USA 2014 Will Again Stress Need for Security Basics with Glimpse of What May Lie Ahead

Having the basics well covered will help you navigate through anything that comes along
Black Hat has become the go-to convention where black hats and white hats collide, with hackers showing off their ingenuity and prowess by openly defeating popular security measures, and security professionals demonstrating all of their latest tools and methods in their never-ending battle to keep up. The founder of Global Digital Forensics discusses how covering cybersecurity basics and getting the right emergency incident response plans in place can keep organizations on point for whatever threats may lie ahead.
Black Hat 2014 offering some FUD
When the Black Hat conventioneers descend on Las Vegas every year, starting today August 2nd this year, one thing can be always counted on, plenty of FUD will be on the menu - also known as fear, uncertainty and doubt. The run-up has already made its share of FUD inducing headlines, like in an article published by Reuters on July 31st about how hackers could use a USB device like a computer mouse or keyboard to successfully infect a system with malware, completely undetected, by leveraging the unfiltered way operating systems read and process the firmware on the device once it’s plugged in. “And that is scary stuff,” Joe Caruso, founder and CEO/CTO of Global Digital Forensics (GDF) , a premier cyber security solutions provider, said. “But the way the cyber threat landscape is today, I would much rather see businesses use their resources, often very limited resources, in covering the basics like raising social engineering awareness for every employee across the board, having regular vulnerability assessments, penetration tests and deep scans performed, and putting together an effective emergency incident response plan, before directing any real concern or resources towards much more remote possibilities like these.”
New attack methods making headlines doesn’t necessarily mean they’re new, or likely
“It’s not like it’s a new concept. It was widely reported that late last year at the G20 Summit in Russia there was a little something extra in the gift bags handed out to the high ranking political officials in attendance, USB sticks and phone chargers, emblazoned with the summit logo, with spyware pre-loaded which would deploy their payload once the stick or charger was plugged into a system or device, like an tablet or smartphone," recalls Caruso. “But stunts like that take a decent amount of coordination and trust to pull off, but a well-crafted phishing or spear phishing campaign can cause exactly the same problems, are a lot easier to execute, and have a lot less overhead for the attackers, making it a cheap and easy attack to launch, making them a hacker’s dream on the risk-cost-and-reward scale. When you look at the biggest and most successful headline-making attacks, well over 90% of them started with a single employee dropping the ball by falling for a phishing or spear phishing email. So yes, that’s where the focus should be for every business with valuable ESI (Electronically Stored Information) and/or digital assets to protect. Covering the basics first and sweating the highly remote possibilities last; that’s how we structure and perform our professional vulnerability assessments and pen-testing (penetration testing), with a strong focus on social engineering. When we we’ve taken care of a client, they are in a much stronger position as far as their overall defensive cyber security posture is concerned, because we will have we’ve identified their weaknesses, from the technology to the human element, and we’ve eradicated any nasty hard-to-detect malware existing on the system or network. But there is one also one more piece to the puzzle which may be the most important of all, emergency incident response.”
When, not if, an attack occurs, an effective emergency response plan is crucial
“If any cyber security professional tells you there is such a thing as perfect cyber security protection, aside from dropping everything electronic and going back to paper and filing cabinets, don’t walk away, run!,” warns Caruso. “Cyber threats are evolving every day, threats no one ever saw coming will pop up, or someone will slip up and leave an opening an attacker is just waiting for. The difference between survival and total demise will all come down to how an organization responds. One of our biggest strengths in the security industry are our 24/7 emergency incident response teams, strategically positioned across the country and the globe to ensure we can have boots on the ground within hours, not days, to almost any metropolitan area. But most of the time we work even faster than that, with remote response options, in many cases, which allow us to be instantly on the job. Anyone can call us in an emergency, but clients that use us for our vulnerability assessments and pen-testing have some big advantages; we’ll already know the lay of the land relating to their requirements, regulatory compliance issues, data flow and digital architecture, and we will have already helped them devise and/or improve their emergency response policies and procedures so they have an easy-to-follow roadmap and escalation matrix ready to be executed at the first sniff of trouble. Our clients can also have us waiting in the wings with the “no-retainer” response services we offer our pen-testing clients. If something happens, we’re a phone call away and can jump right in knowing exactly what’s what so we can respond as efficiently and cost-effectively as possible, and if nothing happens, having us on call won’t cost them a thing. And that’s as close as you can get to a no-lose scenario in today’s digital world. Black Hat 2014 undoubtedly will offer a lot of FUD again this year, but we’re here to get you through whatever you actually encounter in the real world.”
To thrive in this digital world, only trust proven cyber security experts
*Global Digital Forensics is a recognized industry leader in the fields of computer forensics , cyber security and emergency incident response , with years of experience assisting clients in the government, banking, healthcare, education and corporate arenas. For a free consultation with a Global Digital Forensics specialist, call 1-800-868-8189 about tailoring a cost-effective plan which will meet your unique needs, without wasting resources on solutions you simply don’t need. Emergency responders are also standing by 24/7 to handle intrusion and data breach emergencies whenever and wherever they arise. Time is critical if a cyber incident has occurred, so don’t hesitate to get help. For more information, visit our cyber security page.
From Cyber Security to eDiscovery, the Cloud Can Complicate Matters

The cloud can be an unfriendly place
Cloud computing has found its way into nearly every sector of industry, and with the challenges the very nature of “computing in the cloud” brings to the table for both IT security personnel and legal professionals, NIST released a draft report for public review and comment to drag some of those challenges into the light. The founder of Global Digital Forensics offers some industry insight into this burgeoning world of cloud computing and talks about some of the difficulties which businesses and counsel must consider before diving in head first.
Clouds everywhere
Over the last couple of years, cloud computing has exploded. And with it, so too have the frustration and confusion levels of those responsible for the security of organizational ESI (Electronically Stored Information) and digital assets, as well as those tasked with navigating the intricacies of eDiscovery (Electronic Discovery) involved in litigation. On June 23rd, the Information Technology Lab at NIST (the National Institute of Standards and Technology), which is tasked with promoting the U.S. economy and public welfare by providing technical leadership for the Nation’s measurement and standards infrastructure, released a report draft titled “NIST Cloud Computing Forensic Science Challenges” for a public review and comment period which is to close on July 21st. In it, they grapple with the problems cloud computing poses for cyber security specialists and litigation professionals alike. Joe Caruso, founder and CEO/CTO of Global Digital Forensics (GDF) , a premier provider of cyber security and eDiscovery solutions, has been a front-liner on both battlefields for over two decades, and has seen firsthand the complications which can arise when “the cloud” is involved. “It’s a whole new ballgame when the cloud is involved,” he says, “the diversity of providers and plans, the geographic distances and multiple jurisdictions which can be involved, and the variety of applications, equipment and tools involved can be a nightmarish prospect for those who don’t live and work on the cutting edge of the cyber security and forensics industries.”
All clouds are not created equal
“Probably the biggest source of headaches is the wide variety of cloud options available,” says Caruso. “From the equipment used, to the architecture and function of the environments and applications, there are a lot of things which must be carefully studied and considered before developing a sound cyber security plan, or before an effective forensic readiness plan can be established. Even in the most complex internal server environments there are some certainties which make life on both fronts a lot easier than in the cloud, like the physical location of the data, the jurisdiction and regulatory concerns which have to be dealt with and the control the organization typically has over it all. In the cloud, it’s just not that straight forward. You may not only have multiple sets of vendor policies and agreements to contend with, but the data may reside or travel through completely different countries, introducing some sometimes very thorny jurisdiction issues which can not only make it problematic to work within restrictive court imposed deadlines concerning eDiscovery and the potential to prosecute or defend, but sometimes even makes it impossible to gain access to the logs and other information vital to a case. The same goes for the cyber security aspect, because when data is out of your hands, it’s also out of your control, which is the first tenet of effective cyber security. Another big problem can also be the proximity and comingling of information with other cloud subscribers, which can make the identification, acquisition and production of digital evidence feel more like an art form than a science in a great many cases.”
A fish out of water shouldn’t be driving
“If there is one thing the NIST report makes abundantly clear, it’s that when dealing with a cloud environment, there is no perfect roadmap to deal with cyber security and eDiscovery issues. With all the variables involved, nine times out of ten it takes the ability to adjust effectively on-the-fly. Otherwise, it’s like thinking you can just get up and scale Everest one morning because you read an article on how it’s done. But in truth, it will take a whole lot of experience in dealing with environments like that, knowing everything about your equipment inside and out and how to adjust if anything goes wrong with any of it, and following the guidance and instructions of the sherpas who’ve made the ascent many times before. Think of us like the sherpas, our team of specialists will study the clouds, gauge the snow and help you pick the best tools equipment and path to successfully make it to the top of the mountain. Because if you leave that role in the hands of an internal department or outside vendor not skilled or experienced enough to handle the nuances of the cloud, you’ll just end up another frozen body buried in the snow on the path to the summit.”
Experts with ESI, from security to eDiscovery
*Global Digital Forensics is a recognized leader providing cutting edge solutions in the fields of computer forensics, eDiscovery, cyber security and emergency incident response . GDF is strategically positioned with resources across the country and the globe to react quickly and efficiently with a staff of highly qualified and experienced specialists. Many Fortune 500 companies have trusted GDF with their most sensitive situations. GDF has the technology, skill and experience to ensure any computer forensics tasks and/or eDiscovery needs are handled in a highly cost effective manner, while always ensuring exceptional, defensible results. To speak with a GDF evidence specialist about a plan to suit your unique needs, call 1-800-868-8189. The call and the initial consultation are free. For more information, visit our eDiscovery, cyber security and digital forensics pages.
Mobile Device Forensics Guidelines Play Key Role in Supreme Court’s Smartphone Evidence Warrant Decision
Law and technology are joined at the hip today, but learning to walk that way is not always easy
With smartphones playing an ever increasing part in the lifestyles of so many people in today’s technology driven world, the amount of private information they can contain can be staggering, from the uninteresting and mundane, to the potentially embarrassing or even incriminating. On the heels of the Supreme Court decision to require a warrant before law enforcement can search an individual’s smartphone, Joe Caruso, founder and CEO/CTO of Global Digital Forensics, discusses some types of information smartphones can contain and why it is so important for attorneys to know how to navigate the world of digital devices, or bring in someone who does.
SCOTUS Reaches Desicion on Warrants for Smartphones
"As reported in this July 1st article by NIST (the National Institute of Standards and Technology), the June 25th, 2014 Supreme Court ruling in Riley v California shook up the electronic discovery world. It was also met with both cheers and jeers when the verdict was finally in, depending on whether it was seen from an individual privacy perspective, or a law enforcement perspective, respectively. But this much is fact, there is now precedent which will require law enforcement officials to obtain a warrant before being allowed to sift through information on someone’s smartphone, which up until now has been fair game when an arrest took place. “It was a long time coming,” said Joe Caruso, founder and CEO/CTO of Global Digital Forensics (GDF) , “digital devices like smartphones today can have computing power which rivals what military supercomputers had under the hood just 15-20 years ago. Couple that with storage capacity that could fill the beds of several pickup trucks with documents if printed out, and the apps and Internet capability that so many people rely on every day to do everything from work and looking things up, to taking and sharing pictures, video and private correspondence, and it was only a matter of time before the privacy concerns posed by smartphones and other digital devices and an individual’s Fourth Amendment rights were going to face off.”
History and technology butt heads
Existing precedent is obviously rooted in the past, but it’s not always easy drawing dots and the connecting lines between historical precedent and today’s technologies. Michael P. Reynolds, JD, an attorney who specializes in the technology field and has served as consulting counsel for Global Digital Forensics on many occasions, recently published an opinion titled, Warrantless Searches of Smartphones Limited: Historical Principles Applied in the Digital Age , in which he calls the Supreme Court’s decision a “watershed moment,” and tries to help connect some of the dots that have now been added to the board. He also sums up the crux of the SCOTUS decision in his closing by warning, “Crafting a reasoned and methodical approach to discovery with the assistance of legal and computer professionals is the key to staying on the right side of any discovery trend, from the Supreme Court of the United States, to a Night Court near you.”
Keeping an eye on the ball
“The ediscovery process always continues to evolve because of the speed with which technology roars forward, but that doesn’t mean attorneys, or the courts for that matter, are always seeing things from a cutting edge perspective,” Caruso said. “ It’s not easy staying current on every technology, or the latest digital forensics tools and processes, especially when that’s not even your main field of expertise. But it is our field of expertise, so we do. And that’s why the courts don’t tend to take excuses from litigants, and especially from their counsel, when it comes to eDiscovery. There is expert help out there, and if an attorney isn’t well versed enough in the ins-and-outs of every bit of technology involved and how to correctly identify, acquire, analyze and produce every bit of relevant data necessary and/or requested for the case, they are compelled to get expert outside help like we provide. And if they don’t, their future will not be filled with good things once the judge gets through with them.”
Smartphones and other digital devices can hold a wealth of evidence
“Let’s forget for a second all the information people purposely store on their smartphones and digital devices, phone numbers, pictures, favorite websites, texts, emails, contact addresses and so on. While that kind of information could prove invaluable during litigation to prove or disprove a case, often it’s the information the user doesn’t know the device stored that proves to be the smoking gun. We’ve been called in as digital forensics and technology experts on countless civil and criminal cases across the country, and we’ve delivered more than our fair share of digital smoking guns that counsel on the case was not even aware existed until we fished it out,” said Caruso. “For example, we assisted in a child pornography case where we not only found the incriminating photos which the suspect tried to delete and destroy, but we also acquired metadata (data about data) on the photos which that particular device stored with geo-location tracking information. So not only could the attorney produce the photos the suspect was convinced he had thoroughly destroyed, but he could also build a timeline of when the photos were taken, and map the locations they were taken in down to the building. After that, the rest was a cakewalk. Digital forensics and eDiscovery often make or break cases today, and that’s why the unanimous opinion written by Chief Justice John Roberts cited NIST’s Guidelines on Mobile Forensics three times, and it’s also why getting a digital forensics expert involved early in the process is more important today than ever before.”
Don’t delay in getting expert help when evidence goes digital
*Global Digital Forensics is a recognized leader providing cutting edge solutions in the fields of computer forensics, eDiscovery, cyber security and emergency incident response. GDF is strategically positioned with resources across the country and the globe to react quickly and efficiently with a staff of highly qualified and experienced specialists. Many Fortune 500 companies have trusted GDF with their most sensitive situations. GDF has the technology, skill and experience to ensure any computer forensics tasks and/or eDiscovery needs are handled in a highly cost effective manner, while always ensuring exceptional, defensible results. To speak with a GDF evidence specialist about a plan to suit your unique needs, call 1-800-868-8189. The call and the initial consultation are free. For more information, visit our eDiscovery page.
Financial Trojan EMOTET Uses Network Sniffing to Multiply its Misery

Hackers with access are bad news, no matter how you slice it
With just one member of an organization falling for the phishing scam that delivers the EMOTET Trojan, everyone and everything on the network they are connected to can be put at risk. Global Digital Forensics’ founder discusses what organizations can do to raise social engineering awareness to protect against these type of malware infiltrations, while at the same time helping to secure other critical aspects of their cyber security posture.
EMOTET Banking Trojan Sniffs Out Prey
Earlier this week, reports started surfacing about a new banking Trojan dubbed EMOTET making the rounds, like this June 30th report in Security Week . But unlike run-of-the-mill banking Trojans that employ keyloggers, screen captures, dummy website phishing portals and other means to capture sensitive banking information, EMOTET goes even further by leveraging network “sniffing” to propagate to other systems and devices connected to the same network as the compromised user. It also cleverly uses DLL files to store the information that is to be sent back to the attackers and to help cover its tracks so the user is oblivious to its presence.
“This allows for an attacker to monitor and capture digital information, even if it’s being sent through a normally secure connection,“ said Joe Caruso, CEO/CTO and founder of Global Digital Forensics (GDF), a premier provider of cyber security solutions, “putting financial data at great risk.”
I Spy … Everything
“As information travels across the network, it’s possible to "grab" that information,” explains Caruso, “so when hackers employ network sniffing in their malware design, it basically gives them the ability to “sniff out” the information and data moving across the network, even using normally secure HTTPS protocol, which could include information on other devices on the network, passwords, usernames, sites visited and virtually anything else users on the network are doing. It’s like a Hollywood heist movie where the bad guys splice into the security system and can see everything all the internal security cameras see without the guards having a clue. With the way they designed EMOTET to use DLL files, or overlay files, which no typical user ever pays attention to, it lets them not only store information like Web addresses of financial sites they are looking for a match to in order to trigger certain aspects of the payload, but also lets them evade detection so they can sit on the line undisturbed and undetected until the information they are after comes along. Then it’s just a matter of getting the detected information captured and sent back to the command and control module, which can be done in any one of a number of ways.”
Don’t be fooled by geography
According to the report, right now the European theater is being mostly affected, with Germany seeing the most action; even the phishing emails used are predominantly in German. “But don’t let geography or language lull you into a false sense of security,” Caruso warned, “think of it like a deadly virus outbreak. What may have started with a handful of infected individuals in a small village in China or Africa can make its way across oceans in a matter of hours by plane with just one infected passenger and start spreading like wildfire wherever they land. With the Internet, travel time isn’t counted in hours; it’s counted in fractions of a second, and the landing strip is right in your home or office. When hackers have success like they’ve been having with EMOTET, you can bet they will find a way to tweak their phishing scheme and payload to maximize success in other countries as well. So don’t discount the threat it poses right here at home just because it seems to have made its debut overseas.”
Social Engineering is a hacker’s favorite tool
“Our GDF emergency response teams are on call 24/7, and have been called in to handle countless cyber emergencies for organizations of all sizes. And if one thing bears repeating as often as possible, it’s that most successful advanced attacks start with a simple phishing email,” says Caruso. “You can have all the firewalls, virus scanners and other technology you want in place to thwart cyber attacks, and they do a great job in a great many cases to stop simple attacks, but the ones that make headlines and cause great turmoil for even some of the largest and most recognized companies on the planet can most often be traced back to a simple phishing or spear phishing email, which lets an attacker get a foothold on the network. The reasoning behind it is simple; if a hacker can muster enough trust in a well-crafted email by personalizing it enough to make sense to the target, human nature takes over and it gets opened, bypassing all the security measures in place to stop brute force attacks and such. Even simple curiosity can be costly, and it won’t bode any better for the organization than it did for the cat. We’ll take on the role of real-world hackers to shine a spotlight on a client’s weaknesses and raise awareness enterprise wide. We’ll even gather publicly available information that any hacker would have access to and launch a realistic phishing or spear phishing campaign, complete with a legitimate looking dummy website to entice users to divulge their credentials to us. When the smoke clears, we always have the user credentials hackers covet, and the lesson really sticks when we catch folks red-handed. In today’s digital age, it’s an invaluable lesson to learn in a way that doesn’t have all the grave consequences a real attack would.”
Test, identify and respond
“Regular vulnerability assessments and penetration testing are paramount for organizations to survive today’s cyber threat landscape,” Caruso cautions. “By letting cyber security specialists like ours at GDF review, test and identify an organization’s weaknesses on the cyber front, we can put together a remediation plan that will help any client significantly strengthen their cyber security posture. And since we’ve been at this for such a long time, our experience translates into streamlined, cost-effective solutions that not only fit our clients’ unique needs like a glove, but we also get the job done in the most efficient and cost-effective manner possible by not including solutions that simply aren’t needed for their situation. We take the time to understand the entire digital landscape and the data lifecycle of our clients’ ESI (Electronically Stored Information) and other digital assets, and that lets us offer plans and assistance which make a real difference, and not just “techie” sounding offerings, which serve no other real purpose other than inflating their bill unnecessarily.”
Cyber security solutions tailored to fit
*Global Digital Forensics is a recognized industry leader in the fields of computer forensics, cyber security and emergency incident response, with years of experience assisting clients in the government, banking, healthcare, education and corporate arenas. For a free consultation with a Global Digital Forensics specialist, call 1-800-868-8189 about tailoring a cost-effective plan which will meet your unique needs, without wasting resources on solutions you simply don’t need. Emergency responders are also standing by 24/7 to handle intrusion and data breach emergencies whenever and wherever they arise. Time is critical if a cyber incident has occurred, so don’t hesitate to get help. For more information, visit our cyber security page.
Hackers Target Critical Infrastructure SCADA Systems with Havex Trojan

Know the threats you are facing in the cyber world
The Department of Homeland Security issued an alert regarding a remote access Trojan called Havex that is being used to target Industrial Control Systems. Global Digital Forensics’ founder offers some industry insight into how malware like Havex is introduced to a network and the importance of taking the time to check into the cyber security posture of vendors and other “trusted” business relationships which could become a gateway for attackers.
Wreaking "Havex"
The Department of Homeland Security (DHS) is tasked with helping maintain the safety and continuity of the nation’s critical infrastructure. So it is a big deal when they issue an alert about a coordinated cyber attack which could jeopardize Industrial Control Systems (ICSs), like they did on Wednesday, June 25th, about a Remote Access Trojan (RAT) malware package known as Havex. Joe Caruso, Global Digital Forensics (GDF) founder and CEO/CTO, hopes it serves as a wakeup call. “We are past the days when cyber security was strictly considered an in-house issue. The reality today is that every “trusted” entity you deal with in the digital world should be checked out as far as their cyber security posture too, because like Havex shows, if hackers can infiltrate any one of your “trusted” suppliers, vendors, application providers, or any other entity you share digital information and/or assets with, enemies can covertly find their way inside the gates to do as they please.”
New fears from old tricks
“When Stuxnet wreaked havoc on the Iranian nuclear program back in 2010 by causing their enrichment centrifuges to malfunction and set them back months, if not years, it showed what kind of crippling chaos can be unleashed when ICSs (Industrial Control Systems) are successfully targeted and attacked by hackers. It was only a matter of time before that same kind of power found its way to the doorstep of our own critical infrastructure industries as well. What should really get attention in this case is the fact that vendors were first infiltrated and the Havex malware was built right into the software they had available for download, giving them a back door into every infrastructure ICS that downloaded it. It may sound like a clever new tactic to the uninitiated, but it is just another classic watering hole attack that we see all the time. Trust is the weapon; unauthorized access and all the costly consequences that come with it are the aftermath,” warned Caruso.
Depending on luck is not an effective security strategy – Vetting a vendor’s cyber security posture is a much better idea
“SCADA systems (Supervisory Control and Data Acquisition) of critical infrastructure targets are tantalizing for hackers in many arenas, from state-sponsored saboteurs from other nations looking for a cyber-warfare advantage, to hacktivists trying to make a political or ideological statement, or even a lone wolf hacker just looking for some notoriety in underground hacker circles, and by compromising a system or network of a vendor, partner or other entity doing business with our infrastructure organizations, they can get their foot in the door for full access even if the targeted organization has gone through great pains and resources to secure their digital assets. That’s why is it essential today to find out how those outsiders’ security posture stacks up. Have regular vulnerability assessments been performed by experienced cyber security professionals? Has regular penetration testing been done to identify and rectify weaknesses in their security chain? Have applications been tested for unwanted malware and/or other vulnerabilities? Have deep scans been regularly performed to identify and neutralize any resident malware like rootkits and RATs? Do they have detailed documentation from trusted professionals to back up their claims? These are the things we do for our clients, and if an outside entity is to be trusted in today’s threat landscape, they should have to be up to snuff, and be able to prove it too,” said Caruso. “Our experts can help clients not only test and secure their own networks, systems and devices, but can also significantly raise awareness as to potential problems they may be facing from those other trusted outside entities they are involved with, and we can help review any cyber security documentation, policies and procedures they have to spot dangers and deficiencies before it’s too late.”
Experienced Cyber Security Experts
*Global Digital Forensics is a recognized industry leader in the fields of computer forensics , cyber security and emergency incident response , with years of experience assisting clients in the government, banking, healthcare, education and corporate arenas. For a free consultation with a Global Digital Forensics specialist, call 1-800-868-8189 about tailoring a cost-effective plan which will meet your unique needs, without wasting resources on solutions you simply don’t need. Emergency responders are also standing by 24/7 to handle intrusion and data breach emergencies whenever and wherever they arise. Time is critical if a cyber incident has occurred, so don’t hesitate to get help. For more information, visit our cyber security page.
The Covert Devaluation of US Businesses – Hackers Getting Their Hands on Intellectual Property Proving Costly

Don't trust the illusion, make sure data is secure
The Center for Strategic and International Studies recently released a report estimating the cost of cybercrime and how it has been affecting economies and businesses around the world, evaluating everything from direct theft of funds, to the much harder to gauge ramifications on business due to things like the loss of Intellectual Property, as well as the effect on employment. Drawing on years of experience and some of the conclusions relayed in the report, GDF’s founder talks about how businesses can be devalued without anyone, from those running businesses, to those investing in them, even knowing it’s happening.
Cybercrime costs hundreds of billions annually - that we know of
The Center for Strategic and International Studies (CSIS) was commissioned by MacAfee to gather data and crunch the numbers on the global economic impact of cybercrime, and on Monday, June 9th, the report, Net Losses: Estimating the Global Cost of Cybercrime, was released. While the number making headlines from the report is the almost half a trillion dollar tally ($445 billion), “the numbers which could not be well gauged are probably the scariest, because they are the ones that are devaluing US businesses every day, often completely undetected and unknown to anyone in, or involved with the organization,” said Joe Caruso, founder and CEO/CTO of Global Digital Forensics (GDF), a leading provider of cyber security solutions for clients ranging from small businesses, to Fortune 500 companies.
Unknown, unseen, but not unfelt.
After spending over two decades in the cyber trenches helping clients beat back the constant onslaught of cyber attackers, Caruso and his team of cyber security specialists and emergency responders have seen just about everything. “What really leapt out at me from this particular report was that they really went through some exceptional effort to explain some of the critical aspects of cybercrime and cyber security that often go unnoticed and never seem to be talked about, yet can be devastating to businesses of virtually any size, although small to medium sized businesses often take the hardest blows because they simply can’t afford to weather the storm; I’m talking about the loss of IP (Intellectual Property), which in today’s “plugged in” world is often the meat that makes the meal. When a business invests in R&D (Research and Development), whether it’s in manufacturing, engineering, the pharmaceutical industry, technology, or any one of countless other industries, it’s both a financial and personnel investment they are counting on to yield dividends. But all of a sudden, a company right in their backyard or halfway around the world comes out of nowhere and is somehow moving at light speed, offering stiff competitions with very familiar ideas. Or somehow, a new competitor seems to be breathing down their neck and getting in contact with that “gold list” of clients that took years to nurture and cultivate, all without the paying the blood, sweat and tears it took the victim to get there. All it takes for disasters like these to wreak havoc on an organization is an undetected intrusion which yields the right data, be it blueprints or design plans for the next big breakthrough, manufacturing secrets that reduce costs and increase output, or even private customer lists. The fact that it can be going on right under their noses without anyone in the organization having a clue it’s happening just rubs salt in the wound once it’s discovered, which hopefully happens before they have to downsize their workforce, or worse, close the doors for good.”
Couple low risk and high reward, safe havens, and anonymity, and it’s easy to understand why cybercrime is such an explosive growth industry.
“The report hit the nail on the head,” Caruso said, “hackers often have little to fear, especially those operating in places where either law enforcement routinely turns a blind eye, like in Russia and other Eastern Bloc countries, India and Brazil, or where the government is funding and/or supporting the attacks, like the coordinated corporate cyber espionage campaigns to gain economic advantages China likes to engage in. Even attackers on the home front can leverage routers and botnets from these areas to fly under the radar and function with near impunity. Add in the growing underground black market where exploit kits and botnet access can be easily bought and sold by anyone with a little cash and the will to plunder, using anonymous currencies like Bitcoins, and it’s a perfect storm everyone has to somehow weather, from the largest corporations in the world, to a grandparent staying in touch on Facebook. So calling it an explosive growth industry is certainly not overstating things by any stretch, because for hackers, they know it’s mostly reward with very little risk. In our business we see the fallout every day, and if we’re called in too late, it can be gut-wrenching to watch the aftermath of a successful attack unfold.”
Testing networks regularly and raising everyone’s social engineering awareness within an organization are the keys to cyber survival.
“We see it just like the rest of the cyber security industry,” said Caruso, “the most common entry vector for attackers is usually a successful phishing or spear phishing campaign. And with the magnitude of information at hackers’ disposal like publically accessible registry databases, and the wealth of informational available on social media platforms like Facebook, Twitter, and LinkedIn, gathering information which lends the perfect personal touch to make a spear phishing email seem legit has never been easier. When we do penetration tests for companies, we put them through a live fire spear phishing campaign as part of the process, many times using nothing more than the publically available information we can gather. We’ll use letterhead we find on papers and reports published online, we’ll use signatures we find on corporate documents posted online, friends or vendors of the business we find in social media, and anything else we can get our hands on to make things look like the correspondence is coming from a trustworthy source; and we’ve never failed to get the credentials we need to gain access to the client’s network. It’s a hard hitting lesson that really serves as an eye-opening wake up call, and when we’re done, we help them remediate their weaknesses on everything from both a technology standpoint, to raising awareness enterprise wide and showing them what to look for. The human element is almost always the weakest link, and if it does not get the attention it deserves, you may as well flush away the money you spend on inadequate vulnerability assessments and penetration testing, which must be done regularly if a business doesn’t want the value of their company to sink to unfathomable levels due to long term cyber campaigns that are sucking the lifeblood out of them without anyone having a clue it’s even going on.”
The right cyber security professionals are just a phone call away.
*Global Digital Forensics is a recognized industry leader in the fields of computer forensics, cyber security and emergency incident response, with years of experience assisting clients in the government, banking, healthcare, education and corporate arenas. For a free consultation with a Global Digital Forensics specialist, call 1-800-868-8189 about tailoring a cost-effective plan which will meet your unique needs, without wasting resources on solutions you simply don’t need. Emergency responders are also standing by 24/7 to handle intrusion and data breach emergencies whenever and wherever they arise. Time is critical if a cyber incident has occurred, so don’t hesitate to get help. For more information, visit our cyber security page.
Hacking Power Squared – Scary Details on Big Botnet Takedowns Coming to Light
 Massive financial fraud, data for ransom and other sophisticated attacks are par for the course when it comes to giant botnets, and as details trickle in about some of the biggest botnet takedowns ever, US businesses better take notice. GDF’s founder discusses some of these newest revelations and the importance for organizations to undergo regular in-depth testing and to have sound emergency response plans in place.
Massive financial fraud, data for ransom and other sophisticated attacks are par for the course when it comes to giant botnets, and as details trickle in about some of the biggest botnet takedowns ever, US businesses better take notice. GDF’s founder discusses some of these newest revelations and the importance for organizations to undergo regular in-depth testing and to have sound emergency response plans in place.
Devilish Details
On Tuesday, June 3rd, Reuters published an article about details that have started to emerge on the takedown of the GameOver Zues botnet which infected up to a million machines and netted the group behind it over $100 million dollars along the way. By coupling financial fraud malware with the data-hostage-taking Cryptolocker malware, which found great success last year, GameOver Zues packed a powerful punch.
“The first priority of course is to prevent the initial infection when it comes to botnet attacks,” said Joe Caruso, founder and CEO/CTO of Global Digital Forensics (GDF), a premier provider of cyber security solutions for businesses, “but with so many constantly evolving variables, no security is perfect. So the next best approach is to regularly test for the sophisticated malware which standard antimalware/antivirus solutions simply stand no chance against. To do that, it takes a very different arsenal of professional tools and the expertise and experience to wield them correctly. And in the event something nefarious manages to get through between testing cycles, which far too many companies don’t schedule often enough, then it all comes down to an effective emergency response plan which will quickly escalate the event so qualified responders can snap into action to identify the attack, stop it in its tracks, and best manage the aftermath, and by extension, both the costs financially and to an organization’s reputation and integrity.”
So what is a botnet?
“Put simply, a botnet is an army of compromised systems, called zombies, which can be controlled by an individual or group to carry out synchronized attacks. This not only makes it much more difficult to track down the culprits, but also amplifies the computing power at their disposal exponentially. So to add insult to injury, they are basically making accomplices of sometimes millions of users without their knowledge, as the malware that compromised each “zombie” typically goes undetected because of their ability to fool the standard off-the-shelf security solutions that most users have in place as their only line of defense,” explains Caruso.
Seeing is believing? Not necessarily in the world of cyber crime.
The sophistication of botnet attacks can also be the stuff of nightmares, as detailed in an article published on June 4th in Gizmodo in relation to information recently released about last year’s takedown of the Citadel botnet, which apparently was responsible for up to 98% of the online financial fraud in Australia before Microsoft’s Cyber Crime Center teamed up with authorities in multiple countries to bring it down. If it wasn’t bad enough that the malware employed by Citadel was able to vacuum credentials and account information when it recognized financial transaction pages, but there was also an available man-in-the-middle component which was able to record balances and other account information and then deploy a spoofed page to the user so everything looked like it was in order while transactions had time to be carried out in the background.
The art of deception
“Deception is always the name of the game,” said Caruso, “ Whether it’s a phishing email that’s made to look like it’s coming from a recognized and trustworthy source, with links to a fabricated website which can look quite convincing, or the evasion techniques malware uses to circumvent standard antivirus and antimalware solutions, the goal is to make you trust your eyes on face value. But to survive and thrive in the cyber world today, you have to learn to instinctively look deeper. Our vulnerability assessments and penetration tests are designed to help clients raise that awareness enterprise-wide.“
Cyber attacks can happen to anyone, be prepared in advance.
According to Caruso, “It’s a harsh truth, but a truth none the less; outside of completely unplugging from the internet and relying on digital technology, there is simply no way to stay protected against every type of possible threat. Hackers don’t sit on their hands, they are always on the lookout for previously undiscovered vulnerabilities, known as zero-day attacks, and they are always changing, improving and refining their techniques. On the security side of the fence, it’s a daunting task to plug the millions of holes already out there and also have to be concerned with threats security professional haven’t even thought of yet. On the other side of the fence, an attacker only needs to find one flaw, so obviously, they have the advantage. We help our clients stay as up-to-date as possible, but if the unthinkable does happen, we also have emergency responders on call 24/7 every day of the year, so we can jump right in and often start mitigating the attack immediately with remote technologies, or we can have boots on the ground within hours, not days, thanks to our network of responders strategically positioned across the country if a physical presence is needed given the situation. We also help clients design and improve emergency incident escalation policies and procedures so everyone knows exactly what to do in the event of a cyber emergency like a data breach or intrusion. The end–effect cost of a successful attack is significantly reduced if the right steps are taken right out of the gate, but on the flipside, making the wrong moves early on their own with untrained in-house personnel can end up costing an organization everything.”
The right choice
*Global Digital Forensics is a recognized industry leader in the fields of computer forensics, cyber security and emergency incident response, with years of experience assisting clients in the government, banking, healthcare, education and corporate arenas. For a free consultation with a Global Digital Forensics specialist, call 1-800-868-8189 about tailoring a cost-effective plan which will meet your unique needs, without wasting resources on solutions you simply don’t need. Emergency responders are also standing by 24/7 to handle intrusion and data breach emergencies whenever and wherever they arise. Time is critical if a cyber incident has occurred, so don’t hesitate to get help. For more information, visit our cyber security page.
Another Giant Falls – eBay Hack Exposes Personal Information of Up To 145 Million Users
 Once again, a corporate behemoth found itself making headlines for all the wrong reasons this week when it came to light that eBay had been successfully hacked about a month ago and up to 145 million users had their personal information exposed in one of the largest data breaches in history. Joe Caruso, founder and CEO/CTO of Global Digital Forensics, sheds some light on how these mega breaches keep happening and discusses the costly fallout that can accompany data breaches of any magnitude, as well as some steps companies can take to better protect themselves.
Once again, a corporate behemoth found itself making headlines for all the wrong reasons this week when it came to light that eBay had been successfully hacked about a month ago and up to 145 million users had their personal information exposed in one of the largest data breaches in history. Joe Caruso, founder and CEO/CTO of Global Digital Forensics, sheds some light on how these mega breaches keep happening and discusses the costly fallout that can accompany data breaches of any magnitude, as well as some steps companies can take to better protect themselves.
Does Size Matter? Not in the Cyber World
It’s not supposed to be easy to compromise the network(s) of a corporate entity with the size footprint eBay has globally, but as was reported earlier this week by Reuters and most major news outlets on May 21st, it did indeed happen. Companies of this size are typically trusted by the public to have all their ducks in a row when it comes to their cyber security posture, and they do spend vast resources and have personnel dedicated to the task of keeping their customers’ data safe. But then how do names like eBay, Target, Neiman Marcus, Michaels and a slew of others keep finding themselves putting out the costly fires that inevitably follow a mega breach? Global Digital Forensics (GDF) founder and CEO/CTO, Joe Caruso, says, “More often than not, the chink in the armor is not the technology, the desire or the will, it’s the human element that proves fallible. All it takes for hackers to get their foot in the door is one individual not paying close enough attention, or worse yet, lacking regular awareness training on what to watch out for. Social engineering is the most powerful tool in a hacker’s arsenal today, from phishing and spear phishing campaigns, to bogus ads and popups that lead users down a very dark road that ends in the delivery of malware like rootkits and RATs (Remote Access Trojans). Once this kind of malware gets introduced to the corporate network, or network credentials are unknowingly gleaned from even one user, it will soon be time to notify all their customers, vendors and investors, call the lawyers and call the publicist, because things will be getting ugly fast, and the corporate reputation is going to take a beating. The initial reports on the eBay hack mentioned a few users being compromised which led to the successful breach, so once again, the proof is in the pudding.”
The Three Golden Words to Improve Cyber Security – Test, Learn, Strengthen
“At GDF, we’ve been helping clients bolster cyber security for over two decades, and we’ve seen it all. It is because of that invaluable experience that we take the social engineering aspect very seriously when we perform vulnerability assessments and penetration tests, which is basically us assuming the role of real-world black-hat hackers to infiltrate a company’s network so we can identify the weak links in the security chain, without the client having to suffer the real-world consequences. We’ve never been unsuccessful in accomplishing a compromise during the social engineering phase of our testing. And I can tell you this, nothing has a more powerful impact for raising user awareness enterprise wide than when we catch personnel red-handed after designing a bogus website, and launching a spear phishing campaign that typically gets anywhere from 20% to 90% of a company’s work force to take the bait. Hackers have been honing their skills and improving techniques for years and they are very good at it, but so are we. It’s also a powerful lesson on the second biggest problem we find in many organizations we are called in to test - the weak password problem that still dominates the corporate world. When employees give up their credentials during our social engineering testing, being able to call out “John Smith” and his “abc123” or “qwerty” password leaves a sting he won’t soon forget, and presto, he starts using strong passwords from then on, strengthening the entire organization as a whole.”
Emergency Response – Making the Right First Steps is Crucial
“In a world of magic wands, unicorns and pixie dust, maybe there is such a thing as perfect cyber security protection, but we all know that’s not the world we live in. The best we can do is make it extremely difficult for hackers to breach a network by identifying every weakness we can and significantly improving awareness for each and every user within an organization. That will thwart the vast majority of threats every business faces on a daily basis, but if the unthinkable does happen and a breach does occur, an organization’s survival will depend on their response. That’s why we have a network of emergency responders on call 24/7 every day of the year, strategically positioned across the country, and the globe, so we can respond within hours, not days, and many times even start the process remotely right away, to quickly and effectively identify the attack, stop it in its tracks, eradicate it and help clients immediately begin the damage control phases of notification, dealing with regulatory compliance issues and calming anxious customers, vendors and investors by being able to detail exactly what happened, what is being done and what new improvements will be made to prevent any type of similar incident from happening again in the future. Silence is a killer when it comes to public perception, and the faster you get in front of the squall, the less damaging the effects will be on the organization, and that means significantly lower costs in the long run and much better chances the organization will actually survive the event. So the best advice is to make the choice today to do something about it, and sleep easier knowing you’ve got the right plans already in place. It just takes one call, you just have to sit down and actually make it.”
Customized Cyber Security Solutions are the Smart Choice
Global Digital Forensics is a recognized industry leader in the fields of cyber security and emergency incident response, with years of experience assisting clients in the government, banking, healthcare, education and corporate arenas. For a free consultation with a Global Digital Forensics specialist, call 1-800-868-8189 about tailoring a cost-effective plan which will meet your unique needs, without wasting resources on solutions you simply don’t need. Emergency responders are also standing by 24/7 to handle intrusion and data breach emergencies whenever and wherever they arise. Time is critical if a cyber incident has occurred, so don’t hesitate to get help. For more information, visit our cyber security page.
Are Your Cyber Security Measures “Doomed to Failure?” If Social Engineering Isn’t a Prime Concern, They Most Likely Are

Times are changing
When even antivirus software giants like Symantec publicly throw their hands in the air and say the industry is “dead” and “doomed to failure,” like their senior vice president for information security, Bryan Dye, said in a Wall Street Journal article published last Tuesday, it’s clear that tactics to secure data and other digital assets must finally evolve from ineffective passive resistance, to aggressive vulnerability detection and equally aggressive coordinated response plans.
If you want to keep your eye on the ball, take a long, hard look at social engineering weaknesses
Network vulnerability testing is the first crucial cog in this necessary sea-change in thinking, but many companies are falling short by not focusing enough attention on the human element. Robert Knudsen, Northeast Regional Manager for Global Digital Forensics (GDF), and an experienced CHFI (Certified Hacking Forensic Investigator), has been helping guide clients through the constantly evolving cyber battlefield for years. To him it’s a simple matter of common sense, “If you are going to scan your networks for vulnerabilities, why not scan your employees for vulnerabilities as well? After all, that’s where the most devastating and costly attacks predominantly find their first foothold into a network.” In other words, ignoring social engineering is pure folly for anyone concerned about data and digital asset security.
Spear phishers may be targeting fewer recipients per campaign, but their aim has never been better
Spear phishing is one of the most effective social engineering strategies hackers have at their disposal to target specific organizations and/or individuals in an effort to breach their network. Just one recipient clicking on an attachment infected with malware, or following links to a bogus site that looks convincing enough to entice them to enter their credentials can open the door to a full scale network breach. According to Symantec’s 2014 Internet Security Threat Report, the number of targets spear phishers went after per campaign in 2013 was down significantly compared to 2012, by 76%, and the recipients receiving these malicious emails per campaign was also down by 81%. But the number of campaigns launched was up by 91%, and the duration of an average attack was also up from 3 days in 2012, to 8.2 days of undetected access in 2013, a whopping 173% increase. These numbers clearly show that spear phishers have been refining their tactics considerably, and to great effect, by forgoing the carpet bombing mentality in favor of more precise surgical strikes. They are not doing it by chance, they are putting in the research it takes from the many sources of publicly available information online, from social media sites, to an organization’s own website. With an organization’s internal hierarchy, names and contact information at their disposal, spear phishing emails can be so well crafted and convincing they can be very hard to distinguish from the real thing. GDF puts a strong focus on social engineering during their penetration testing phase, going through the same efforts real-world hackers do to craft these kinds of convincing campaigns, and then helps an organization raise awareness enterprise wide according to the results. To date, GDF has never failed to penetrate a client’s network, and the eye-opening results go a long way in making the lessons learned stick.
Cyber survival today is also about how you respond when you get knocked down
It’s an undeniable fact; eventually, every organization gets hacked in some form or fashion, whether it comes from the outside, or from within. But the organizations that will weather the storm will be the ones with predetermined emergency response policies and procedures ready to go. Global Digital Forensics has experienced emergency response teams on call and strategically positioned across the country and the globe to be able to respond quickly and effectively whenever an emergency strikes, day or night. And for organizations that use GDF to perform professional vulnerability assessments and penetration testing, no-retainer Service Level Agreements (SLAs) are available so you can always have expert responders waiting in the wings should an emergency event materialize, without having to spend anything if nothing happens. GDF can also help clients craft emergency response policies and procedures from scratch, if none exist, or help bring existing plans up-to-date to meet today’s threats, as well as design an effective escalation matrix which can be easily followed to make sure your initial response efforts move like clockwork. It’s as close to a no-lose-scenario as it gets to deal with cyber emergencies, from identifying and stopping the attack, to reporting procedures and other regulatory compliance issues that may be involved for specific industries.
The right cyber security plan is cost effective and tailored to suit your unique needs
Global Digital Forensics is a recognized industry leader in the fields of cyber security and emergency incident response, with years of experience assisting clients in the government, banking, healthcare, education and corporate arenas. For a free consultation with a Global Digital Forensics specialist, call 1-800-868-8189 about tailoring a cost-effective plan which will meet your unique needs, without wasting resources on solutions you simply don’t need. Emergency responders are also standing by 24/7 to handle intrusion and data breach emergencies whenever and wherever they arise. Time is critical if a cyber incident has occurred, so don’t hesitate to get help. For more information, visit www.evestigate.com.
Social Engineering Awareness Crucial to Survive Today’s Cyber Threats

How may I help you?
You can consider the days when hackers lived only in the shadows long gone. If it wasn’t stressful enough to always be worrying about hackers coming after you from the darkest corners of the digital world to steal, destroy or hold your data hostage, now you have to worry about whether or not you are actually seeking them out in broad daylight. A recent rash of full-press social engineering scams making headlines lately should leave no doubt that it’s far from a baseless worry, and that there can be potentially hefty consequences. The truth is, when it comes to social engineering there is no magic software solution or hardware fix, it’s all about human awareness – which must first be taught before it can be applied.
Social engineering is all about trust
Whether the “con” used is a tried and true email-based phishing or spear phishing scam, or one of these latest pretending to be from well-known companies like Netflix, AOL or Comcast, among others, that incorporate real Google and Bing ads coupled with actual 800 or other toll free numbers, it’s all about making the “mark” feel like they are interacting with a legitimate entity or person they can trust. If that hook is set, everything else is easy, and the inevitable outcome leaves you as the next victim of data/identity theft, fraud, data destruction, or worse.
Hackers flex some business acumen - Need a target? Why not advertise?
Anyone with a business website knows that it takes a lot of effort to make it up to, and then maintain, first page status for search returns on major on search engines like Google and Bing. But if you want to spend some money, you can also dive into the world of Google or Bing ads that will propel you to the top of search return pages when certain keywords are searched – for a price. It’s a price hackers have decided is worth paying. Now, when you are having trouble with a service and need support, a simple search like “I need Netflix support” can bring up a false ad created by hackers with a toll free number and/or a link to a site that’s been crafted to look very much like the real thing to coax you into entering credentials. Once that’s done (now they already have your account credentials), a splash screen will typically appear that you have been cancelled or some other bogus claim that would prompt you to call for support. Then it’s up to a smooth talking charlatan to convince you that he/she would need to log into your system remotely to help. With full access to your system now to transfer malware for future attacks, or to access other accounts, or exfiltrate confidential data directly, it doesn’t take much imagination to understand the trouble that could lie ahead.
Don’t underestimate the scope of the problem
It’s not just a few isolated incidents here and there either. Google spokesman, Aaron Stein, said they removed 350 million bad ads last year – that translates to one bad ad being removed more than every tenth of a second, every single minute, of every hour, of every day of the year. If that many got caught, how many got through? Even if it’s just a tiny percentage compared to the ones which were blocked, it’s easy to see the numbers are not in your favor, and that social engineering awareness has never been more crucial.
Learning a lesson, without the damaging consequences
The key to stopping any kind of social engineering attack is to raise awareness enterprise wide. One of the best ways to do that is with regular penetration testing that also puts a strong focus on social engineering attempts. That’s what Global Digital Forensics (GDF) provides for clients, doing everything from setting up dummy websites and making phone calls, to creating and launching well-crafted spear phishing campaigns so that the weakest links in the security chain, the human links, can learn the hard lesson that only comes from actually being caught off guard. But instead of a hacker teaching a lesson that can have dire and far reaching consequences, GDF will use the results to help organizations raise awareness, and even help with training personnel on what to look for, like false domain names, redirect links and spoofed email headers, just to name a few.
Getting ahead of the problem is the most cost-effective approach to solving the problem, so get help today!
Global Digital Forensics is a recognized industry leader in the fields of cyber security and emergency incident response, with years of experience assisting clients in the government, banking, healthcare, education and corporate arenas. For a free consultation with a Global Digital Forensics specialist, call 1-800-868-8189 about tailoring a plan which will meet your unique needs. Emergency responders are also standing by 24/7 to handle intrusion and data breach emergencies whenever and wherever they arise. Time is critical if a cyber incident has occurred, so don’t hesitate to get help. For more information, visit http://evestigate.com.
Cyber Security Tips & Advice for Safer Travels
 To stay connected while travelling today, there are certainly a lot of gadgets and devices to choose from. But whether it’s a smartphone, laptop, notebook, tablet, all-in-one or any combination, you still need access to the Internet. That’s where things can get dicey, because there really are unsavory elements out there that specialize in preying on unsuspecting travelers in unfamiliar surroundings just trying to get “connected.” Whether it’s getting work done on a business trip (hopefully it’s a business trip), staying connected with family and friends, or just surfing the Web, hackers know you want to connect and they will do their best to get in the middle of those plans so they can access your device and/or important data, not to mention being more than willing to just steal the device itself if they can.
To stay connected while travelling today, there are certainly a lot of gadgets and devices to choose from. But whether it’s a smartphone, laptop, notebook, tablet, all-in-one or any combination, you still need access to the Internet. That’s where things can get dicey, because there really are unsavory elements out there that specialize in preying on unsuspecting travelers in unfamiliar surroundings just trying to get “connected.” Whether it’s getting work done on a business trip (hopefully it’s a business trip), staying connected with family and friends, or just surfing the Web, hackers know you want to connect and they will do their best to get in the middle of those plans so they can access your device and/or important data, not to mention being more than willing to just steal the device itself if they can.
So with spring unfolding and vacation season just around the corner, our team at GDF wanted to offer some tips and advice to help keep your sensitive information and personal devices safe from looming threats.
WiFi/Wireless Access
Not everybody has a roaming data plan, so many travelers are looking for the next best thing, a wireless hotspot for Wi-Fi access. Hotels, airports, fast food places, interstate gas stations and a host of other locations can offer Wi-Fi access, often for free, and many desperate travelers will jump on the opportunity. But as these networks are accessible by everyone, they are also highly insecure.
A favorite trick hackers like to use is to set up their own hot spot in the vicinity of another, often using a network name that’s close to what is expected, like a misspelled hotel name, or a series of number after the name. When you search for wireless networks, it comes up on the list and they hope you take the bait. Now they can intercept everything you transmit and receive, our saddle you with malware. So the best rule to follow is this; if you don’t want the information you are transmitting or receiving to be disclosed to an undesired party, don’t send it over a free wireless network. If you do decide to use it anyway, make sure to check with the location offering the wireless connection if multiple hotspots seem to be available so you choose the one they really control.
Shared/Public Computers
So you were trying to unplug from the digital world or had an equipment disaster, whatever the case, you can’t rely on your trusted device to get Internet access and are forced into using a public or shared computer. Assume everything you do can be seen and/or recreated by someone else. Never access sensitive information like bank accounts from a shared or public system. A hacker-installed keylogger, for instance, would allow them to recreate everything you typed in, including user names and passwords. And if you are accessing your accounts from a public system, they know chances are good you are away from home and they will have some time to do what they do before being noticed, and that can prove costly in more ways than one.
Bluetooth Access
Bluetooth is that short-range radio frequency connection often relied on to connect two devices in close proximity, like allowing for hands-free calling from your smartphone while driving. For the connection to work, devices must be paired, which typically requires a user to confirm the attempted pairing, and only once that secure connection is confirmed can data be sent freely between the paired devices. But there are dangers, especially if Bluetooth connectivity settings are not properly configured on the device(s). If your device is set to allow for automatic connections, meaning any Bluetooth network can connect to your device without any confirmation required, anyone could potentially connect to your device without authorization and do what they please, from stealing data, to installing malware. It’s best to disable Bluetooth networking altogether while traveling to thwart unwanted connections, but most importantly - check your connectivity settings before you travel!
Cyber Safety Tips:
- Password protect your device – otherwise, it is very tempting low-hanging fruit.
- Make sure your applications and antivirus software are up-to-date before you leave – you don’t want to rely on an unsafe connection while you’re travelling to do it.
- If possible, install a firewall – this will provide an added layer of protection against unauthorized access.
- Limit password attempts - some devices have an option that will erase all data if the password is entered incorrectly 10 times. Enable this option so that if you lose the device, that’s all you’ll lose.
- Gotcha tools - you may want to look into anti-theft measures, like remote locking and/or tracking. Some even allow you access your device’s camera so you can take video or snapshots through a cloud application – talk about red-handed.
- Disable your wireless (Wi-Fi) connection when you are not actually using your device to connect to the Internet – better safe than sorry.
- Bring your charger - don’t charge your devices by plugging into any foreign device. Just plugging into a USB port of a strange device makes you susceptible to malicious software downloads – you don’t even have to click on anything, plugging in is enough.
Never plug in or load any foreign media – everything from USB sticks and flash drives, to CDs and DVDs, can leave you infected with malware. - Contact Details - whether you make a wallpaper screen or include a handwritten note, make sure your local contact information is with your device so it can be returned if someone finds it – yes, it does happen, especially password protected devices.
Different Strokes
Some countries have very different rules when it comes to digital information and privacy. What might be legal in one country, may not be legal in another. Check on the rules of the country you intend to visit, you may find those movies or music you have downloaded on your device can cause you some big problems, and border agents are authorized to seize it if that’s the case. Intellectual property can also be subject to very different rules, so don’t be afraid to contact your embassy for more information before you leave.
Don’t forget about physical security
Smartphones, tablets, notebooks and other digital devices are prime targets for thieves. They are high dollar items that are always in demand and easy to sell. Treat your digital devices like valuable jewelry, don’t let them out of your sight. Lock them up when you are not in the room and don’t leave them charging unattended. It’s also a good idea to always carry your devices with you when flying to reduce the risk of loss or damage. Otherwise, you may be relying on public systems for the duration of your trip if you need to get connected, which is not a good situation to find yourself in unexpectedly.
Last but not least
Back up your data before you leave!
And of course, be safe, and enjoy your travels,
Your team at Global Digital Forensics
We're always here to help with all of your cyber security, computer forensics and eDiscovery needs, just give us a call at 1 (800) 868-8189, or schedule a free consultation by clicking below.
Lawyers and Law Firms Prime Targets for Hackers
There are three unquestioned sanctums of confidentiality that everyone is familiar with; a confessional, a doctor’s office, and a law office. But how do they stack up in today’s world of cybercrime and data theft?

Desired Data
Thankfully, we can cross confessionals off the prime targets list for hackers because they are supposed to be done the old-fashioned way - in person, with no electronic data involved, just you and your priest. A doctor’s office, on the other hand, can yield personal information which could lead to identity theft and the possibility of leveraging private information like diagnoses and treatments for material gain. But lawyers and law offices, that’s goldmine territory for hackers. Personal information, corporate information, legal strategies, contract negotiations, financial books, patents, trade secrets, investor information and everything else imaginable can cross a lawyer’s desk, and hackers know it.
Cyber threats aplenty target legal professionals
Because of the wide array of privileged and sensitive information lawyers and law firms routinely deal with, there is no ceiling to the level of threat sophistication they can face. Every kind of hacker must be considered. There are the well-funded and highly advanced cyber armies of foreign nations like China, Russia, Korea and Iran conducting industrial espionage campaigns on a daily basis, private investigators working for the opposition looking for any advantage they can find, organized cyber-crime rings, politically motivated actors, lone-wolf hackers and every type in between, all chomping at the bit to gain access for profit, leverage, or advantage.
In the legal arena, making a “reasonable effort” to protect data is not a choice, it’s a requirement
Protecting paper documents has always been the cornerstone of the legal profession, with routines and procedures refined over time to make the process run like a well-oiled machine - most of the time. For a thief to lay hands on all those hardcopy documents required a physical presence, making it a lot harder to pull off the job. But today, hackers can just let their fingers do the walking. It was one of the main reasons the ABA amended Rule 1.6 in 2012 explicitly stating that, “A lawyer shall make reasonable efforts to prevent the inadvertent or unauthorized disclosure of, or unauthorized access to, information relating to the representation of a client.” And no, simply having off-the-shelf antivirus/antimalware solutions in place may not satisfy “reasonable efforts” when opposing counsel takes aim. That’s when words like sanctions and fines can enter the conversation, and those are words no lawyer or litigant ever want to hear.
It’s time to see where your security stands
The cornerstone of effective cyber security is understanding the threat landscape and identifying the most problematic threat vectors as they pertain to your unique situation. That’s exactly what GDF’s vulnerability assessments and penetration tests are designed to do. We start by looking at the big picture, from policies and procedures being employed internally to secure data, to the entirety of the digital architecture being used. From networks to stand alone systems, from Wi-Fi connections to digital devices like smartphones and tablets, knowing where every bit of data travels is essential. Once that is done, we switch hats and take on the role of a real-world attacker to shine a spotlight on weaknesses. We’ll use everything from brute force attacks to customized spear phishing campaigns, depending on what weak points were uncovered during the initial cyber threat assessment. And with over two decades of dealing with legal professionals in our capacity as a computer forensics and eDiscovery solutions provider, we understand exactly what lawyers and law firms face from both a security perspective and the possible consequences a lack thereof can have on a case in court.
With the Global Digital Forensics, legal professionals have an invaluable ally, formidable on both the cyber security and eDiscovery fronts. So call us today at 1-800-868-8189 for a free consultation with one of our specialists and let us help to tailor solutions that will satisfy your unique needs.
Watering Hole Attacks Show Hackers for the Cunning Predators They Are
Law firms, defense contractors, design companies, infrastructure facilities and manufacturers are high on the list when it comes to cyber espionage. But they are far from alone on that list with so much sensitive digital information in play across nearly every industry. And with more and more organizations finally waking up to the real scope of the espionage game, and the high stakes involved, adversaries are forced to constantly vary the tactics they rely on to quarry their prey. Hackers know brute force attacks are becoming increasingly difficult when their aim is to target a specific organization or industry, so sometimes they go old-school – very old school - as in the watering hole attack.

What is a watering hole attack?
Watering hole attacks have been an effective favorite of natural predators since before mankind roamed the earth, because they’ve always worked. It didn’t take long for predators to realize that instead of expending precious energy to find and chase prey, it’s a lot easier to just figure out where they are going to be. And since they all have to head to the watering hole to drink eventually, it’s a perfect spot for an easy ambush. Hackers didn’t take long to put their own spin on it as well. By figuring out the sites frequented by the players from the particular industry or organization they want to target, they could try to compromise any one of those less secure locations, and if successful, use it as an ambush spot to quietly deliver a malware payload like a RAT (Remote Access Trojan) to all the unsuspecting industry visitors that stopped by for a “drink.” Once that’s accomplished, the hackers have their foot in the door to all of their respective networks, free to steal, modify and/or corrupt ESI (Electronically Stored Information) at will.
What kind of sites do hackers use as watering holes?
There are two key criteria for hackers to set up a successful watering hole attack. First, the site has to be frequented by the type of visitors the hackers are targeting, whether it’s a particular organization or broader industry-specific traffic. Second, they have to be able to compromise it. Aside from those requirements, every kind of site is fair game and a potential watering hole. Blogs, forums, vendor sites, industry news sites, they’re all favorites and have all been used, among many others. Hackers creating bogus forums, blogs and sites from scratch fashioned to look legitimate has also been done, sometimes garnering a respectable amount of industry traffic in the process, before being shut down to avoid detection.
Cyber predators come in all shapes and sizes.
The sophistication of watering hole attacks can vary greatly, mostly dependent on the predator(s) behind it. Foreign actors, many funded by the deep pockets of rival governments, like China, Russia, North Korea and Iran, rely on attacks like these as the main staple of their industrial espionage campaigns today. They want defense plans, design specs, manufacturing secrets and other valuable intellectual property to stay in and ahead of the game on the world stage. It’s nothing new, but with most of the world’s information now found in digital form, the old cloak and dagger spy game has gone mostly digital too. One gigabyte of information can be stolen in a moment today, whereas in the old days you would have to fill a pickup truck with over a thousand books and make it to the drop point in order to get away with the same size bounty. But governments are not the only ones relying on watering holes, everyone from organized crime rings to lone wolf hackers are happy to get in on the action. If your data has value, they’re more than willing steal it by any means possible and cash it in on underground black market sites where buyers abound.
How can organizations fight back?
Increasing awareness enterprise wide and regular threat testing are essential. You can’t control the security weaknesses of other sites, so the task of maintaining security falls on your end. Religiously using tools like DBRT (Data Breach Response Toolkit), by Global Digital Forensics (GDF), has to be a top priority. It’s designed to sniff out and eradicate even the most sophisticated malware that standard antivirus/antimalware programs miss because they rely on signature identification, like RATs, polymorphic viruses, keyloggers and other advanced payloads. DBRT lets your IT security personnel monitor, identify, and eliminate threats like these across the entire network from a single command and control client. So if anyone on the network got compromised by a watering hole attack, you can find and remove the malware and keep your digital assets safe. DBRT also allows you to inoculate your systems from reinfection from any malware it identified, a huge bonus when it comes to watering hole attacks in case more personnel visit the same malicious site.
The right help is just a phone call away
Let GDF help you survive and thrive in this increasingly dangerous digital world. Call 1-800-868-8189 today for more information about DBRT, or to receive a free consultation with one of our security specialist to help craft a plan that suits your unique needs. With our proven ability to streamline effective solutions, it’ll cost less than you think, but the benefits could prove priceless.
POS Systems, Malware and XP Converging to Form a Perfect Storm for Retailers in 2014
2013 was a harsh reality check for many retailers. POS (Point of Sale) system hacks on Target, Neimen Marcus, Michaels and a host of retailers across at least 11 countries made for scary headlines to close out the year. Well over 100 million holiday shoppers were directly affected, and confidence in card transactions, the lifeblood of most retailers today, took a real hit. Losses from Target’s breach alone will be well into the ten figure range when all is said and done, and that’s without their customers’ finances even in the conversation.

The big question now is, what does it all mean for retailers in 2014? The answer is, a real storm is brewing.
RAM scraper revival
RAM scrapers are not new, but thanks to the unequivocal successes RAM scraper exploit kits like Black POS and Chewbacca had in those devastatingly effective high-profile attacks last year, retailers can count on hackers milking this weakness until it no longer reaps big rewards. The revival is on.
What exactly is a RAM scraper?
In short, a RAM scraper is malware that intercepts information that would normally be encrypted (like POS transactions) while they are in the system or device’s RAM memory. By getting the data out of RAM, it hasn’t been encrypted yet. It is still in plain text form while being initially processed in memory. Only after this step is it encrypted and sent on its way to whatever secure server it ‘s supposed to go to. The Target, Niemen Marcus and Michael’s hacks and the other big ones recently, like the Chewbacca Trojan (another recent RAM scraper success), brought a lot of attention to the problem, and fear to retailers. RAM scrapers can be next to impossible for many standard antivirus/antimalware solutions to detect because hackers are steadily employing more antivirus evasion techniques or packing tools to alter malware signatures.
So what can you do?
Identifying and remediating the attack as quickly as possible is obviously paramount. Unfortunately, signature-based detection is the standard template for most of detection products still being widely used today. So it’s easy to see why non-signature reliant next-generation antimalware solutions, like GDF’s Data Breach Response Toolkit (DBRT), are becoming more necessary by the day. DBRT can find the most advanced malware out there by sniffing out suspicious system activity, not by relying on a signature that hackers are getting better at disguising every day.
Microsoft is “pulling the plug” on Windows XP - Don’t let it spell the end for your retail business too
If you are a retailer with an XP-based POS system, circle April 8th on your calendar in red. That’s the official “end-of-life” day for Windows XP. That means no more Patch Tuesday security updates from Microsoft. And since part of PCI DSS (Payment Card Industry Data Security Standards) compliance hinges on maintaining current security updates, significant problems are looming large for retailers relying on outdated POS systems. Fines for non-compliance can range from $5,000 to $100,000 a month, which alone could very likely put many smaller retailers into a death spin. Even upgrading the operating system may not be enough. The older applications may not work properly and other integration issues could crop up as well. Workaround attempts like shifting to compatibility mode or virtual desktops will not only slow down and otherwise hinder daily operations, but may not work at all after all the effort. Finally biting the bullet on a new and updated POS system from the ground up is obviously the best choice, but as the costs involved can be a burden just as crippling, many will try everything imaginable just to stay afloat until they are ready and able to switch. In other words, advantage – bad guys.
Get the right help in time
The successes of these recent massive breaches on POS systems already spawned a surge of copycats that are putting their own new variation twists on RAM scraper malware now that these hackers can smell blood in the water. Couple that with the swan song of XP and you have the makings for a perfect storm quickly bearing down on retailers. GDF’s vulnerability assessments can let you know where you stand, both from a compliance perspective and a security perspective, so call us today and let our specialists help you identify and remediate the weaknesses in your entire data environment. Because while weak POS system breaches have been making the big headlines, there are a lot more threat vectors that need to also be considered for effective security - and that is GDF’s domain.
Smart Appliances and Other SPPDs Hacked
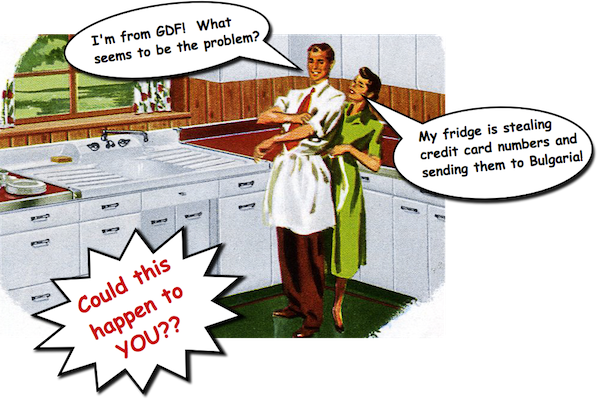
Is there Spam in your refrigerator? If so, you better hope it comes from Hormel Foods, because it finally happened: the first confirmed report of a smart refrigerator involved in sending malicious spam emails.
California-based Proofpoint Inc. revealed some details last week about what they are calling an ""Internet of Things"-based cyber attack involving smart home appliances that took place between December 23rd 2013 and January 6th 2014. So if worrying about all the more familiar threat vectors aiming to assault your network on a daily basis wasn't already enough, now you've got to think about things like televisions, multi-media platforms, home routers, gaming systems, and yes, even smart refrigerators being recruited by nefarious hackers that are up to no good. And with more Smart Personal Peripheral Devices (SPPDs) coming online all the time, it's time to keep them in mind as they crack the list of potential cyber threats.
Time to cull the herd
The attack they reported was global, affecting more than 100,000 consumer gadgets which were basically Shanghaied into serving as part of a botnet. A botnet is a collection of compromised systems and/or devices used by a "bot herder/bot master" as a platform to launch more orchestrated attacks, like sending malicious emails or instigating a Distributed Denial of Service (DDos) attack. In this case, over 750,000 malicious emails were sent by the herd, with full quarter of that spam traffic coming from those far less traditional and often overlooked SPPDs. The attacker(s) also played it smart, limiting each compromised SPPD to send no more than 10 emails, making it a much harder to block specific IP addresses by location to thwart the attack.
How did the hackers get in?
As is often the case when dealing with cyber attacks, human error was largely at fault. In this case, complacency related to setting strong passwords can be blamed for most of the fires. When a consumer gets their new smart refrigerator, TV or entertainment center home, they are ready to plug it in and start using it. So when prompted to set a password, a quick tap on enter sets the manufacturer's default password and away they go. After all, who would want to hack a refrigerator, and why? Well, now you know. The lesson to take away from this is that any time you are prompted to set a password, do it, and make it a strong combination of letters with different cases, numbers and special characters when at all possible.
Another thing to keep in mind is that many of these devices, up to now, are designed with convenience in mind, not security. So don't be afraid to ask questions and get educated on your new device's connective capabilities. It's not a far leap to have a smart home appliance access your smartphone through the handy Wi-Fi or Bluetooth application that came with it, causing a cross-over infection that you can then spread to another system or device, or even your business network.
Smart Appliances - New Industry, New Security Problems
Hopefully this incident will be a real wake-up call to SPPD designers going forward, because if they are going to make devices that "plug in" to the digital world we all share, the bullies and bad guys will be out there lying in wait to leverage them for their own sinister ends ... at your expense.
At Global Digital Forensics, we keep an eye on the most current threat trends and how they can affect you and your business. For a free consultation with one of our specialists to discuss what cyber security solutions may be right for your unique situation, call 1-800-868-8189 today.
Hack Gives Snapchat a Black Eye on Privacy
To Start 2014, Snapchat CEO Perfectly Sums Up Cyber Security Dilemma Most Businesses Face - "We thought we had done enough"
On the heels of a cyber attack that exposed the usernames and phone numbers of 4.6 million Snapchat users, Joe Caruso, founder of Global Digital Forensics, lends some industry insight into the dilemma faced by so many businesses today, which was perfectly summed up in a few words by Snapchat’s CEO that should reverberate with every business heading into 2014.
Cyber Threats Alive and Well as 2014 Kicks Off
Just as 2013 was making its final approach into the history books, Snapchat, creators of a photo messaging app that revolves around user privacy, suffered a data breach which exposed the usernames and associated phone numbers of 4.6 million users. Granted, it’s not as catastrophic as the recent attack on Target that put the valid credit card information of 40 million customers in the wind, but in an exclusive post-attack interview with Carson Daly, Snapchat’s CEO, Evan Spiegel, uttered six prescient words that are far too often repeated after an organization is victimized by cyber attackers, “We thought we had done enough.” Joe Caruso, founder and CEO/CTO of Global Digital Forensics (GDF), a premier provider of cyber security solutions and data breach/intrusions emergency response, has heard that line repeated many times. “But,” Caruso said, “far more often than not, regular testing, basic security measures, awareness, and understanding the basics of the threat landscape would have stopped or severely diminished the damage of many of the attacks GDF has responded to over the years.”
The Cost and Effect Balance of Cyber Security
“In today’s ESI (Electronically Stored Information) driven world, cyber security can never be an afterthought, it has to be a primary consideration. But it doesn’t have to be a black hole of resources, time and energy that many organizational decision makers seem to have in their minds to achieve a good to excellent security posture on the digital front. Grasping and driving home the cyber security basics will get any organization 95% and better of the way there. That’s what the bulk of our business is, helping clients nail down the basics first, and then if they want to close the gap on those few remaining percentage points even further, we can seamlessly transition into helping them combat the more sophisticated and advanced threats that their unique situation dictates. And since we will already have the knowledge gained from our initial threat assessments and testing, already knowing and understanding the organization’s digital asset environment, data flow and regulatory compliance needs, any future costs for more advanced security help are driven down substantially. Not to mention, it gives us a huge leg up when it comes to time-critical emergency response should a breach or intrusion occur, because the hard truth is there is no such thing as a perfect solution for cyber security for any organization relying on digital information and technology; the threats and players evolve every day. But we can get clients close and quickly and effectively respond to any threat that still may manage to get through, both the external variety, and the even harder to prevent insider variety.”
Building a Roadmap to Improved Cyber Security
“Achieving effective cyber security is like any journey, you can’t figure out how to get where you’re going if you don’t know where you are. It’s easy to be lulled in to a false sense of security and to think you’ve done enough just because you finally grabbed the steering wheel, put it in gear and started to drive, but unless you’re heading in the right direction, you could end up in a very scary and dangerous place you really don’t want to be. Our network vulnerability assessments, application reviews and penetration testing solutions don’t only provide clients with a map, we’re more like a full on-board computer and GPS system that can warn you about dangerous conditions, both in the vehicle and on the road ahead, so you can take appropriate measures. And that’s what doing business in the digital world of the 21st century takes, knowing where you are, what weaknesses your vehicle has inside and out, and what kind of threats you’re likely to face on the road today and how to best avoid them.”
Business Reality Today
“The benefits of digital information and technology can be immeasurable, giving businesses abilities that were unimaginable even a decade ago. But with those abilities come responsibilities, and security for customers, employees, investors and vendors has to rank high on the totem pole. It will take some time, energy and resources, but it has to be an expected and included part of any business model today, no matter how large or small the organization. Just ask the CEOs of Target and Snapchat if they would do something different looking back. And they’re the lucky ones, they will probably survive the attack and the aftermath because they have the resources to weather the storm, but most small to medium sized businesses that suffer a big breach end up closing their doors in six months, and that is business reality today. So don’t wait until it’s too late to get professional help, your business' survival could depend on it.”
The Holiday Season Means Phishing Season for Hackers

It’s that time of year again, the holiday season has arrived. Unfortunately, that means it’s also high season for hackers looking to leverage every ounce of holiday chaos to increase their chances of success when it comes to malware delivery, infiltration, virus infections, cyber espionage and theft. Time is of the essence when an organization is attacked, with every delay potentially compounding both the effectiveness of the attack, and the cost of remediation. Global Digital Forensics (GDF) will have emergency incident responders on call 24/7 throughout the holiday season to provide professional assistance and remediation expertise quickly, even on those days most cyber security solution providers are closed, like Thanksgiving, Christmas and New Year.
How do hackers take advantage of the holidays?
Hackers have always heavily relied on deception and misdirection to deliver an initial malware payload which they can then use to open the doors to systems and networks at will, and social engineering, or conning people, routinely plays a big part in making that happen. Phishing and spear phishing emails are a great example. They are a problem year round, disguised as notices requiring action that come from well-known and reputable organizations like Amazon, Paypal, banking institutions or any other organization that large swaths of the population are familiar with and use. But users stand a much better chance of spotting and dismissing them when they don’t make any sense, as they often don’t coincide with that user’s typical behavior. During the holidays though, unusual purchasing and online behavior is the norm. Multiple family members may be making undiscussed purchases with certain shared accounts, a user may not exactly remember the name of every website they visited to find that perfect gift, or because they have been making so many more purchases than they typically do throughout the year with credit and debit cards, the likelihood of identity theft can seem much more realistic, making those phishing emails about unusual account activity much harder to resist.
Helping hackers bait the hook - Social media, gifts and promotions
Thanks to the ever increasing willingness to “share everything” on social media, hackers can also use information users divulge to customize phishing and spear phishing emails for added effectiveness, like a user posting about the luck they had getting that last Playstation 4 from Best Buy and then getting a phishing email disguised to look like it’s from Best Buy about a purchase they made. Also be dubious about offers that seem too good to be true, the link about that $50 dollar iPad offer will most likely lead to a malicious site and an unwanted payload, but no iPad. Hackers will also use things like “friends lists” to send seasonal eGreetings that look like they come from trusted sources, only to deliver a malicious payload once the target opens it to view the contents. Infected USB sticks designed to look like promotions or gifts are also a hacker favorite, delivering their payload as soon as they are attached to a system by a user. So during the holidays it is more important than ever to stay vigilant and approach everything unexpected or unusual with a healthy degree of doubt. These 7 tips to prevent malware infections are a good rule of thumb to follow all year long, but especially during the holidays.
24/7 Cyber Emergency Incident Response
Businesses are especially vulnerable to cyber attacks during the holidays for all the same reasons mentioned above, but with the prevalence of BYOD (Bring Your Own Device) practices being employed by so many organizations, the possibility of crossover infections has also never been higher. Just one employee making a mistake is all it takes to open the doors of a business network to attackers. In the past that mistake would have had to happen at work, but today a personal system connecting to the company network, cloud computing, a USB stick used to share data, or even a mobile device like a smartphone or a tablet connecting through WiFi at work can be all it takes. Global Digital Forensics has handled emergency incident response for countless organizations in a wide variety of industries.
Time matters when responding to a cyber emergency.
With just one toll free call (1-800-868-8189), GDF can get the response and remediation process started any time of the day or night, even weekends and holidays. With a network of emergency responders strategically positioned nationwide and across the globe, GDF’s response times are unrivaled in the industry. In most cases, GDF can even start the process remotely, employing powerful tools like the new Data Breach Response Toolkit (DBRT) to identify, stop, and remediate the threat, and when it comes to data breaches and other cyber attacks, every second counts. GDF has the proven experience in highly regulated industries as well, so regulatory compliance issues, notification headaches and all the documentation needed to satisfy controllers and anxious clients and/or investors will all be handled the right way, significantly reducing the costs and aftermath of any successful intrusion or attack. So if this joyous holiday season hits a cyber snag, don’t hesitate to call right away, expert responders are standing by.
Top Ten Holiday Cyber Scams

The holidays are supposed to be about joy, loved ones, special friends and the spirit of giving. But every year the lowest form of criminals do their best to ruin it for everyone but themselves. This year, your team at GDF offers you a list of the top ten cyber scams people run into over the holidays.
Holiday Charity Scams
The giving spirit of the holidays is truly embodied by helping those less fortunate. The trick is making sure your contribution actually gets to whom it is intended and not criminals looking to profit from your generosity. The best way to avoid being scammed by charity fraudsters is to reach out personally to the paticular charities to which you wish to give. Money or payment information you give to a total stranger or an unknown charity is at risk. So if a cause touches your heart, please do give - just don’t automatically trust social media posts, emails, phone calls or even that knock at the door. Ask questions and make an extra phone call.
Malware Heaven - Holiday Downloads
The holidays can be infectious, and hackers are banking on that. Offers for screensavers, animations or other holiday themed downloads pop up everywhere this time of year. Unfortunately, they can also be jam-packed with all kinds of nasty malware. So if you don’t want a horrible surprise that will only dampen your holiday spirit, be sure to download from sources you know are legitimate, preferably those with clearly stated policies and procedures in place to help ensure malware-free downloads.
FedEx/UPS/USPS Delivery Notices
No one is busier during the holidays that parcel delivery services. Of course, hackers know this too, and will be sending out lots of phishing emails disguised as notifications from popular parcel services like FedEx, UPS and the US Postal Service, coaxing targets to open malicious attachments or follow links to fake sites. To stay safe, don’t click on any attachment or link you get in an email notifying you about a parcel. Legitimate emails will have a prominently displayed tracking number within the body of the email itself, not hidden in an attachment or behind a link. Even if you think it may be valid, don’t follow any suggested links, simply go to the site directly (like fedex.com, ups.com and usps.com) and enter the tracking number yourself. Also, don’t hesitate to call a company directly for assistance using the phone number on their site - avoid using any numbers contained in the email itself, as they too may be fictitious!
Holiday Employment Opportunities
When the holidays roll around, many employers need additional help, which is a great thing with so many people looking for work. However, be especially suspicious of any job offer that seems too good to be true, like high paying “no experience necessary” or work-at-home jobs. Many times these types of offers will lead you to signup sites that are built just to gather your personal information. And if they want a payment of any kind to send you the information on the “guaranteed” job that’s being offered, forget it, it’s a scam.
Unsolicited Offers
If you are sent an unbelievable offer, beware. Cyber criminals have been known to go as far as designing entire websites around unbelievable offers, and true to form, they will be targeting your personal information or direct access to your valid account. If at all possible, stick to retailers you know and trust. Paying a little bit more and actually getting what you purchased is far better than paying less and receiving nothing but headaches associated with identity theft and compromised accounts.
Egreetings
Be very cautious about following links contained in any egreetings, even if they look like they come from a familiar source. Many times hackers will push out malicious holiday greetings as spam to huge groups hoping to get an initial victim to open it by chance, and then attempt to steal contact lists or break into email accounts. Once hackers achieve this, they can push out more phising emails to friends and family making detection of the scam that much harder.
Hard to find Items
From PlayStations and Xboxes, to Furby Booms and Big Hugs Elmos, some gifts are in such demand that they are going to be hard to find. So when that special offer shows up in touting that one special gift still in stock, proceed with caution. Following links or actually making online purchases based on these sorts of offers can lead to problems such as bait and switch or worse. Reputable retailers don't need to advertise for incredibly popular items and won’t waste precious time and money spamming “still available” offers.
Smishing – Texts with a punch
Smishing texts employ the same tactics as phishing emails, but they come to your phone. Beware of any text asking for personal information, pin numbers, etc. Dual factor authorization - when an online company sends login information via a text is getting common, and this is another avenue for a hacker to lure unsuspecting targets into divulging their personal and/or account information. Treat texts with the same caution you use on every email you receive.
Quick cash offers
Bogus loan, credit and quick cash offers have long been hacker favorites, but with wallets and pocketbooks getting squeezed extra tight during the holidays, those offers can look more tempting than ever. Unless you are sure of the legitmacy of the offer, signing up for any type of financial account online can be highly risky. If you see an offer that really grabs your interest, verify the offer on your own, again, without using any links or phone numbers contained in the email offer. These scams are especially dangerous because setting up an online account requires you to reveal a lot of personal information, which can really expose you to identity theft and worse.
Computer Security – the basics still apply
Basic computer security is the foundation for protection against cyber threats and should be a high concern year round, but with the extra zeal with which cyber criminals attack over the holidays it’s best to kick that vigilance up an extra notch this time of year. As a friendly reminder, here is a list of 7 simple tips to help prevent malware infections that will help protect you from cyber attacks and malware infections all year through.
Your team at Global Digital Forensics wishes you and yours a happy holiday season. Stay safe and enjoy the festivities. And if the unthinkable happens and your organization experiences a cyber emergency, we have responders standing by 24/7 every day throughout the holidays. Time is critical when responding to a data breach or cyber intrusion, so don’t hesitate to call us at 1-800-868-8189.
copyright 2013 by Global Digital Forensics. All rights reserved.
7 Simple Tips to Prevent Malware Infections
There are some simple, common sense things you can do that can vastly improve your security posture and lessen the chances of a major malware infection on your system.

Antivirus Software – If you don’t have some kind of reliable antivirus software always running in the background, you should consider yourself already compromised. In fact, chances are very good that an intruder has access to your system and/or data right now. There are even free solutions like Avast and AVG which prevent many common threats, so there is absolutely no excuse to not have at least minimal protection. Whatever AV solution you use, set it up to accept automatic updates (very important) and scheduled it to run scans daily. This step alone will protect you from over 90% of the threats out there.
Beware of Phishing and Spear Phishing Emails – A phishing email looks like it comes from a well-known organization, like PayPal, Amazon, or a national bank, containing a malicious attachment or a link for you to click which will open the door to an infection, or worse. Hackers blast phishing emails to thousands or millions of email addresses hoping someone clicks. Spear phishing campaigns, on the other hand, are targeted and designed to make them much more effective against a specific organization, or even an individual. Hackers will often do extensive research to make their email very convincing, using personal or business information acquired from social networking sites like Facebook, LinkedIn and Twitter, or other publicly available information. They will usually make them look like they are coming from a trusted source, like family, friends, or internal personnel or departments. Sometimes they’ll be disguised as a notification from within the organization for an incoming fax, a scanned document, or a voicemail message, all designed to look “trustworthy” enough to entice the target to open an infected attachment or follow a link to a malicious site. The primary rule concerning email is question everything. Don’t follow links in any email to check an account or verify the “problem” you are being notified about, and don’t download and open attachments you are not absolutely sure about. And don’t be afraid to make a phone call to whoever just sent you an unexpected email to verify it came from them. But don't use the phone number included in the email - hackers set up boiler rooms to receive those calls! Look for bad English and grammar, as many of these campaigns originate in foreign countries where prosecuting offenders is much more difficult.
Pop-ups – Whenever you're browsing the web and see a pop-up message appear, exercise extreme caution: pop-ups are a favorite means of delivering viruses. Even clicking the close button or the “x” may be enough to get you into hot water. A favorite tactic of hackers is generating messages that pop up and look legitimate, such as your Flash player is out of date and needs an update, prompting you to click for the update. DON’T DO IT. And never trust a pop-up that says you’ve been infected with something and to “click here” to get rid of it. Go to the source yourself with valid URLs you are sure about. Here are some useful links to check your Flash and Java versions:
Verify Java Version
Verify Adobe Flash Player
Verify Microsoft Silverlight
Keep all software and applications up to date – A favorite exploit vector for hackers is out-of-date software. Operating systems like Windows, and popular software like Flash and Java, are in use every day on billions of systems and devices worldwide, and that’s a numbers game hackers just love to take advantage of. So when your system or software tells you an update is available, take care of it right away. And remember to beware of pop-ups informing you about updates, as discussed above!
USB Sticks/Flash Drives – Small, convenient and with tremendous storage capacity, USB storage devices are a great way for hackers to get their foot in the door and even move past air gaps to more sensitive areas within an organization. It’s a common practice for hackers to load them with a virus and then leave them laying around in smoking areas, waiting and break rooms, or even on subway or park benches, hoping someone will pick it up, plug it in and deliver the malicious payload. With a little thought and ingenuity in selecting “drop-spots,” it’s also a favorite method for hackers to target specific organizations or individuals. Never plug in any USB storage devices from questionable or unknown sources. You may just want to see what it is so you can return it, but the “reward” you may get is not anything you want. And beware of freebies and gifts. It was widely reported that at the 2013 G-20 Summit in Russia, USB devices like memory sticks and specially modified mobile phone chargers containing spyware, emblazoned with Russia’s G20 summit logo, were included in gift bags passed out to high ranking delegates. Gifts like these can keep on giving – your data to hackers.
Web Habits – Some common sense goes a long way. Illegal download sites for software, games, music and movies are notorious conduits for hackers to deliver viruses and other dangerous malware, so always consider the source. If you have doubts, run a check on the URL to see a little of their history. We've even made a handy tool for you to use.
Passwords – Using the same password for everything is a very dangerous habit, and unfortunately, an all too common practice that hackers rely upon. Create strong passwords (a mix of letters, different case, numbers and special characters) and change them regularly. Using the same password(s) for many things makes it easy for a hacker to turn one stolen password into a skeleton key of sorts, allowing them to compromise a target on multiple fronts.
Bigger problems?
Following these seven simple tips will get you off to a great start to protecting your network and your valuable data, but it still won’t mean you are safe from every kind of threat out there. If you suspect your system is compromised, or if you'd like more information, contact Global Digital Forensics at 1 (800) 868-8189, or use the contact us link below:
copyright 2013 by Global Digital Forensics. All rights reserved.

IS BADBIOS A CYBER SECURITY GAME-CHANGER?
In the world of cyber threats, evolution can be a fierce enemy, especially when threats make a such a huge leap that the cyber security game ends up being changed forever. That’s when evolution becomes a revolution, and every IT security professional hoping to remain standing is going to eventually be sucked in, like it or not. It’s happened before (Stuxnet quickly comes to mind), and it will happen again. So when I see anything with even a glimmer of that kind of potential, I feel compelled to do whatever I can to help get it on the radar of as many security professionals as possible. And after looking into badBIOS, first brought to light by known and respected cyber security researcher Dragos Ruiu, that glimmer of potential certainly caught my eye and bears watching.
Is badBIOS the new Bad Boy on the Block?
What makes badBIOS score so high on my potential danger scale is that it could directly impact one of the most relied upon methods used today for shielding critical systems and data to drastically reduce the risk of compromise – air gaps – the practice of physically separating systems so there is no tangible connection which could be used as a springboard for malware to propagate. badBIOS seems to have the ability to circumvent that protection though, allowing systems (and malware) to communicate with each other even when unplugged from every physical connection, including a power cord plugged into the wall, and disabling and/or removing any Wi-Fi and Bluetooth capabilities. Imagine the large scale implications on critical infrastructure and SCADA systems that often rely on air-gaps as a main line of defense. To me, it’s a terrifying thought.
Fact or Fiction? Time Will Tell
So for three years Ruiu has been trying to find the answer to the mystery that befuddled him since he first noticed that malware was being introduced and communicating with systems that were not connected in any traditional way. So he reported it, and started his own quest to find the truth. But as often happens, most of the cyber security world just filed it away as more science fiction that’s just not possible. But as the microwave oven in your kitchen and the 20th century military super-computer that now doubles as a phone in your pocket can attest, sometimes science fiction has a way of making the leap to science fact. And with what would be at stake in the real world we live in today, even the possibility of that being the case should merit further scrutiny in data security circles.
That Sound You Don’t Hear Could be the Answer
So how does Ruiu think this mysterious connection is taking place? Right now all signs are pointing to the possibility that inaudible high frequency sounds transmitted from the speakers of one system are being picked up from the microphone of the other and translated by the malware present on each. It’s not hard to imagine digital information being transmitted this way, just think about logging on to the Internet years ago and listening to the screeching howl of the modem as it was trying to connect - same idea, but bigger, stronger, faster and silent to human ears. In a practical sense, it would mean if a hacker could get that malware on the systems on both sides of the air gap, they would just talk up a storm. Then all the hacker would have to do is simply glean the conversation from the system connected to the outside, or introduce their own conversation to the connected system which would relay it to the one on the other side of the air gap. It’s so simple it’s brilliant, not to mention powerful and dangerous on so many levels.
The Malware Still Needs to be Delivered
The one saving grace I see is that in some form or fashion the malware still needs to be initially delivered to the systems on both sides. For the connected system, that could come in a host of forms we are all too familiar with, like emails with infected attachments, malicious sites, or what is often the culprit with malware that makes it past the air gap, USB storage devices. USB sticks have always been a favorite for this purpose. The tendency to rely on USB devices to update and/or synchronize systems on the other side of the gap is all too common, and something we have long focused on when we do network vulnerability assessments and penetration tests for clients. Thankfully, it looks like guarding against that practice may also be a main weakness of badBIOS, because the introduction of data from a USB device seems to be the one constant in the mystery. The malware goes as far as disabling the ability to boot from external devices, and can even brick USB devices so they unreadable until they are reintroduced to an infected system, then they mysteriously work again, which both show a concerted effort on the part of the malware designers to force the user into the direction they want them to go. I look forward to the next phase of his testing where more advanced forensics will be performed on what exactly is happening on that level.
Standing Still Only Gets You Left Behind
It will take more study and industry scrutiny before the final verdict is in on badBIOS, but if there is one point I hope to get across, it’s this; malware will always continue to evolve. If you are tasked with the security of data and digital assets, one eye always has to be looking ahead. Read and consume all the information about the latest trends and developments that you can. While many times new “revelations” will turn out to be nothing but smoke, they can still make you see things in a different light, and sometimes that is enough to make a connection to dangers you’ve never even considered before. Because like Sherlock Holmes, or Mr. Spock, depending on your generation, if you eliminate all other possibilities, whatever remains can lead you to the truth.
*Joe Caruso is the founder and CEO/CTO of Global Digital Forensics, a premier provider of cyber security solutions since the infancy of the Internet.
Traditional discovery was an endeavor fraught with no small amount of peril: what if something was lost, concealed, destroyed or (even if produced) just plain missed? The lurking danger of a damaging “needle in the haystack” was a constant concern.
At the dawn of the age of electronic discovery, Electronically Stored Information (“ESI”) offered a new hope: the opportunity to “freeze” the evidence in time (in the form of a single computer hard drive) and methodically sift through all of the information on the hard drive.
Because data collection for a single machine (or each machine at issue) could be documented and the results recorded and repeated, the field of electronic discovery began to take on the look of a computer forensics operation. Relevant information (even if “deleted”) was difficult to conceal and as a result, even the location of data on a hard drive could give counsel a valuable window into what the data meant to the opposing party. Forensic soundness mattered. Forensically sound data would hold a wealth of information which could be used to tell an enlightening story about the data and what had been done to it, unlocking revealing answers, or at the very least, better questions.
One key rule in computer forensics is, it can be difficult, if not impossible, to prove who was at a computer keyboard at any given time. However, with this rule in mind, the application of computer forensics principles to the collection and review of ESI provided an unprecedented level of information, insight and evidence to litigators.
At last, there was cause to rejoice: it was now harder than ever before for a party to actively conceal the sort of information that could blow a case wide open. Computers were poised to provide counsel with incontrovertible evidence, as long as a human could review all the information and find the needle hiding in the haystack.
These miraculous gains, however, unleashed a new beast to tame: the sheer volume of data.
As most people around the world have access to electronic devices, the amount of ESI that might fit squarely into a discovery request has increased geometrically, with no end in sight.
As attractive as the computer forensic discovery model was for electronic discovery where an adversary’s ESI might consist of a few desktop computers, each with a 40 GB hard drive, that same model becomes logistically and fiscally crushing when the corpus of data exceeds several terabytes of information stored on a company’s server(s), computers, laptops, smart phones and tablets.
While an attorney might have argued that the safest and best practice would be to image the entire corpus of an adversary’s data, the prospect of imaging all of that data in 2012 has ceased to make sense. It is also worth noting that the “image it all” strategy is arguably a defense against claims of legal malpractice, but the era of this sort of “defensive discovery” has ended due to the volumes of data involved.
In short, computer forensics as we knew it in the first decade of the 21st Century is eyeing extinction. It is also an inexorable truth that electronic discovery based on this same forensic model will also not long survive.
So What Does it All Mean?
First, the good news: electronic discovery, overall, is likely to get cheaper. The bad news is that the cost reduction is a direct result of the loss of traditional notions of forensic soundness.
It is, however, important to note that forensic soundness is not synonymous with evidentiary quality and the two concepts are not (and never have been) mutually exclusive.
Arguably, the application of the strictest standards of forensic soundness did not add to the quality of the data recovered, even though these standards ALWAYS increased the price per gigabyte for all of the data recovered, processed and reviewed. Forensic acquisition was a “one size fits all” approach to discovery that certainly provided certain standards and safeguards, but did so at a significant, and often unnecessary, cost to the client.
What the current state of ESI really means is a return to “old school” discovery, a form much more akin to what discovery was before.
The days of isolating gigabytes of information and then sifting through all of the dates with a search tool are over. The amount of data at issue, even in small commercial cases, is simply often too large to justify a forensic collection of absolutely all of the data.
Is Paradise Lost?
In a word, “No,” paradise is not lost. While a forensically sound and complete hard disk image provided a wealth of information, alternate paths to some of the same results do still exist. The methodology is the same as that which was employed before electronic discovery, back when production was done on paper.
Don’t Image Everything
With very few exceptions, forensic imaging of an entire corpus of a client’s data is unnecessary and prohibitively expensive, often running into the hundreds of dollars per gigabyte for imaging, processing (like de-duping and near de-duping) and conversion. An adequate response to discovery can be achieved by means of a close review of a client’s systems along with an agreed upon strategy formulated with the client’s IT department/computer consultant.
Does Remote Access make things “Cloudy?”
Recalling that the traditional computer forensics acquisition paradigm, one of the key processes to forensic soundness involved isolating the target computer, powering it down (or, it if was off, not turning it on) and removing the hard drive from the computer in order to make a forensic image with a read-only device. The dates, times, number, kind and character of the files were thereby preserved, and the discovery process could then shift to reviewing the results of the acquisition and determining “what you had” as a result of the operation. The hard drive was, at first, a black box, but once imaged, it revealed its secrets from a point which the forensic technician had frozen in time.
This static acquisition is as quaint a notion as a stroll down a main street full of small shops and Model T Fords. Remote access, cloud computing, has eliminated static acquisitions, but it has not destroyed the evidence necessary to a successful litigation, just altered the way we must acquire it.
Does remote access make things “cloudy?”
The answer to this question is the same as the answer to most clients’ questions: it depends.
Cloud Computing
A brief word about cloud computing: it’s here and it’s not going away. The convenience of remotely accessing data, for work, or for entertainment, is eminently appealing. Cloud computing provides the ease and portability that have come to define the Internet era.
In support of this new computing frontier, service providers have built a “brick and mortar” (or “aluminum and plastic”) physical infrastructure to support cloud computing. While the user can travel light, the provider has a large, heavy footprint.
Modern server farms and datacenters are constructed as secure facilities with redundant electronic assets and fire suppression/safety systems. In essence, a server farm is run like a bank, but instead of money, the facility safeguards data.
It is this bank comparison which has finally allowed some attorneys to counsel their clients (or allow themselves) to utilize cloud computing. The traditional concerns about not having control of one’s data are allayed when the comparison is made to placing one’s money in the bank, as opposed to stashing it in one’s mattress. A loss can occur in either scenario, but the valuable asset is better protected and insured by the professional custodian as opposed to a data owner’s often inadequate do-it-yourself approach.
Bearing all this in mind, cloud computing necessarily translates into a certain level of uncertainty when it comes to the provenance of a quantum of data. Unlike the file pulled from a forensically isolated hard drive, the issue of alteration or authenticity does loom. Securing adequate answers as to the provenance of data weighs heavily on the system in use. Some cloud based systems maintain detailed logs regarding access, as well as copies of subsequent versions of a file/document. In this case, the provenance of the data is as good and as reliable as the logs.
If the Cloud Service Provider (“CSP”) is reputable, the logs will be both complete and accurate. While a litigant might argue that the logs could be manipulated, this sort of conspiracy theory seems a remote possibility in light of the larger issues at stake, after all, why would a service provider endanger its reputation with current and potential clients for the limited benefit of one client in one case? The need for digital integrity and the threat of negative consequences in the absence of digital integrity provide ample incentive for CSPs to be as reliable as any other custodian of records or valuables.
Discovery Methodology under the Cloud
ESI produced from cloud based storage may (or may not) contain the same metadata it had when it was created and then uploaded to the cloud. The key factors in determining the state of metadata is the system and software being used and the access records maintained by the CSP.
Depending on the type of cloud, public or private, and the configurations on the backend server (or servers), metadata in the traditional sense may not exist. However, it is the job of the technical experts to determine what "metadata" does in fact exist. Big players, like Google, have introduced Message Vault, an integrated electronic discovery (ediscovery) layer, and Microsoft 360 has had ediscovery-centric features since its introduction. However, this is a far cry from what we traditionally understand as metadata and there are literally tens of thousands of cloud based storage options, SaaS (Software as a Service) and web applications that are used by business today, these are the unknowns that experts are accustomed to and must handle every day.
From a planning perspective, it would be wise for organizations to fully understand the capabilities of cloud providers and find out what is, and what is not, available from both a security and ediscovery perspective, so they are prepared to facilitate producing documents when required.
Applying Old Lessons to a New World
Perhaps one of the greatest tributes to our legal system is the timeless quality of some of our basic rules and practices: perjury is so corrosive to the fact finding process it’s one of the Ten Commandments. Hearsay is inherently unreliable since it does not allow for cross examination. There are some concepts, such as these, that work, in any time and any season. In this same spirit, working with ESI from the cloud should follow the same sound principles of evidence that have always applied. In the absence of a forensically “frozen” corpus of data, the validity, admissibility and evidentiary quality of data can still be asserted, or assailed, based upon a cogent analysis of the facts and circumstances surrounding that data. This is the same calculus in which lawyers have engaged, quite literally, for centuries. In this regard, everything old is new again, and that’s an ironclad grasp that even cloud computing can’t escape. The trick is finding the right experts with the right expertise to help you successfully negotiate the many potential perils of ediscovery in the cloud.
This article written and submitted July 17, 2012, by:
Michael P. Reynolds, JD - President of Michael P. Reynolds, PC
Contact Information:
(347) 433-6068 (v)
(516) 750-9028 (f)
